F5D8011 specifications
The Belkin F5D8011 is a wireless networking device that played a significant role in the early development of home networking solutions. As a wireless Ethernet adapter, it allows users to connect their Ethernet-only devices to a wireless network, enabling seamless internet access and file sharing among connected devices. This product exemplifies Belkin’s commitment to delivering reliable networking solutions for everyday users.One of the main features of the F5D8011 is its support for 802.11g wireless standard, which provides data transfer rates of up to 54 Mbps. This makes it suitable for various applications, including web browsing, online gaming, and streaming media. The device operates on the 2.4 GHz frequency, which is commonly used for wireless networking, ensuring compatibility with a wide range of routers and access points.
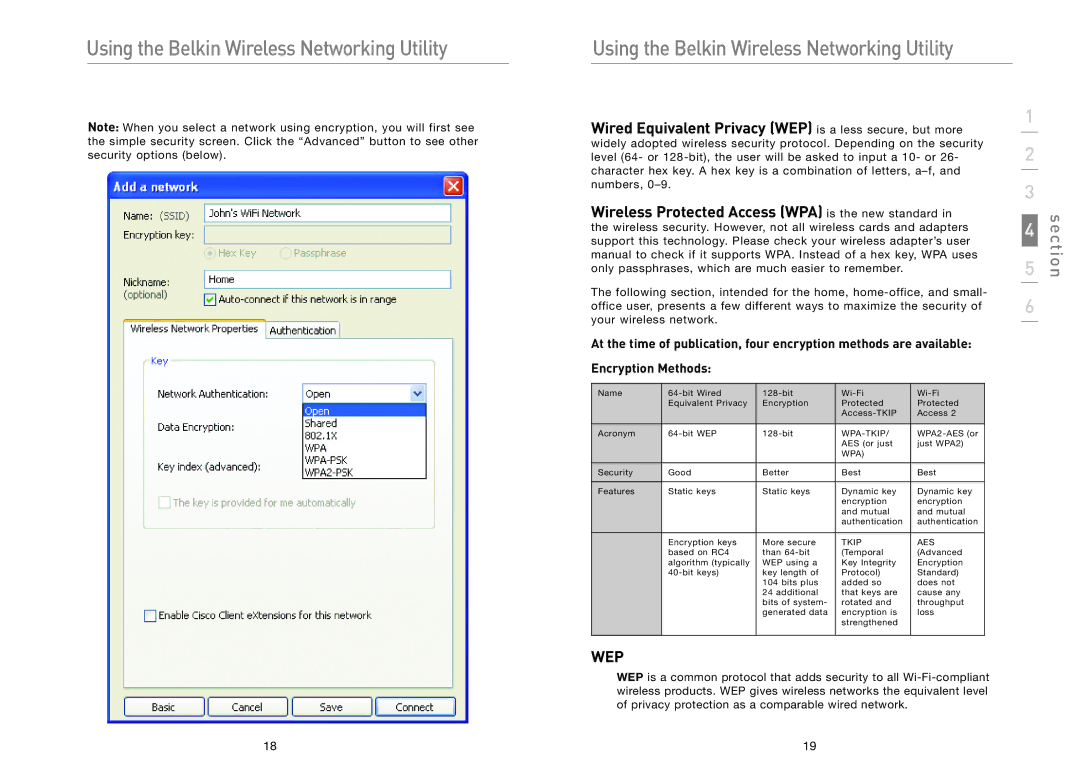
Setting up the F5D8011 is a straightforward process, thanks to its plug-and-play functionality. Users can simply connect the adapter to their Ethernet-enabled devices, such as gaming consoles, set-top boxes, or desktop computers, and establish a wireless connection with minimal effort. Additionally, the device comes equipped with advanced security features, including WPA (Wi-Fi Protected Access) and WEP (Wired Equivalent Privacy) encryption, ensuring that data transmitted over the network remains secure.
The Belkin F5D8011 also supports the use of multiple wireless clients simultaneously, allowing several devices to share the same internet connection without experiencing significant drops in performance. Its compact design makes it a convenient addition to any home or office setup, as it does not occupy much space and can be easily transported if needed.
Another noteworthy characteristic is its compatibility with a variety of operating systems, including Windows and Mac OS, which broadens its appeal among users who employ different devices. Moreover, the F5D8011 is known for its reliable connectivity and decent range, ensuring that users can maintain a stable connection even at a distance from the router.
In conclusion, the Belkin F5D8011 wireless Ethernet adapter combines ease of use, solid performance, and essential security features to provide an effective solution for connecting wired devices to a wireless network. Its design and capabilities make it a valuable asset for homes and small offices looking to maximize their networking efficiency.