|
|
| Prestige 964 Cable Router | |
|
|
|
|
|
|
| log on. DHCP centralizes IP address management on central computers that run the DHCP server | ||
|
|
| program. DHCP leases addresses for a period of time which means that addresses are made |
|
|
|
| available to assign to other systems. |
|
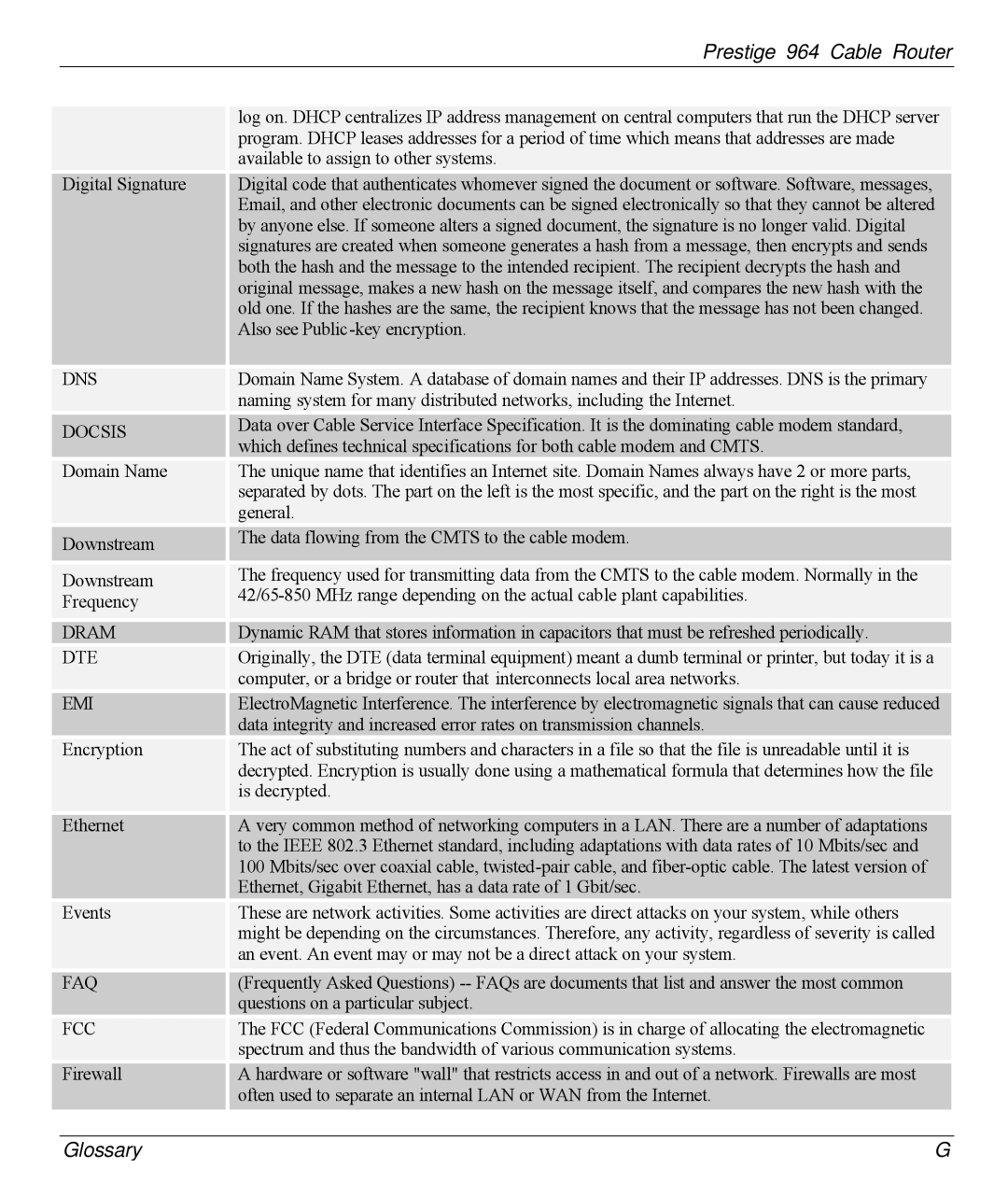
| Digital Signature |
| Digital code that authenticates whomever signed the document or software. Software, messages, | |
|
|
| Email, and other electronic documents can be signed electronically so that they cannot be altered | |
by anyone else. If someone alters a signed document, the signature is no longer valid. Digital signatures are created when someone generates a hash from a message, then encrypts and sends both the hash and the message to the intended recipient. The recipient decrypts the hash and original message, makes a new hash on the message itself, and compares the new hash with the old one. If the hashes are the same, the recipient knows that the message has not been changed. Also see Public
DNS
DOCSIS
Domain Name
Downstream
Downstream Frequency
 DRAM
DRAM
DTE
EMI
Encryption
Ethernet
Events
FAQ
FCC
Firewall
Domain Name System. A database of domain names and their IP addresses. DNS is the primary naming system for many distributed networks, including the Internet.
Data over Cable Service Interface Specification. It is the dominating cable modem standard, which defines technical specifications for both cable modem and CMTS.
The unique name that identifies an Internet site. Domain Names always have 2 or more parts, separated by dots. The part on the left is the most specific, and the part on the right is the most general.
The data flowing from the CMTS to the cable modem.
The frequency used for transmitting data from the CMTS to the cable modem. Normally in the
![]()
![]() Dynamic RAM that stores information in capacitors that must be refreshed periodically.
Dynamic RAM that stores information in capacitors that must be refreshed periodically.
Originally, the DTE (data terminal equipment) meant a dumb terminal or printer, but today it is a computer, or a bridge or router that interconnects local area networks.
ElectroMagnetic Interference. The interference by electromagnetic signals that can cause reduced data integrity and increased error rates on transmission channels.
The act of substituting numbers and characters in a file so that the file is unreadable until it is decrypted. Encryption is usually done using a mathematical formula that determines how the file is decrypted.
A very common method of networking computers in a LAN. There are a number of adaptations to the IEEE 802.3 Ethernet standard, including adaptations with data rates of 10 Mbits/sec and 100 Mbits/sec over coaxial cable,
These are network activities. Some activities are direct attacks on your system, while others might be depending on the circumstances. Therefore, any activity, regardless of severity is called an event. An event may or may not be a direct attack on your system.
(Frequently Asked Questions)
The FCC (Federal Communications Commission) is in charge of allocating the electromagnetic spectrum and thus the bandwidth of various communication systems.
A hardware or software "wall" that restricts access in and out of a network. Firewalls are most often used to separate an internal LAN or WAN from the Internet.
Glossary | G |