Embedded Web System User Guide
Copyright & Trademarks FCC Statement
Table of Contents
Defining Access Profiles
Configuring Authentication Methods
Defining Authentication Profiles
Mapping Authentication Profiles
Configuring the Classic STP Defining STP Properties
Configuring Garp
Configuring Multicast Forwarding
Defining Gvrp
Advanced QoS Mode
Basic QoS Mode
Configuration Download
Configuration Upload
Glossary
Viewing Statistics
Guide Overview
Preface
Intended Audience
Starting the TP-Link Embedded Web Interface
Getting Started
Understanding the TP-Link Embedded Web Interface
Click . The TP-Link Embedded Web Interface Home Page opens
Interface Components
TP-Link Web Interface Configuration Management Buttons
Using the TP-Link Embedded Web Interface Management Buttons
Device Representation
TP-Link Web Interface Information Buttons
Deleting Configuration Information
Using Screen and Table Options
Adding Configuration Information
Modifying Configuration Information
Click System General Reset. The Reset Page opens
Resetting the Device
Logging Off from the Device
Click . a confirmation message is displayed
System Description
Defining Device Information
Configuring Daylight Savings Time
Setting the System Time
System Information Time
Daylight Savings
Recurring
Define the Date, Local Time and Time Zone Offset fields
Sntp Overview
Configuring Sntp
Polling for Unicast Time Information
Polling for Anycast Time Information
Defining Sntp Global Settings
Configuring Sntp Authentication
Sntp Properties Page contains the following fields
Sntp Authentication Page contains the following fields
To configure Sntp authentication
Check the Enable Sntp Authentication checkbox
Click . The Add Sntp Authentication Page opens
Click . The Sntp Server is added, and the device is updated
Defining Sntp Interface Settings
Sntp Servers Page contains the following fields
Click . The Add Sntp Server Page opens
Check the Receive Server Updates option
Sntp Interface Settings Page contains the following fields
Click . The Add Sntp Interface Page opens
Select the Interface
Defining General Log Properties
Configuring System Logs
Following table lists the log severity levels
System Log Severity Levels
Viewing Memory Logs
Viewing Flash Logs
Severity
Defining System Log Servers
To view Flash memory logs
Click . The Add Syslog Server Page opens
Add Syslog Server
Click . The Log server is defined and the device is updated
Configuring Management Security
Configuring Device Security
Configuring Authentication Methods
Defining Access Profiles
Click . The Add Access Profile Page opens
Access Profile
Profile Rules
Defining Profile Rules
Defining Authentication Profiles
Click . The Profile Rule Settings Page opens
Authentication Profiles Page provides the following
Click . The Add Authentication Profile Page opens
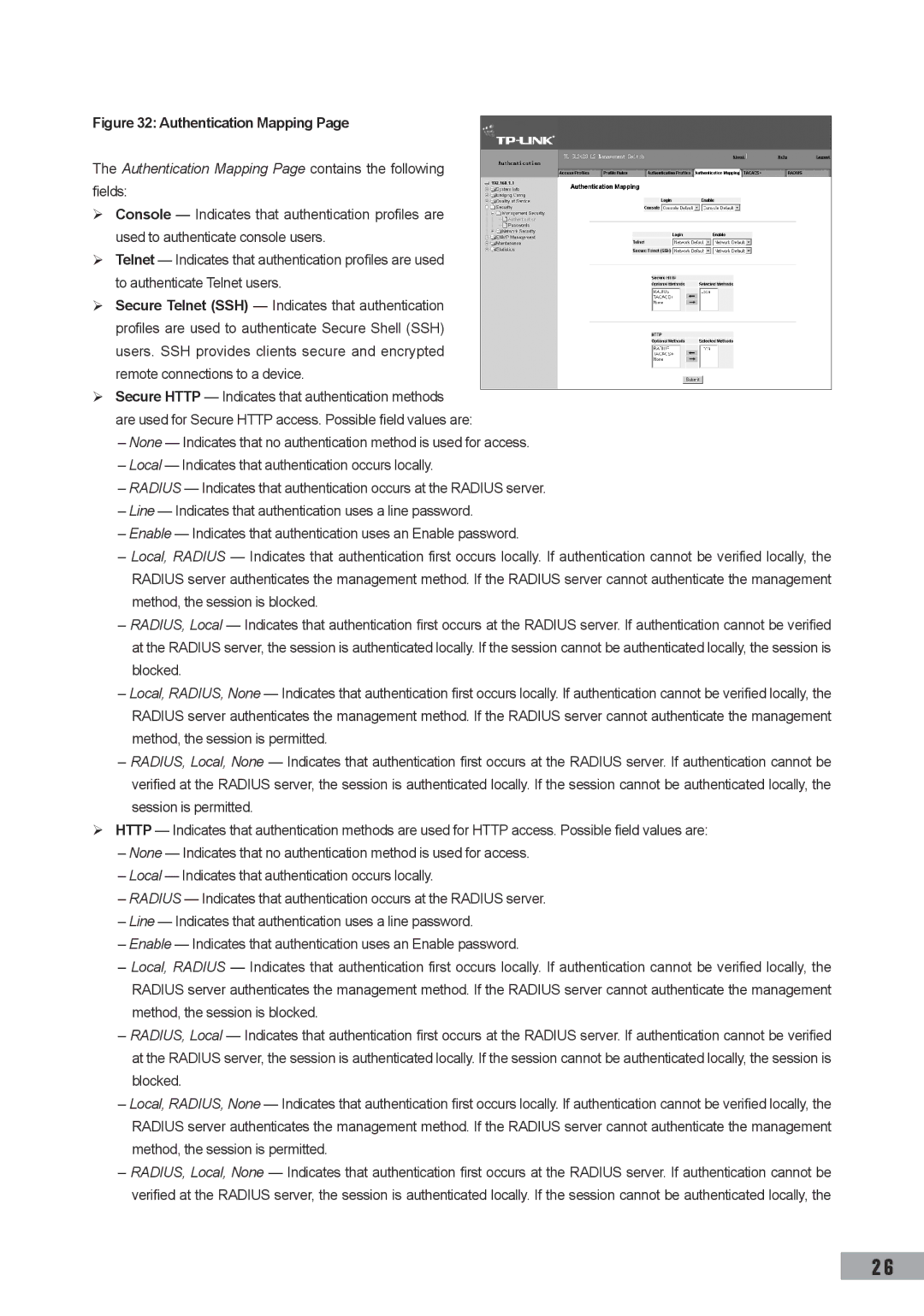
Mapping Authentication Profiles
Click . The Authentication Profile Settings Page opens
Define the Profile Method and enter the Profile Name fields
Authentication Mapping Page contains the following fields
Authentication Mapping
To define TACACS+ authentication settings
Defining TACACS+ Host Settings
Session is permitted
Define the Console, Telnet, and Secure Telnet SSH fields
Click . The TACACS+ Host Settings Page opens
Defining Radius Server Settings
Click . The Add TACACS+ Host Page opens
Select TACACS+ server entry
Click . The Add Radius Server Page opens
Radius
Click . The Radius Server Settings Page opens
Configuring Passwords
Defining Local Users
Click . The Add Local User Page opens
Defining Line Passwords
Configuring Network Security
Defining Enable Passwords
Line Password Page contains the following fields
Port-Based Authentication
Defining Network Authentication Properties
Advanced Port-Based Authentication
Network Security Overview
Port Authentication Page contains the following fields
