Building a Security Application
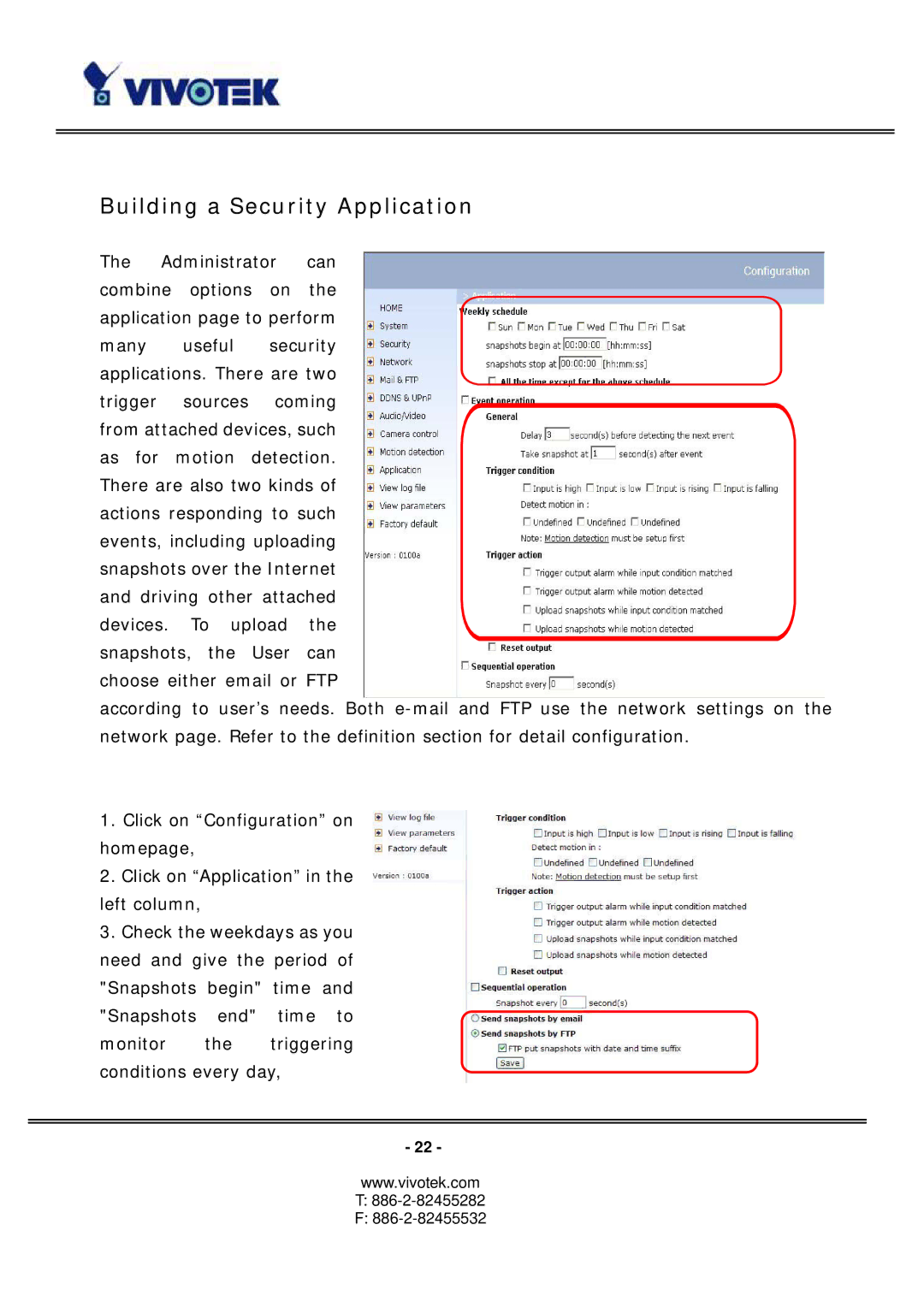
The Administrator can combine options on the application page to perform many useful security applications. There are two trigger sources coming from attached devices, such as for motion detection. There are also two kinds of actions responding to such events, including uploading snapshots over the Internet and driving other attached devices. To upload the snapshots, the User can choose either email or FTP
according to user’s needs. Both
1.Click on “Configuration” on homepage,
2.Click on “Application” in the left column,
3.Check the weekdays as you need and give the period of "Snapshots begin" time and "Snapshots end" time to monitor the triggering conditions every day,
- 22 -
www.vivotek.com