TL-SG3216/TL-SG3424 JetStream L2 Lite Managed Switch
Copyright & Trademarks
Contents
Gvrp
100
VII
NDP
Package Contents
Intended Readers
About this Guide
Conventions
Overview of This Guide
System Switching Vlan Spanning Tree Multicast
QoS ACL Network Security Snmp Cluster
Return to Contents
Overview of the Switch
Main Features
Introduction
Appearance Description
Front Panel
¾ LEDs Name Status Indication
Rear Panel
Login to the Switch
Login
Configuration
Return to Contents
System Info
System
System Summary
¾ Port Status
Type
Port
Rate
Status
Device Description
System Time
¾ Device Description
Get GMT
Current System
Synchronize With
PC’S Clock
System IP
¾ IP Config
User Config
User Manage
User Table
¾ User Info
User ID, Name, Access Level and status Operation
User Status
¾ User Table
Config Backup
Config Restore
¾ Config Restore
System Tools
¾ Config Backup
Firmware Upgrade
System Reboot
Access Security
System Reset
Access Control
¾ Session Config
¾ Access Control Config
IP Address&Mask
MAC Address
¾ Access User Number
SSL Config
¾ Global Config
SSH Config
¾ Certificate Download
¾ Key Download
Idle Timeout
Protocol
Max Connect
Key Type
¾ Configuration Procedure
Download
¾ Network Requirements
Application Example 2 for SSH
Page
Return to Contents
Port Config
Switching
Port
Port Select
Description
Port Mirror
Speed and Duplex
Flow Control
Group
Mirror Mode
Mirroring
Mode
¾ Port Security
Port Security
LAG
Max Learned MAC
Learned Num
Aggregate Arithmetic
LAG Table
¾ LAG Table
Group Number
Detail Information
Static LAG
Lacp Config
¾ LAG Config
LAG will delete this LAG
Admin Key
¾ Lacp Config
System Priority
Port Priority
Traffic Monitor
Traffic Summary
¾ Auto Refresh
Traffic Statistics
MAC Address
Bound MAC address
Address Table
Way
Port
¾ Address Table
¾ Search Option
Static Address
MAC Address Displays the MAC address learned by the switch
Displays the corresponding Vlan ID of the MAC address
¾ Create Static Address
¾ Static Address Table
Dynamic Address
¾ Dynamic Address Table
¾ Aging Config
Bind
Filtering Address
¾ Filtering Address Table
¾ Create Filtering Address
Vlan
¾ Link Types of ports
802.1Q Vlan
¾ Pvid
¾ Vlan Table
Vlan Config
Vlan ID Select
Description :
Enter the ID number of Vlan
¾ Vlan Config
Is valid or not
¾ Vlan Members
Port Displays the port number
¾ Vlan Port Config
Required. On the VLAN→802.1Q VLAN→VLAN Config
Required. On the VLAN→802.1Q VLAN→Port Config page, set
¾ Vlan of Port
Vlan Description
MAC Vlan
VLAN→VLAN Config
¾ MAC Vlan Table
Protocol Vlan
MAC Select
Step Operation Description
¾ Encapsulation Format of Ethernet Data
¾ The Procedure for the Switch to Identify Packet Protocol
Encapsulation