Defining Port Authentication Properties
Click . The Port Authentication Settings Page opens
Configuring Multiple Hosts
Defining Authentication Hosts
Click . The Multiple Host Settings Page opens
To define authenticated users
Managing Port Security
Configuring Traffic Control
Enabling Storm Control
Click . The Port Security Settings Page opens
Cast B, cast M tbd Cast M, cast tbd Cast tbd
Storm Control
Defining IP Addressing
Defining IP Addresses
Defining IP Addresses
Click . The Add IP Interface Page opens
Click . The IP Interface Settings Page opens
Defining the Default Gateway
Enter the name of the User Defined Default Gateway
Defining Dhcp Addresses
Defining ARP
To define ARP
ARP Page contains the following fields
Defining DNS Servers
Defining Domain Name System
DNS Server Page contains the following fields
Type Displays the IP address type. The possible
Host Mapping Page contains the following fields
Configuring Host Mapping
Enter the Host Name and IP Address
Add DNS Host
Configuring Ports
Configuring Interfaces
Click . The parameters are saved, and the device is updated
Interface Configuration Settings
Click . The LAG Membership Settings Page opens
Configuring LAGs
Defining LAG Members
To define LAG members
LAG Membership Settings Page contains the following fields
Configuring Lacp
Click . The Lacp Parameters Settings Page opens
Lacp Parameters Page contains the following fields
Configuring VLANs
Define the Port Priority and Lacp Timeout settings
Defining Vlan Properties
Defining Vlan Membership
Modify the Vlan Name and Disable Authentication fields
Vlan Member Properties Page contains the following fields
Click . The Vlan properties are saved
Vlan Interface Settings Page contains the following fields
Defining Vlan Interface Settings
To define Vlan membership
Vlan Member Membership Page contains the following fields
Configuring Garp
Click . The Vlan / LAG Interface Settings Page opens
Defining Garp
Defining Gvrp
Garp Parameters Page contains the following fields
To define Gvrp on the device
Gvrp Parameters
Forwarding Database Static Addresses
Configuring Static Addresses
Click . The Add Forwarding Database Page opens
Configuring Dynamic Forwarding Addresses
To define the dynamic forwarding addresses
Clear Table Clears the Current Address Table
Select an Address Table Sort Key
Select the Interface, the MAC Address, and the Vlan ID
Defining STP Properties
Configuring the Classic STP
Click System Bridging Info Spanning Tree STP
Properties. The STP Properties Page opens
Complete the Spanning Tree State and Bridge Settings fields
Defining STP Interface Settings
STP Interface Settings Page contains the following fields
Click . The STP Interface Settings Page opens
Click the STP enable checkbox Define the fields
Rstp
Configuring the Rapid STP
Configuring the Multiple STP
Click . The Rstp Settings Page opens
Defining Mstp Properties
Configuring Mstp Instances
Click . The device information is updated
Define the Region Name, Revision and Max Hops fields
Configuring Mstp Interface Settings
Configuring Mstp Vlan Instances
Mstp Vlan Instance Configuration Page opens
Mstp Interface Settings Page contains the following fields
Modify the Port Priority and Path Cost
Mstp Interface Settings
Igmp Snooping Page contains the following fields
Configuring Multicast Forwarding
Click . The Multicast Global Parameters Settings Page opens
Click the Enable Igmp Snooping Status checkbox
Defining Multicast Bridging Groups
To define multicast groups
Click . The Multicast Group Settings Page opens
Igmp Port/LAG Members Table Control Settings
Multicast group statically in the Current Row
Join a Multicast group
Defining Multicast Forward All Parameters
Port is not attached to a Multicast router or switch
Multicast Forward All Page contains the following fields
Forbidden
Snmp v1 and v2c
Snmp
Defining Snmp Security
Defining Snmp Global Parameters
