User Guide
Export
Licensing
Contents
Upgrading the NVG Software
Snmp Agent 183
Copyright 2007-2008 Nortel Networks
Preface
Who Should Use This Book
Related documentation
VPN Gateway 6.0 Application Guide for SSL Acceleration
Product Names
How This Book Is Organized
Users Guide
Appendices
Adding User Preferences Attribute to Active Directory
Typographic Conventions
AaBbCc123
Host# telnet IP Address
How to Get Help
Getting help from the Nortel Web site
Introducing the VPN Gateway
VPN
SSL Acceleration
VPN
Hardware Platforms
Feature List
Software Features
Web Portal
Transparent Mode Access
User Authentication
User Authorization
Accounting and Auditing
Secure Service Partitioning
Client Security
Networking
Branch Office Tunnels
Portal Guard
SSL Acceleration
Scalability and Redundancy
Certificate and Key Management
Public Key Infrastructure
Hash Algorithms
Supported Key and Certificate Formats
Supported Handshake Protocols
Cipher Suites
Virtual Desktop
Secure Portable Office SPO Client
Introducing the VPN Gateway
Introducing the ASA 310-FIPS
HSM Overview
Extended Mode vs. Fips Mode
FIPS140-1 Level 3 Security
Concept of iKey Authentication
Types of iKeys
Wrap Keys for ASA 310-FIPS Clusters
Available Operations and iKeys Required
CODE-USER
HSM-SO HSM-US
Additional HSM Information
Introducing the ASA 310-FIPS
Initial Setup
Configuration is Replicated among Master NVGs
Clusters
New and Join
Clustering Over Multiple Subnets
IP Address Types
Ports
Interfaces
One-Armed Configuration
Two-Armed Configuration
Two-Armed Configuration without Application Switch
Configuration at Boot Up
Setup Menu
Step Action Choose new from the Setup menu
Installing an NVG in a New Cluster
Setting Up a One-Armed Configuration
Specify the port you want to use for network connectivity
Enter a default gateway address
Enter network mask and Vlan tag ID
Enter a Management IP address MIP
Setting Up a Two-Armed Configuration
Configure the management interface port number
Specify the host IP address for the current VPN Gateway
Specify a host IP address on the traffic public interface
Enter a default gateway address on the traffic interface
Specify a new port number for the traffic interface
Interface gateway IP address
Press Enter if correct
Complete the New Setup
Select
Enter if correct
Enter to accept
To accept
Wizard
Create the account
10.10.20.99
Enter Network mask for the pool range Creating IP pool
Settings Created by the VPN Quick Setup Wizard
Basic VPN Setup
Default Network
Default Services
Joining a VPN Gateway to an Existing Cluster
Specify the port to be used for network connectivity
Enter the VPN Gateway ’s host IP address
Step Action Choose join from the Setup menu
Enter the Management IP address MIP of the existing cluster
Accepts
Complete the Join Setup
Enter the default gateway on the traffic interface
Specify the VPN Gateway type
Wait until the Setup utility has finished
Admin user
As slave
Installing an ASA 310-FIPS
Installing an ASA 310-FIPS in a New Cluster
Use Fips or Extended Security Mode? fips/extended
HSM-SO password