¾ The Implementation of Protocol Vlan
802.3 raw 802.2 LLC Snap Protocol
Vlan packets are processed in the following way
Protocol Group Table
Protocol Group
¾ Protocol Group Table
¾ Protocol Group Config
Protocol Template
¾ Protocol Group Member
Application Example for 802.1Q Vlan
¾ Network Diagram ¾ Configuration Procedure
Required. On VLAN→802.1Q VLAN→Port Config page, configure
Required. On VLAN→802.1Q VLAN→VLAN Config page, create a
Application Example for MAC Vlan
Application Example for Protocol Vlan
¾ Network Diagram
Required. On VLAN→Protocol VLAN→Protocol Template
On VLAN→Protocol VLAN→Protocol Group page, create protocol
Gvrp
¾ Gvrp
Select Port Status Registration Mode
¾ Port Config
Configuration Procedure
¾ STP Elements
Spanning Tree
¾ STP Timers
¾ Bpdu Comparing Principle in STP mode
¾ STP Generation
Tips :
Step Operation
¾ Mstp Elements
¾ Rstp Elements
¾ Port Roles
¾ Port States
STP Config
STP Config
Version
Forward Delay
Hello Time
Max Age
STP Summary
Port Config
ExtPath
Priority
IntPath
Edge Port
Region Config
Mstp Instance
Port Status
¾ Region Config
Instance Config
¾ Instance Table
Instance Port Config
Instance
Clear
Instance ID
Path Cost
Port Role
Port Protect
STP Security
¾ TC Protect
¾ Bpdu Protect
¾ Bpdu Filter
Root Protect
Loop Protect
TC Protect
Bpdu Protect
TC Protect
Application Example for STP Function
On Spanning Tree→STP Config→STP Config
On Spanning Tree→STP Config→Port Config
On Spanning Tree→MSTP Instance→Instance
Configure Switch D
¾ Suggestion for Configuration
Multicast
¾ Multicast Overview
¾ Multicast Address
Multicast IP Port
¾ Multicast Address Table
¾ Igmp Snooping
Igmp Snooping
¾ Igmp Snooping Process
¾ Igmp Messages
¾ Igmp Snooping Fundamentals
Snooping Config
Description Displays Igmp Snooping status Member
¾ Igmp Snooping Status
Fast Leave
Igmp Snooping
Member Port Time
Router Port Time
Leave Time
Static Router Port
Multicast→IGMP Snooping→VLAN Config
Snooping→Snooping Config and Port Config
Multicast Vlan
Displays the Vlan ID
¾ Multicast Vlan
On the Multicast→IGMP Snooping→Snooping Config
Vlan
Multicast→IGMP Snooping→Multicast Vlan
Snooping→Port Config
¾ Configuration Procedure Step Operation Description
Snooping→Snooping Config
Multicast IP
Static Multicast IP
Multicast IP Table
Multicast Filter
¾ Create Static Multicast
¾ Static Multicast IP Table
IP Range ID
IP-Range
Start Multicast IP
End Multicast IP
Action Mode
¾ Port Filter Config
Port Filter
Filter
Ports taking up too much bandwidth
Packet Statistics
Displays the LAG number which the port belongs to
Multicast→Multicast Filter→IP-Range
¾ Igmp Statistics
¾ Priority Mode
QoS
¾ QoS
802.1Q frame
¾ Schedule Mode
SP-Mode
¾ Port Priority Config
DiffServ
