Chapter 3 Software Reference
Chapter 3 - Software Reference
Config - Authentication
This tab allows you to set the security settings to match those of your AP. It is configurable only if you have set Network Authentication to WPA or WPA2 in
Authentication Type
The authentication type methods include:
PEAP: PEAP (Protected Extensible Authentication Protocol) authentication is a version of Extensible Authentication Protocol (EAP). EAP ensures mutual authentication between a wireless client and a server that resides at the network operations center.
TLS/Smart Card: TLS (Transport Layer Security) authentication is used to create an encrypted tunnel and achieve
TTLS: TTLS authentication uses certificates to authenticate the server, while maintaining similar security properties to TLS such as mutual authentication and a shared confidentiality for session WEP key.
LEAP: LEAP (Light Extensible Authentication Protocol) authentication is a version of Extensible Authentication Protocol (EAP). EAP ensures mutual authentication between a wireless client and a server that resides at the network operations center.
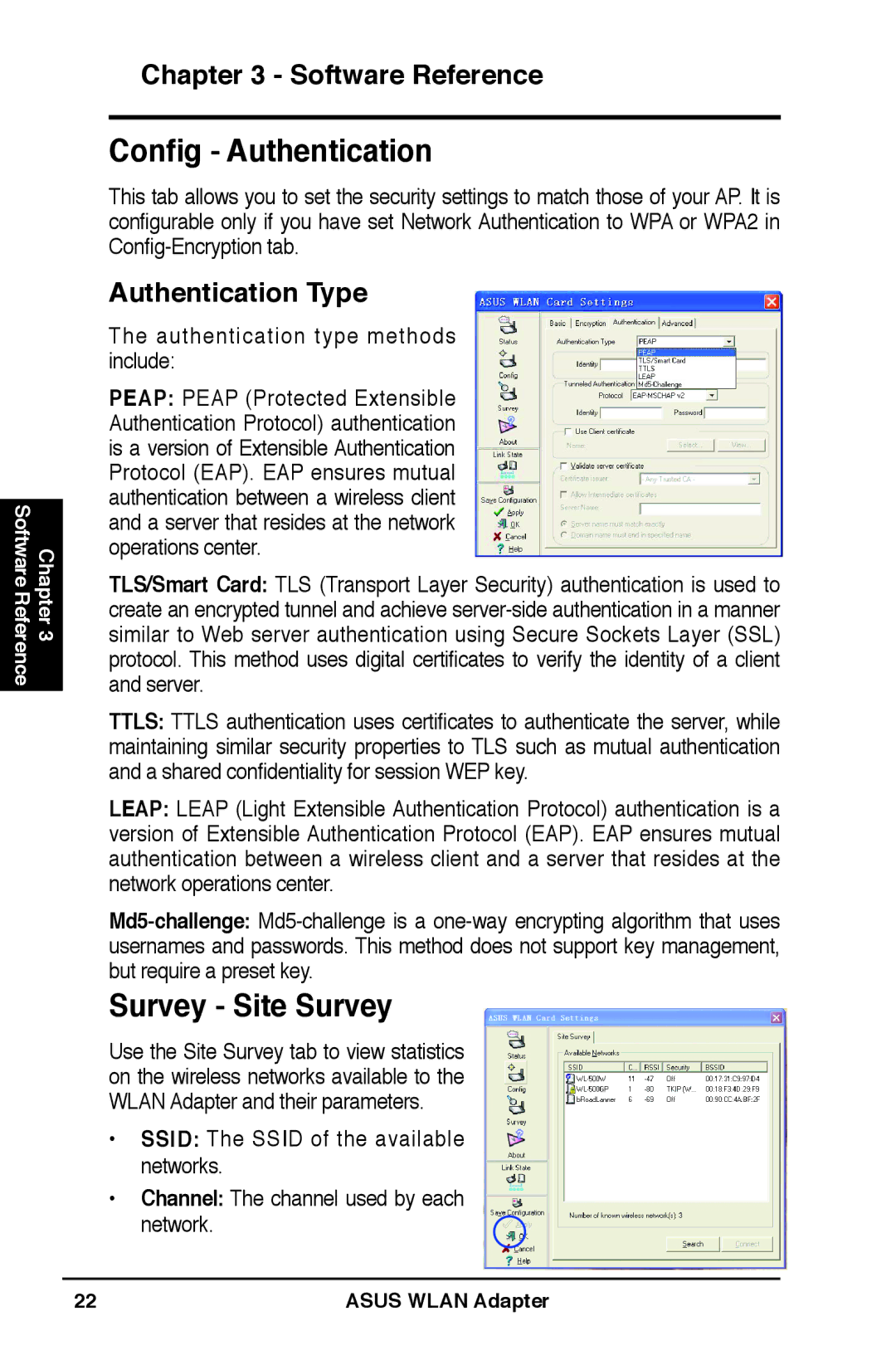
Survey - Site Survey
Use the Site Survey tab to view statistics on the wireless networks available to the WLAN Adapter and their parameters.
•SSID: The SSID of the available networks.
•Channel: The channel used by each network.
22 | ASUS WLAN Adapter |