15101 specifications
Extreme Networks 15101 is a high-performance network switch designed to deliver reliable and efficient connectivity for modern enterprise environments. As organizations increasingly embrace digital transformation, the need for robust networking solutions has become paramount. The 15101 addresses these demands by providing advanced features tailored for businesses seeking to enhance their network infrastructure.One of the standout characteristics of the Extreme Networks 15101 is its modularity. This switch offers a flexible design that allows for easy upgrades and expansions, making it suitable for various network sizes and configurations. With multiple ports available, including 10GbE and 25GbE options, the switch ensures high bandwidth availability and efficient data transmission across devices.
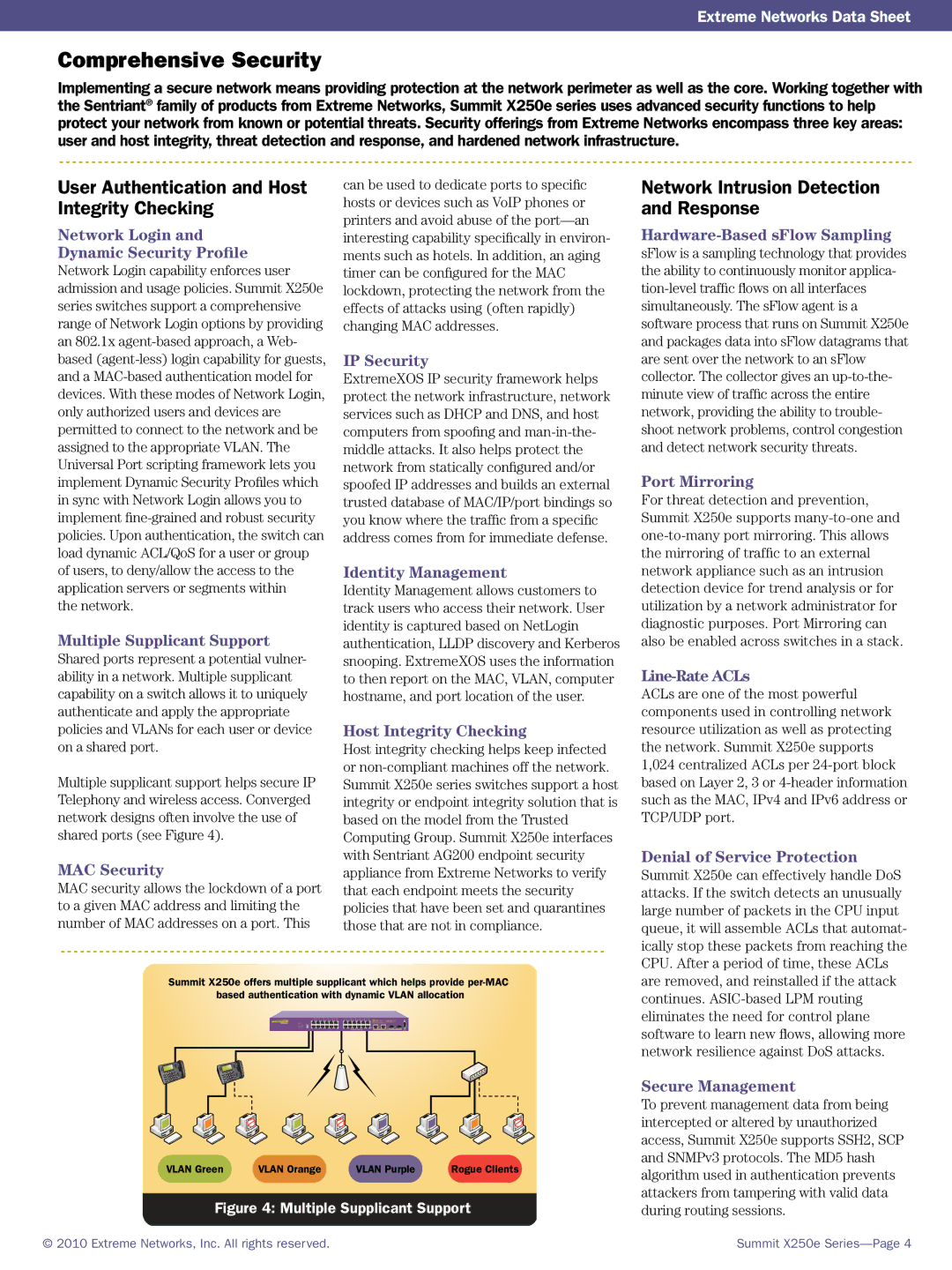
In terms of scalability, the 15101 excels with its stackable architecture. This capability allows multiple units to be interconnected, significantly increasing the total port density and minimizing management complexity. As businesses grow, the ability to scale seamlessly without overhauling the entire network infrastructure is a crucial advantage.
The 15101 also incorporates advanced technologies such as Virtual Extensible LAN (VXLAN) support, which provides enhanced network segmentation and efficient traffic management in a virtualized environment. This feature is especially beneficial for organizations leveraging cloud services and virtualization, as it allows for seamless workloads and simplified network operations.
Security is another critical aspect of the Extreme Networks 15101. The switch comes equipped with state-of-the-art security protocols, including IEEE 802.1X port-based authentication, dynamic VLAN assignment, and advanced ACLs (Access Control Lists), ensuring that the network remains secure from unauthorized access and potential threats.
In addition to security, the Extreme Networks 15101 offers robust management capabilities. The switch can be easily configured and monitored through the user-friendly ExtremeCloud management platform, which provides visibility into network performance and facilitates troubleshooting through advanced analytics and reporting.
Energy efficiency is a priority for the 15101, featuring technologies that promote low power consumption without compromising performance. This consideration not only reduces operating costs but also supports sustainability initiatives within organizations.
Overall, Extreme Networks 15101 is a versatile, high-performance switch that provides the essential features and technologies needed for modern enterprise networking. With its modular design, scalability, security features, and ease of management, it stands out as an ideal solution for businesses looking to future-proof their network infrastructure while enhancing performance and reliability.