HSM-SO password, or use the same HSM-SO password as for Card
Press Enter to select new
Adding an ASA 310-FIPS to an Existing Cluster
Setup Menu Join Join an existing iSD cluster New
Adding an ASA 310-FIPS to an Existing Cluster
Re-enter to confirm HSM-SO iKey has been updated
For this HSM card
Verify that CODE-SO iKey black is inserted in card
Cluster
That you used in Step
End
Reinstalling the Software
Log in as user boot, password ForgetMe
Continue y/n? y Press Enter to continue
Tag id or Enter
If correct
Restarting system Alteon WebSystems,I nc C Booting Login
Upgrading the NVG Software
Performing Minor/Major Release Upgrades
Main# boot/software/download
Enter hostname or IP address of server server host
Activating the Software Upgrade Package
Enter the host name or IP address of the server
Name or IP
At the Software Management# prompt, enter
Software Management# cur
Activate ok, relogin
Main# boot/software/cur
Here
Upgrading the NVG Software
Managing Users and Groups
User Rights and Group Membership
Adding a New User
Step Action Log in to the NVG cluster as the admin user
Access the User Menu
Add the new user and designate a user name
Assign the new user to a user group
Define a login password for the user
User# edit certadmin
Verify and apply the group assignment
Groups# /cfg/sys/user User# edit certadmin
Apply the changes
Remove the admin user from the certadmin group
User# edit admin
Verify and apply the changes
Adding Users through Radius
Login certadmin
Changing a Users Group Assignment
Step Action Log in to the NVG cluster
User admin# groups/add Enter group name certadmin
Changing a Users Password
Changing Your Own Password
Type the passwd command to change your current password
Changing Another Users Password
Type the password command to initialize the password change
Apply the changes
User# del certadmin
Deleting a User
User# list Oper Root Admin Certadmin User# apply
Certificates and Client Authentication
Generating and Submitting a CSR Using the CLI
~ ! @ # $ % * / \ ?
Apply your changes
Save the CSR to a file
Save the private key to a file
KEY----- and -----END RSA Private KEY
Open and copy the CSR
Submit the CSR to Verisign, Entrust, or any other CA
Adding Certificates to the NVG
PEM NET DER
Copy the contents of your certificate file
Copy-and-Paste Certificates
Certificate 1# apply Changes applied successfully
Copy the contents of your private key file
Paste the contents of the key file at the command prompt
Copy-and-Paste Private Key
Using TFTP/FTP/SCP/SFTP to add Certificates and Keys
Enter the desired file name
Name or IP address
Add your private key if in a separate file
End
Step Action Check the certificate numbers currently in use
Update Existing Certificate
Create a New Certificate
Add a certificate with a new certificate number
Configure a Virtual SSL Server to Require a Client Certificate
Step Action
SSL# server
Apply your settings
Main# cfg/cur ssl
Require
Generating client certificates
Enter for client certificate
Specify the validity period, key size, and serial number
