1200 specifications
Lucent Technologies 1200 is a cutting-edge telecommunications equipment designed to enhance communication networks in a variety of settings. Introduced during the late 20th century as part of the company's portfolio of advanced networking solutions, the Lucent 1200 series integrated various technologies to optimize performance and support a broad range of applications.One of the primary features of the Lucent Technologies 1200 is its robust modular design, which allows for easy upgrades and customization to fit specific needs. This scalability is particularly valuable in environments where traffic demands can vary significantly, such as in corporations, educational institutions, and governmental agencies. By accommodating different modules, including voice, data, and multimedia interfaces, the system can evolve alongside technological advancements and user requirements.
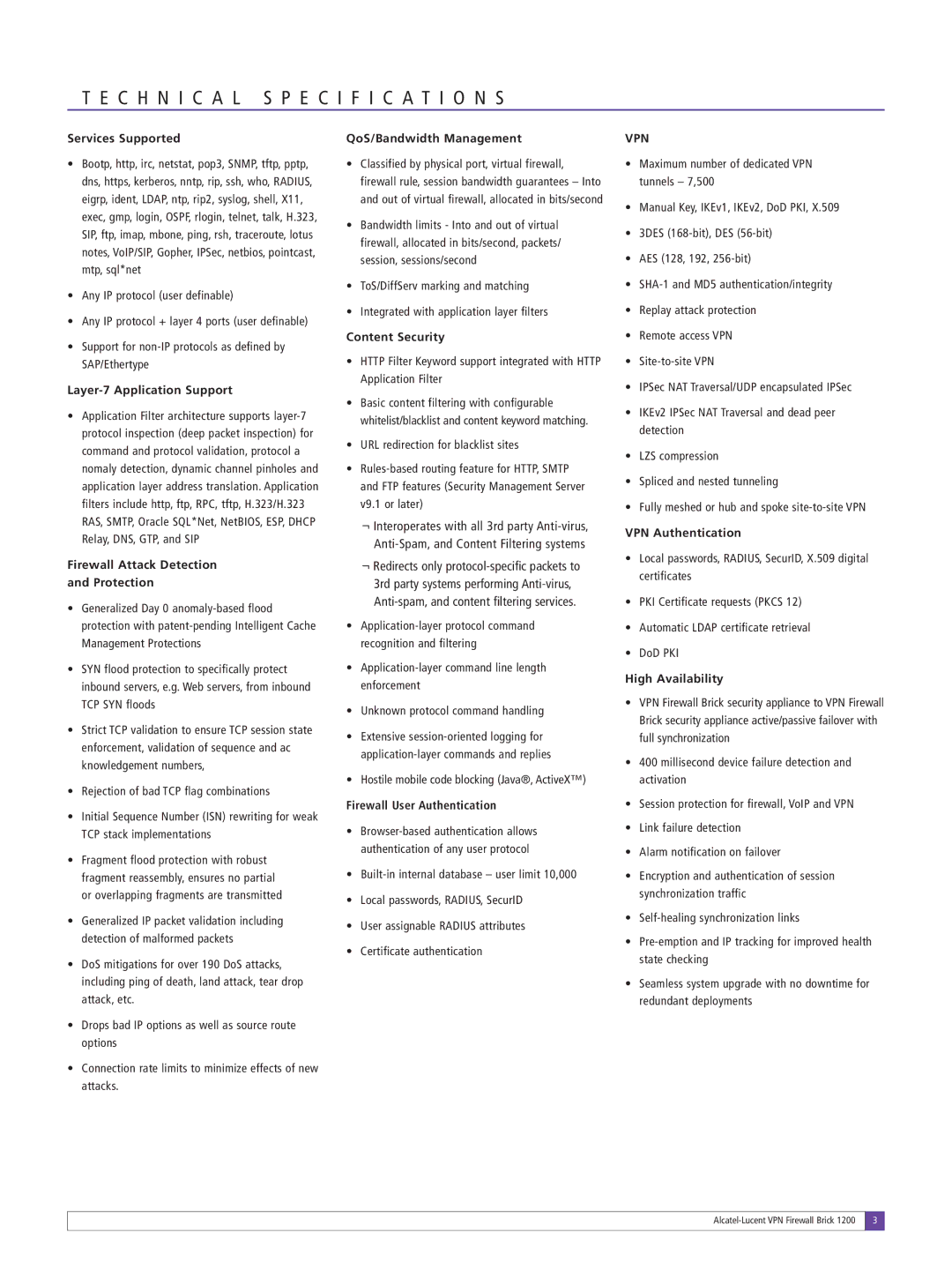
Another critical characteristic of the Lucent 1200 is its high-capacity processing capabilities. Designed to handle a substantial amount of simultaneous connections, the system employs advanced algorithms to manage bandwidth efficiently, ensuring minimal latency during peak usage times. This capability is essential for supporting applications that require real-time communication, such as video conferencing and VoIP services, which have become increasingly prevalent.
The Lucent Technologies 1200 also places a strong emphasis on reliability and redundancy. Incorporating fault tolerance mechanisms, the system can continue operating seamlessly in the event of hardware failures or network disruptions. This reliability is crucial for businesses that depend on uninterrupted communication for their operations, helping to mitigate potential financial setbacks due to downtime.
Security is another vital aspect of the Lucent 1200. The system incorporates various features to safeguard against unauthorized access and ensure the integrity of transmitted data. Encryption protocols and authentication processes work together to create a secure environment for sensitive information.
Finally, user-friendly management tools accompany the Lucent Technologies 1200, enabling network administrators to monitor performance, troubleshoot issues, and configure settings with ease. These tools are designed to provide real-time insights, empowering organizations to maintain optimal network performance proactively.
In summary, the Lucent Technologies 1200 stands out in the telecommunications landscape due to its modularity, high capacity, reliability, security features, and ease of management. It serves as an indispensable solution for organizations looking to enhance their communication infrastructure and adapt to the rapidly evolving technological landscape.