Port Priority
Required. On QoS→DiffServ→Schedule Mode
Schedule Mode
¾ Schedule Mode Config
Required. On QoS→DiffServ→Port Priority
3 802.1P Priority
Dscp Priority
¾ Priority Level
Required. On QoS→DiffServ→DSCP Priority
¾ Dscp Priority Config
¾ Rate Limit Config
Bandwidth Control
Rate Limit
Storm Control
¾ Storm Control Config
Broadcast Rate
Voice Vlan
Bps
Mulitcast Rate
TAG
¾ Security Mode of Voice Vlan
Global Config
Security Packet Type Processing Mode
Enter the Vlan ID of the voice Vlan
Select the desired port for voice Vlan configuration. It is
OUI Config
Displays the OUI address of the voice device
Configuration Procedure of Voice Vlan
Time-Range
ACL
Time-Range Summary
Index
Time-Range Create
Holiday Config
ACL Config
¾ Create Holiday
¾ Holiday Table
ACL Create
ACL Summary
¾ Rule Table
¾ Create ACL
¾ Create MAC ACL
MAC ACL
Rule ID
EtherType
Extend-IP ACL
Standard-IP ACL
¾ Create Standard-IP ACL
Time-Range
¾ Create Extend-IP ACL
IP Protocol
TCP Flag :
Policy Summary
Policy Config
Action Create
Policy Create
¾ Create Policy
¾ Create Action
Binding Table
Policy Binding
Port Binding
Vlan Binding
Direction Displays the binding direction
Application Example for ACL
¾ VLAN-Bind Config
Enter the ID of the Vlan you want to bind
¾ VLAN-Bind Table
On ACL→ACL Config→ACL Create page, create ACL
On ACL→ACL Config→Standard-IP ACL page, select ACL
IP-MAC Binding
Network Security
Manual Binding
Enter the Vlan ID
¾ Manual Binding Option
Protect Type Select the Protect Type for the entry
¾ Manual Binding Table
ARP Scanning
Start IP Address
Dhcp Snooping
End IP Address
Scan
¾ Dhcp Working Principle
Network diagram for DHCP-snooping implementation
¾ Option
¾ Dhcp Cheating Attack
Dhcp Cheating Attack Implementation Procedure
¾ Dhcp Snooping Config
¾ Option 82 Config
¾ Port Config Port Select
Customization Circuit ID Remote ID
ARP Inspection
¾ Imitating Gateway
¾ Cheating Gateway
¾ Cheating Terminal Hosts
10 ARP Attack Cheating Gateway
¾ Man-In-The-Middle Attack
¾ ARP Flooding Attack
ARP Detect
¾ ARP Detect
¾ Trusted Port
ARP Defend
Required. On the Network Security→IP-MAC
Network Security→ARP
¾ ARP Defend
ARP Statistics
Defend
Speed
¾ Illegal ARP Packet
DoS Defend
DoS Attack Type Description
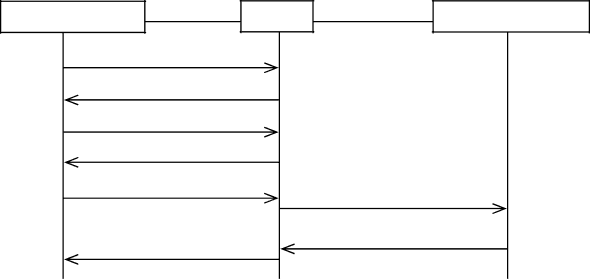
¾ Architecture of 802.1X Authentication
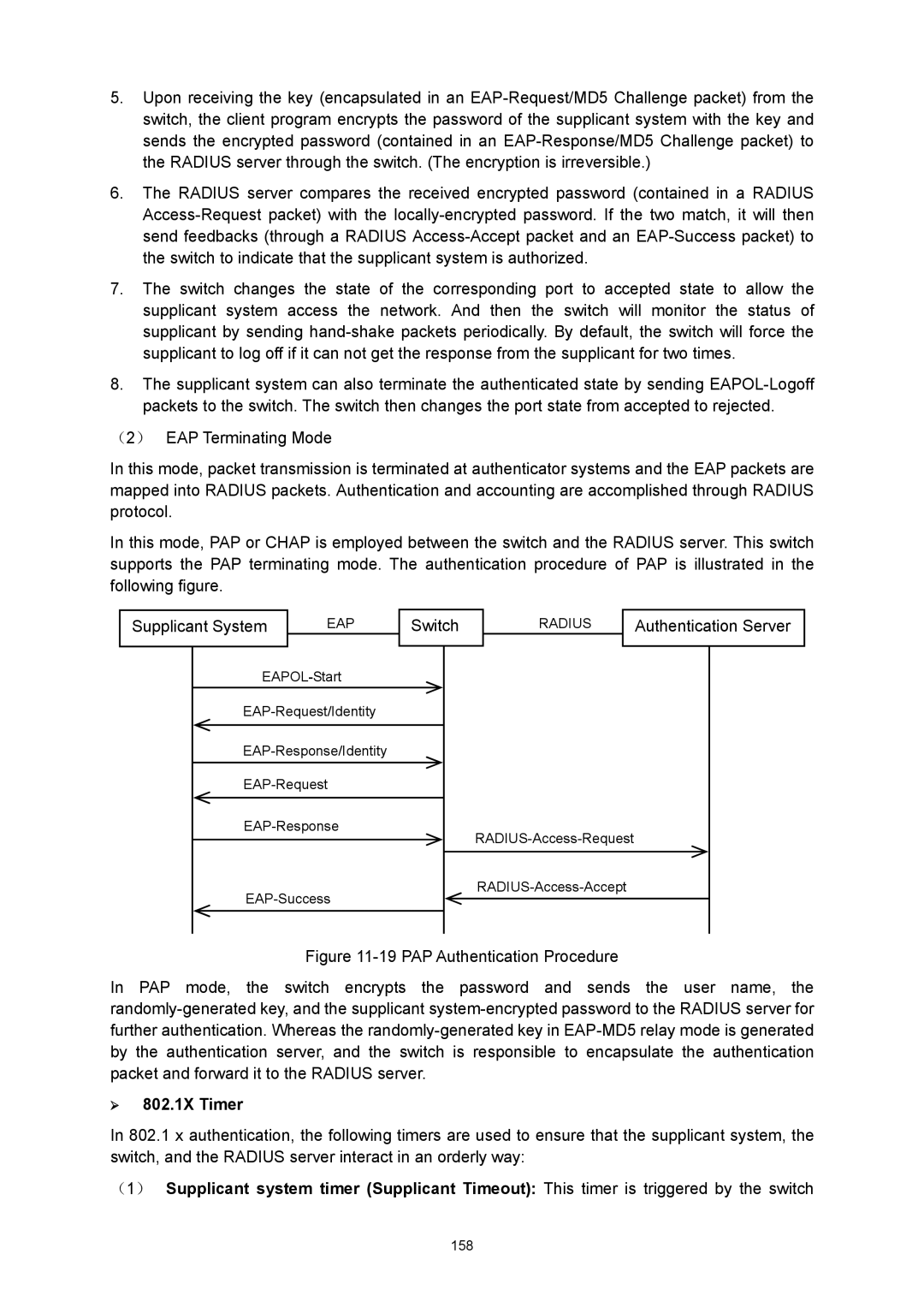
¾ Configure
11.4
¾ Defend Table
¾ The Mechanism of an 802.1X Authentication System
¾ 802.1X Authentication Procedure
¾ 802.1X Timer
¾ Guest Vlan
802.1X
Authentication Method
Guest Vlan
Guest Vlan ID
Supplicant Timeout
Server Timeout
Retry Times
Radius Server
Control Mode
Control Type
Authorized
On the Network Security→802.1X→Global Config
