5790, 5755, 5775, 5735, 5740 specifications
The Xerox 5790, 5760, and 5765 are part of Xerox's well-known line of multifunction printers (MFPs), designed to meet the needs of businesses looking for efficient, high-volume printing, copying, and scanning solutions. These models provide a blend of advanced technology and user-friendly features, making them ideal for offices that demand speed and reliability.The Xerox 5790 is a standout model in this series, offering exceptional printing speeds of up to 90 pages per minute. It features a robust paper handling system capable of accommodating various media sizes and types, including both standard and custom formats. This model integrates advanced imaging technology, providing high-quality output with sharp text and vibrant colors, thanks to its high resolution of up to 1200 x 1200 dpi.
The 5760 and 5765 models, while slightly lower in terms of speed – with the 5765 reaching up to 65 pages per minute – still maintain impressive performance levels suitable for medium to large-sized businesses. Both devices utilize Xerox's innovative EA toner technology, which delivers fine details and smooth gradients, making them particularly effective for graphics-intensive documents.
One of the key features across these models is their user-friendly touchscreen interface, which simplifies operation and allows for seamless workflow management. Users can easily access scanning, printing, and copying functions, with options to customize workflows according to specific job requirements. Additionally, these MFPs offer advanced scanning capabilities, such as double-sided scanning and scan-to-email features, enhancing productivity.
Connectivity is another highlight of the Xerox 5790, 5760, and 5765. They support a variety of networking options, including Ethernet and Wi-Fi, making it easy to integrate them into existing office networks. Furthermore, they are equipped with mobile printing options, allowing users to print directly from their smartphones and tablets, enhancing flexibility and convenience.
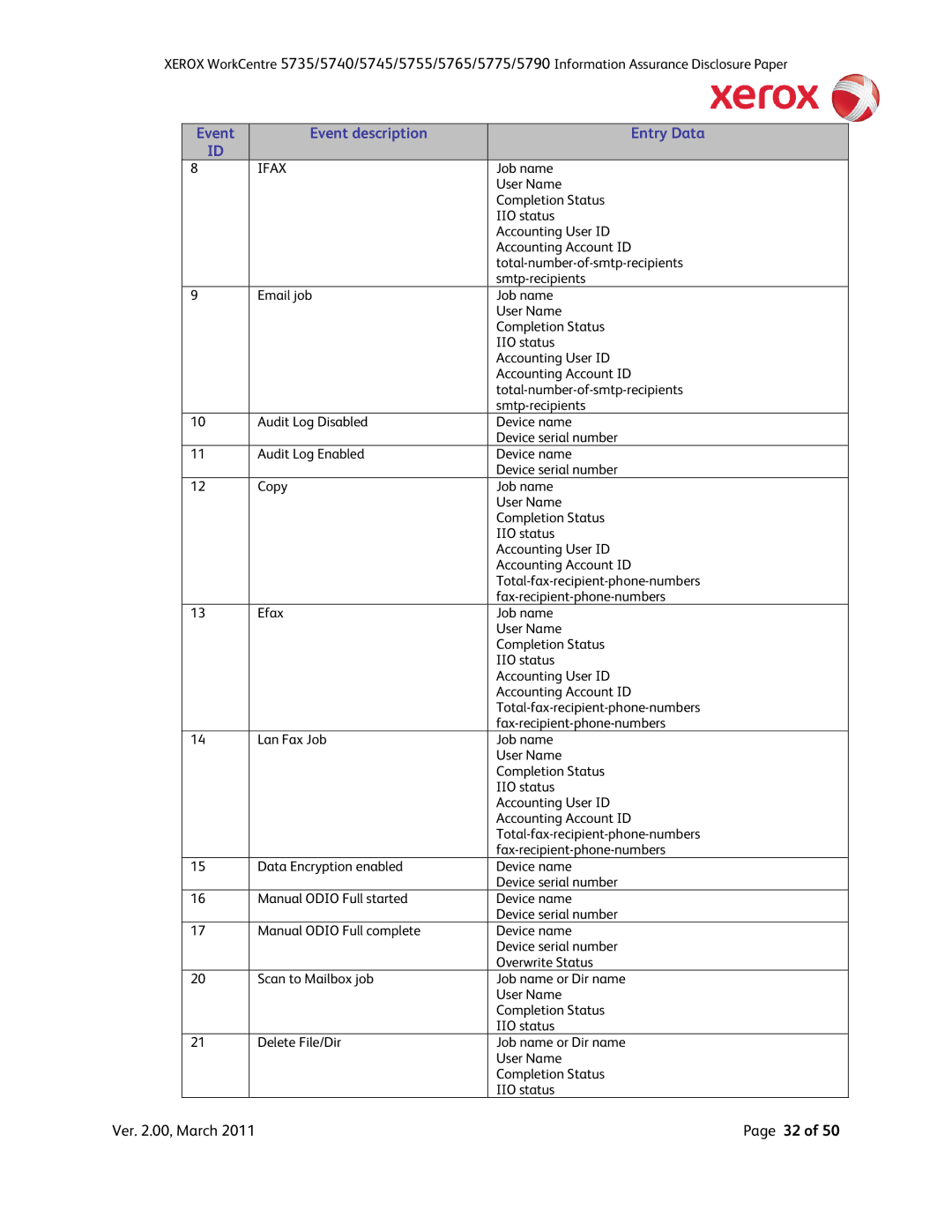
In addition to their powerful performance, these models also come equipped with various security features, such as secure print, user authentication, and data encryption, ensuring sensitive information remains protected. With their strong emphasis on sustainability, Xerox has designed these printers to be energy-efficient and equipped with features aimed at reducing paper waste, such as duplex printing.
In conclusion, the Xerox 5790, 5760, and 5765 multifunction printers combine speed, quality, and advanced technology, making them excellent choices for businesses looking to enhance productivity and workflow. Their range of features and capabilities ensures they can meet the demands of various office environments, all while maintaining a commitment to sustainability and security.