Key size 512/1024 Serial number of client certificate
Main# cfg/ssl/server
Export Client Certificate
Com
Cert.pfx
Transmit Private Key and Certificate to User
Revoking Client Certificates Issued by an External CA
Managing Revocation of Client Certificates
Download and add a CRL from a TFTP/FTP/SCP/SFTP server
Crl.der
Crl.ascii
Creating Your Own Certificate Revocation List
Automatic CRL Retrieval
Http//10.42.128.30/server.crl
Main /cfg/cert 1/revoke/automatic
Info/certs command
Enter the password in the Ndic login screen Click Connect
Client certificate support
Click Connect
Signing CSRs
Paste the CSR
Main# cfg/ssl/server #/adv/sslconnect/verify/cacer
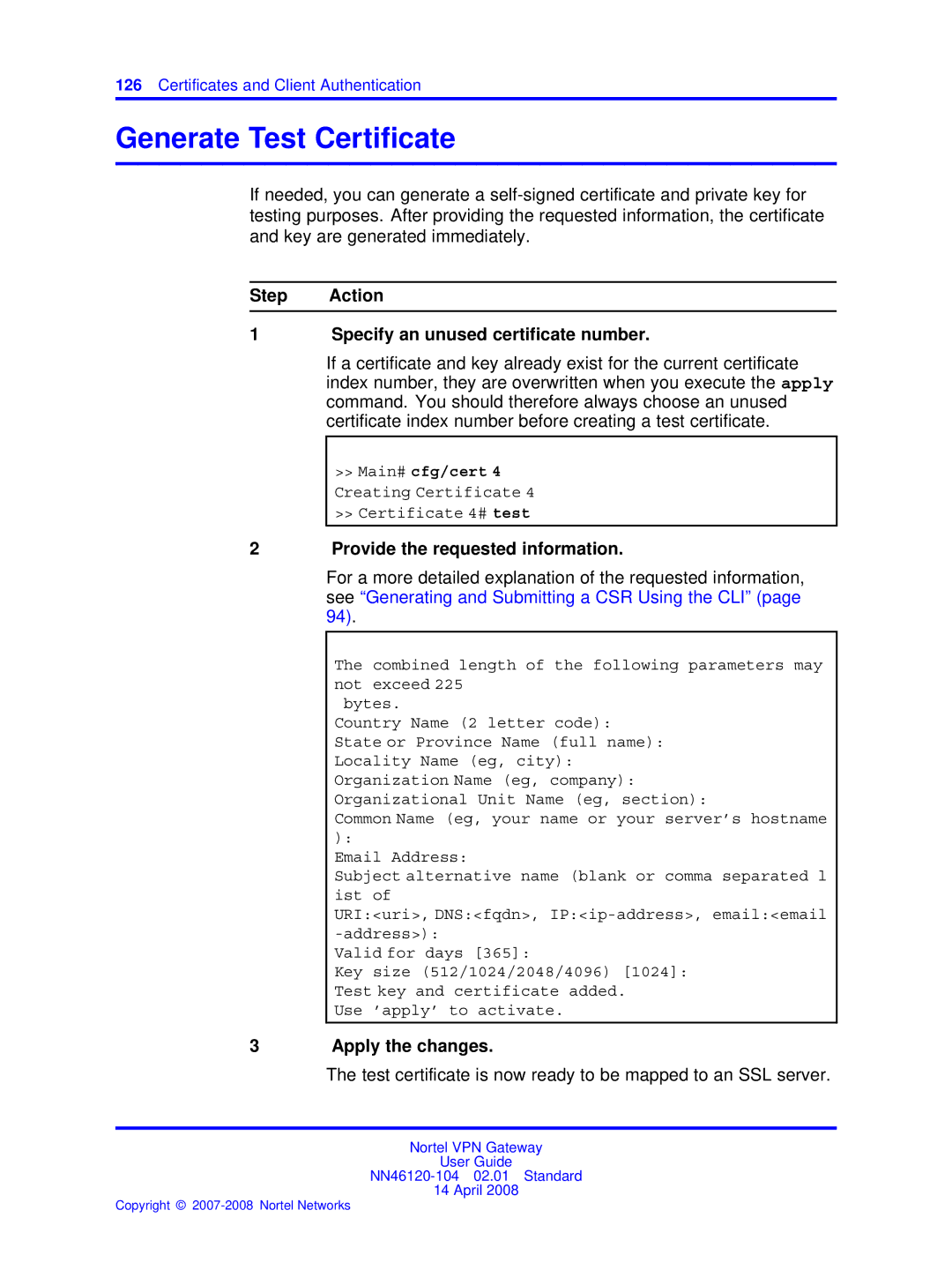
Generate Test Certificate
Step Action Specify an unused certificate number
Provide the requested information
Automatic CRL Retrieval
Show Subject Information
General Commands
Show Certificate Information
Check if Key and Certificate Match
Show Key Size
Show Key Information
Certificates and Client Authentication
Virtual Desktop
Running the Virtual Desktop on Client Computers
Licensing vdesktop
Launch Vdesktop from Portal
Click Save
Virtual Desktop Operations
Command Line Interface
Establishing a Console Connection
Connecting to the VPN Gateway
Procedure
Requirements
Enabling and Restricting Telnet Access
Establishing a Telnet Connection
Running Telnet
Running an SSH Client
Establishing a Connection Using SSH Secure Shell
Enabling and Restricting SSH Access
Telnet IP address
Establishing a Connection Using SSH Secure Shell
Accessing the NVG Cluster
User Access Level Description Default Account Group Passwo
ForgetM
CLI vs. Setup
Command Line History and Editing
Idle Timeout
Troubleshooting the NVG
Cannot Connect to VPN Gateway through Telnet or
Enable Telnet or SSH Access
Check the Access List
Verify the Current Configuration
Check the IP Address Configuration
Cannot Add an NVG to a Cluster
Add Interface 1 IP Addresses and MIP to Access List
# /cfg/sys/accesslist/add
Cannot Contact the MIP
Troubleshooting the NVG
NVG Stops Responding
Telnet or SSH Connection to the Management IP Address
Console Connection
Operator User Password
User Password is Lost
Administrator User Password
Root User Password
Password enter the admin user password
An ASA 310-FIPS Stops Processing Traffic
Main# maint/hsm/login
Password associated with the HSM-USER iKey for card
# /info/events/alarms
Resetting HSM Cards on the ASA 310-FIPS
Main# /boot/delete
End
Step Action
Existing
Transfer the cluster wrap key to card
Enter the same secret passphrase as was used Former cluster
Wait for the setup of the added ASA 310-FIPS to finish
Same secret passphrase as was used in the former Cluster
Main# cfg/gtcfg
User Fails to Connect to the VPN
Aaa
Main# maint/starttrace
Dns
Ike
Ipsec
Ippool
Ssl
Upref
Smb
Ftp
Netdirect
Netdirectpacket
Is Net Direct enabled and configured correctly?
Netdirectpacket
End
Cannot download the NetDirect Zipped file from client PC
System Diagnostics
Installed Certificates and Virtual SSL Servers
Network Diagnostics
