Broadband Router specifications
Edimax Technology is a well-respected name in the networking equipment industry, and their broadband routers are known for providing reliable and high-performance connectivity for both home and office environments. One of their prominent offerings is the Edimax broadband router, which features advanced technology designed to meet the demands of modern internet usage.One of the key features of Edimax routers is their support for the latest Wi-Fi standards, including IEEE 802.11ac. This technology allows for faster data transfer speeds, improved range, and higher capacity, making it ideal for streaming HD content, online gaming, and handling multiple devices simultaneously. With dual-band capability, Edimax routers can operate on both 2.4GHz and 5GHz frequencies, optimizing performance based on the type of activity. The 5GHz band is particularly useful for bandwidth-heavy operations, while the 2.4GHz band is great for devices that require longer range.
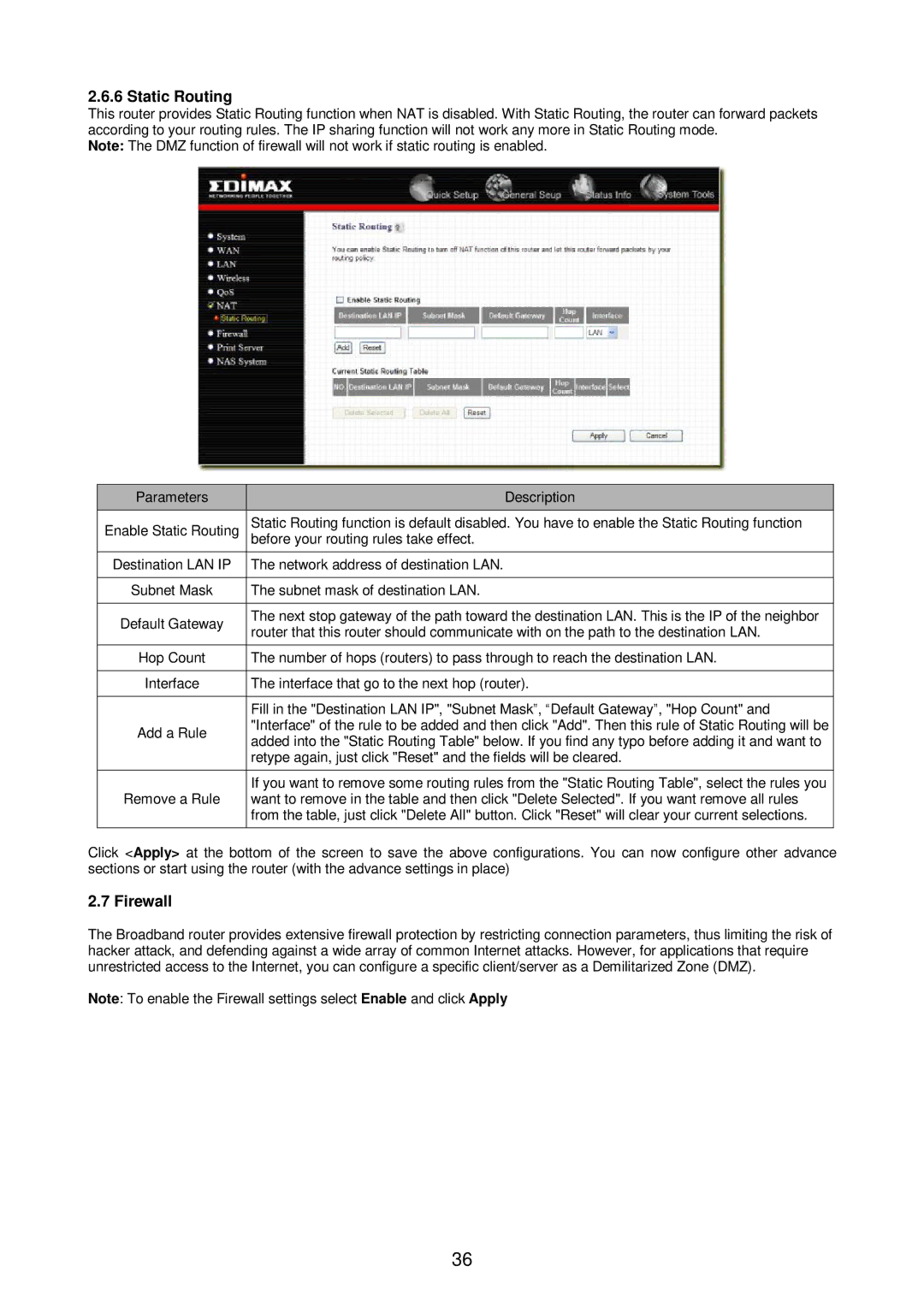
Security is a top priority for Edimax, and their broadband routers come equipped with robust security features like WPA/WPA2 encryption, ensuring that users' data remains secure from unauthorized access. Additionally, many Edimax models include a firewall, which offers an extra layer of protection against external threats.
User-friendliness is another hallmark of Edimax routers. The setup process is often quick and straightforward, with many models featuring WPS (Wi-Fi Protected Setup) for easy connection of devices. The routers may also include web management interfaces that allow users to easily configure settings, monitor network traffic, and manage connected devices.
Another noteworthy characteristic is the built-in Quality of Service (QoS) functionality. This feature prioritizes bandwidth for critical applications and devices, ensuring that activities like video conferencing and online gaming experience minimal lag and buffering.
Moreover, the design of Edimax broadband routers often reflects both aesthetic considerations and functionality, typically featuring compact forms and heat-dissipating materials to enhance durability and performance.
Finally, Edimax Technology backs its products with reliable customer support and often regular firmware updates, ensuring that users can enjoy the latest enhancements and security patches. Overall, Edimax broadband routers represent a solid blend of performance, security, and user-centric features tailored for today's internet needs.