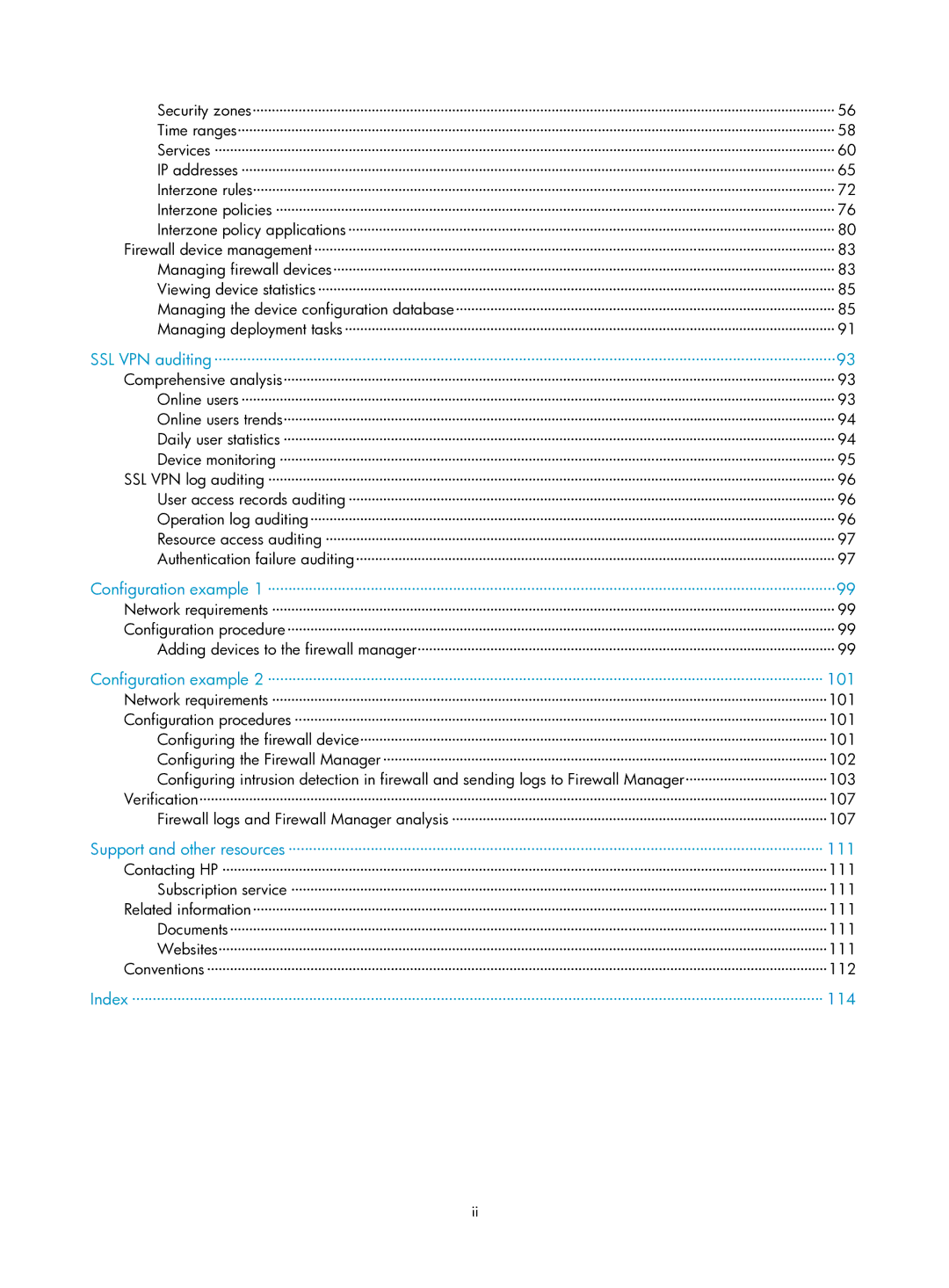
Security zones························································································································································ 56 Time ranges···························································································································································· 58 Services ·································································································································································· 60 IP addresses ··························································································································································· 65 Interzone rules························································································································································ 72 Interzone policies ·················································································································································· 76 Interzone policy applications ······························································································································· 80
Firewall device management········································································································································ 83 Managing firewall devices··································································································································· 83 Viewing device statistics······································································································································· 85 Managing the device configuration database··································································································· 85 Managing deployment tasks································································································································ 91
SSL VPN auditing·······················································································································································93
Comprehensive analysis················································································································································ 93 Online users ··························································································································································· 93 Online users trends················································································································································ 94 Daily user statistics ················································································································································ 94 Device monitoring ················································································································································· 95
SSL VPN log auditing ···················································································································································· 96 User access records auditing ······························································································································· 96 Operation log auditing········································································································································· 96 Resource access auditing ····································································································································· 97 Authentication failure auditing····························································································································· 97
Configuration example 1 ··········································································································································99
Network requirements ··················································································································································· 99 Configuration procedure··············································································································································· 99 Adding devices to the firewall manager············································································································· 99
Configuration example 2 ······································································································································· 101
Network requirements ·················································································································································101
Configuration procedures ···········································································································································101
Configuring the firewall device··························································································································101 Configuring the Firewall Manager ····················································································································102
Configuring intrusion detection in firewall and sending logs to Firewall Manager·····································103 Verification····································································································································································107 Firewall logs and Firewall Manager analysis ··································································································107
Support and other resources ·································································································································· 111
Contacting HP ······························································································································································111
Subscription service ············································································································································111
Related information······················································································································································111 Documents····························································································································································111 Websites·······························································································································································111 Conventions ··································································································································································112
Index ········································································································································································ 114