Required. On the Network Security→802.1X→Radius
Required. On the Network Security→802.1X→Port
¾ Snmp Overview
Snmp
¾ Snmp Management Frame
¾ Snmp Versions
¾ MIB Introduction
¾ Snmp Configuration Outline
Snmp Config
¾ Local Engine
¾ Remote Engine
MIB Object ID
Snmp View
View Type
View Name
Snmp Group
¾ Group Config
¾ Group Table
Snmp User
Auth Password
Auth Mode
Privacy Mode
Privacy Password
¾ Community Config
Access
Snmp Community
Required. On the SNMP→SNMP Config→SNMP
Required. On the SNMP→SNMP Config→Global
MIB View
¾ Community Table
Notification
On the SNMP→SNMP Config→SNMP
UDP Port
Timeout
User
Retry
Rmon
¾ Rmon Group
Rmon Group Function
Event Config
History Control
¾ History Control Table
¾ Event Table
Alarm Config
Sample Type
Variable
Rising Threshold
Rising Event
179
¾ Cluster Role
Cluster
13.1 NDP
Neighbor Info
¾ Introduction to Cluster
NDP Summary
¾ Neighbor
¾ Neighbor Info
NDP
¾ Port Status Displays the port number of the switch
Enable
NDP Config
Disable
¾ Global Cofig
Device Table
Ntdp
Device MAC
Cluster Name
Hops
Ntdp Summary
Neighbor Info
Collect Topology
Port Displays the port number of the switch
Ntdp Config
Ntdp Port Delay
Ntdp Hop Delay
Ntdp Interval Time
Ntdp Hops
Cluster Summary
Cluster
¾ Global
Cluster
¾ Global Config Cluster
Cluster Config
¾ Role Change
¾ Current Role
Application Example for Cluster Function
On Cluster→NTDP→NTDP Config page, enable
On Cluster→NDP→NDP Config page, enable NDP
194
Maintenance
System Monitor
CPU Monitor
Memory Monitor
14.2 Log
Local Log
Log Table
Remote Log
¾ Local Log Config
Log Buffer
Log File
Backup Log
¾ Log Host
Host IP
Device Diagnose
Error
Cable Test
Pair
Network Diagnose
Switch is available
Loopback
Ping
Tracert
¾ Ping Config
10 Tracert Following entries are displayed on this screen
¾ Tracert Config
Appendix a Specifications
Appendix B Configuring the PCs
207
Now
Appendix C Load Software using FTP
Hardware Installation
Configure the Hyper Terminal
210
Figure C-5 Port Settings
Download Firmware via bootUtil menu
Are you want to upgrade the firmwareY/N y
TP-LINK upgrade You can only use the port 1 to upgrade
User
TP-LINK start Start
Appendix D 802.1X Client Software
Installation Guide
215
216
Figure D-7 InstallShield Wizard Complete
Uninstall Software
Figure D-11 Uninstall Complete
Configuration
219
Figure D-16 Connection Status
FAQ
221
Appendix E Glossary
Group Attribute Registration Protocol Garp
Multicast Switching
Ieee 802.1D
Ieee 802.1Q
Remote Authentication Dial-in User Service Radius
Port Authentication
Link Aggregation
Link Aggregation Control Protocol Lacp
Simple Network Time Protocol Sntp
Simple Network Management Protocol Snmp
Spanning Tree Algorithm STA
Telnet