# /info/ethernet
# /cfg/sys/cur
# /stats/dump
# ping IP address of virtual server
# /cfg/ssl/server #/trace/ssldump
Active Alarms and the Events Log File
Error Log Files
# /info/events/download
Unable to download NetDirect from VPN server
Troubleshooting the NVG
Appendix Supported Ciphers
Supported Ciphers
Supported Ciphers cont’d
Cipher List Formats
Modifying a Cipher List
Supported Cipher Strings and Meanings
Cipher Strings and Meanings
Cipher Strings and Meanings cont’d
Appendix Snmp Agent
Supported MIBs
SNMPv2-MIB
SNMP-FRAMEWORK-MIB
SNMP-TARGET MIB
SNMP-USER-BASED-SM-MIB
Limitations
IP-MIB
ALTEON-ISD-PLATFORM-MIB
IANAifType-MIB
Supported Traps
Following Snmp traps are supported by the VPN Gateway
Snmp Agent
Appendix Syslog Messages
Operating System OS Messages
Config filesystem corrupt beyond repair
List of Syslog Messages
Root filesystem corrupt
System Control Process Messages
Config filesystem corrupt
Missing files in config filesystem
System started isdssl-version
Name logopenfailed
Name isddown
Name singlemaster
Name makesoftwarereleasepermanentfailed
Name sslhwfail
Name copysoftwarereleasefailed Sender IP
Name license
Name hsmnotloggedin
Name ssimipishere
Name softwareconfigurationchanged
Name partitionednetwork
Name licenseexpiresoon
Traffic Processing Messages
Jscript.encode error reason
Javascript error reason for hostpath
Vbscript error reason for hostpath
Css error reason
Bad Ipport data line in hc script
Html error reason
Socks error reason
Bad regexp expr in health check
Certificate CRL handling errors
Proxy connect host name too long host
License expired
Gzip error reason
TPS license limit limit exceeded
Certificate CRL handling warnings
Startup Messages
Configuration Reload Messages
AAA Subsystem Messages
Log functionality
Ldap backends unreachable Vpn=\id\ AuthId=\authid\
Host host ip is up accounted for in the license pool
IPsec Subsystem Messages
All credits are exhausted for IPSec SA
Ignoring request to roam from %s to %s
PFS is required but not provided by %s
Failed to allocate IP addr from empty pool
Bad clicert, Can’t find issuer in clicert
Error while decoding certificate DER Id
Failed to decode client cert
Loaded ca certificate %s
Deleting the QM replaced by new rekeyed QM
Revocation byte length %d
Loaded server cert %s
Syslog Messages in Alphabetical Order
Syslog Messages in Alphabetical Order
Syslog Messages in Alphabetical Order cont’d
Config filesystem re-initialized
Down
AAA
Html
IPsec Isakmp SA Established Isddown
Cfg/sys/cur command
Gateway but /cfg/vpn # /ser
Loaded server id *will not Processing
Received Delete Isakmp SA
Socks error reason
System started isdssl-version
VPN LoginFailed Vpn=id
OpenSSL License Issues
Appendix License Information
Original SSLeay License
GNU General Public License
GNU General Public License
Terms and Conditions for COPYING, Distribution Modification
227
License Information
No Warranty
Apache Software License, Version
231
License Information
Appendix HSM Security Policy
Scope
Applicable Documents
Overview
Capabilities
Algorithm How it is used by the HSM module Used Fips Mode?