Define the Local Engine ID and Use Default fields
Defining Snmp Views
Snmp Security Views Page contains the following fields
Click . The Add Snmp View Page opens
Defining Snmp Group Profiles
Click . The Snmp Group Profile Settings Page opens
Defining Snmp Group Members
Click . The Add Snmp Group Profile Page opens
Addition to the fields in the Snmp Security Group
Click . The Snmp Group Membership Settings Page opens
Membership Page, The Add Snmp Group Membership
Contains the following fields
Snmp Communities Basic Table
Defining Snmp Communities
Snmp Communities Advanced Table
Snmp Security Communities Page is divided into
Device is updated To modify Snmp Group Membership settings
Configuring Snmp Notification Settings
Defining Snmp Notification Properties
Defining Notification Filters
Defining Notification Receivers
Snmp Notification FiIter Page contains the following fields
Click . The Add Snmp Notification Filter Page opens
SNMPv1,2c Notification Recipient
SNMPv3 Notification Recipient
Snmp Notification Receiver Page c is divided into
Click . The Add Snmp Notification Receiver Page opens
Click . The Snmp Notification Receiver Settings Page opens
Configuring Quality of Service
Quality of Service Overview
Mapping to Queues
VPT Default Mapping Table
Following table contains the VPT to Queue default settings
Dscp Default Mapping Table
QoS Modes
Enabling Quality of Service
Enabling Quality of Service
Basic QoS Mode
Advanced QoS Mode
Defining Queues
CoS Settings
Mapping CoS Values to Queues
Mapping Queues
Mapping QoS Values to Queues
Scheduling
Dscp to Queue
Downloading System Files
Managing System Files
Download Type
To download system files
Uploading System Files
Configuration Download
Firmware Download
Upload Type
Activating Image Files
Configuration Upload
Copying System Files
Software Image Upload
Select Restore Configuration Factory Defaults
Select Copy Configuration
Configuring Port Mirroring
Performing Device Diagnostics
Click . The Port Mirroring Settings Page opens
To modify port mirroring settings
Viewing Integrated Cable Tests
Click the Remove checkbox for selected item, and click
Optical Transceivers Page contains the following fields
Viewing Optical Transceivers
Viewing Interface Statistics
Viewing Statistics
Viewing Device Interface Statistics
Interface Statistics Page contains the following fields
Open the Interface Statistics
Viewing Etherlike Statistics
Click . The interface statistics counters are cleared
Etherlike Statistics Page contains the following fields
Open the Etherlike Statistics
Viewing Gvrp Statistics
Viewing EAP Statistics
Managing Rmon Statistics
Open the Gvrp Statistics
Click . The Gvrp interface statistics counters are cleared
Configuring Rmon History Defining Rmon Alarms
Viewing Rmon Statistics
Rmon Statistics Page contains the following fields
Defining Rmon History Control
Configuring Rmon History
Open the Rmon Statistics
Rmon History Control Page contains the following fields
Rmon History Table Page contains the following fields
Viewing the Rmon History Table
Defining Rmon Events Control
Configuring Rmon Events
Rmon Events Control Page contains the following fields
Click . The Add Rmon Event User Page opens
Defining Rmon Alarms
Viewing the Rmon Events Logs
Click System Statistics Rmon Events.
Click . The Add Rmon Alarm User Page opens
To modify an Rmon alarm user
Click . The Edit Rmon Alarm User Page opens
103
Glossary
BootP
Boot Version
Class of Service
Backplane
Client
Duplex Mode
Collision
Combo Port
Flapping
Ethernet
Flow Control
Fragment
Ieee 802.1p
Ieee 802.1d
EEE 802.1q
Image File
Limited geographical area
Authenticates the origin of the communication
Process
Processing, as there is more information to process
Packet
Node
Policing
Port
RJ-45 Connector
RJ-11 Connector
Running Configuration
Stand-alone Mode
Telnet
Subnet Mask
Trap
Trunking
71035590