SHA-1
Physical Security
Module Interfaces
Components
Definition of Security Relevant Data Items
HSM Security Policy
Roles and Services
Services
User Creation
YES
Service FIPS140-1 Level 3 Mode
EPK, DPK
EPK
MK, Sopin
Key Management
Key Generation
Key Storage
Key Entry and Output
Key Distribution
Key Destruction
Fips 140-1 Mode
Modes
Key Archiving
Non-FIPS 140-1 Mode
Self-Tests
Conclusion
RC4 KAT
Appendix Definition of Key Codes
Syntax Description
Allowed Special Characters
Redefinable Keys
Allowed Special Characters Explanation
Example of a Key Code Definition File
Appendix SSH host keys
Methods for Protection
VPN Gateway
SSH host keys
261
Install All Administrative Tools Windows 2000 Server
Register the Schema Management dll Windows Server
Step Action Click Start and select Run
Add Standalone Snap-in window is displayed
Under Snap-in, select Active Directory Schema and click Add
Create a Shortcut to the Console Window
Permit Write Operations to the Schema Windows 2000 Server
Right-click Attributes, point to New and select Attribute
Click Continue
Create New Class
Create the isdUserPrefs attribute as shown Click OK
Create the nortelSSLOffload class as shown
Add isdUserPrefs Attribute to nortelSSLOffload Class
Click Next Click Finish
Add the nortelSSLOffload Class to the User Class
Click OK
Adding User Preferences Attribute to Active Directory
Appendix Using the Port Forwarder API
General
Creating a Port Forwarder
=1&c=1
Demo Application
Content.zip file
Creating a Port Forwarder Authenticator
Example
Example
Using the Port Forwarder API
Adding a Port Forwarder Logger
Using the Port Forwarder API
Example
Connecting Through a Proxy
Monitoring the Port Forwarder
Status
Statistics
Using the Port Forwarder API
Glossary
Access Rules
CLI Command Line Interface
Base Profile
CRL Certificate Revocation List
Cluster of VPN Gateways
Console Connection
CSR Certificate Signing Request
DTE Data Terminal Equipment
DIP Destination IP Address
DPort Destination Port
Extended Profile
Master
Http Proxy
IP Interface
MIB Management Information Base
Passphrase
Nslookup
NTP Network Time Protocol
PEM Privacy Enhanced Mail
Port Forwarder
Setup Utility
Portal
Real Server Group
Snmp Simple Network Management Protocol
SIP Source IP Address
Slave
SPort Source Port
STP Spanning Tree Protocol
SSL Secure Sockets Layer Protocol
SSL VPN client
TLS Transport Layer Security
Virtual SSL Server
VIP Virtual Server IP Address
Virtual Router
Vlan Virtual Local Area Network
509
Index
HSM
SSL
298
Page
User Guide