RTA770W, RTA770 specifications
The Dynalink RTA770 is a versatile and powerful router designed to meet the demands of modern home and small business networking. Recognized for its reliability and performance, the RTA770 incorporates advanced technologies that enhance connectivity and overall user experience.One of the main features of the RTA770 is its dual-band capability, offering simultaneous 2.4 GHz and 5 GHz frequency bands. The dual-band functionality allows for greater flexibility in network connections, reducing interference and optimizing performance. The 2.4 GHz band is ideal for devices like smartphones, tablets, and smart home devices that require a stable signal over longer distances. Conversely, the 5 GHz band caters to bandwidth-intensive activities such as online gaming, streaming high-definition videos, and video conferencing, providing faster speeds with reduced latency.
The RTA770 is equipped with the latest Wi-Fi 6 technology, which significantly boosts speed and efficiency. Wi-Fi 6, also known as 802.11ax, enhances wireless throughput, allowing multiple devices to connect simultaneously without compromising on performance. This is especially beneficial for households with numerous smart devices and users, ensuring a seamless online experience.
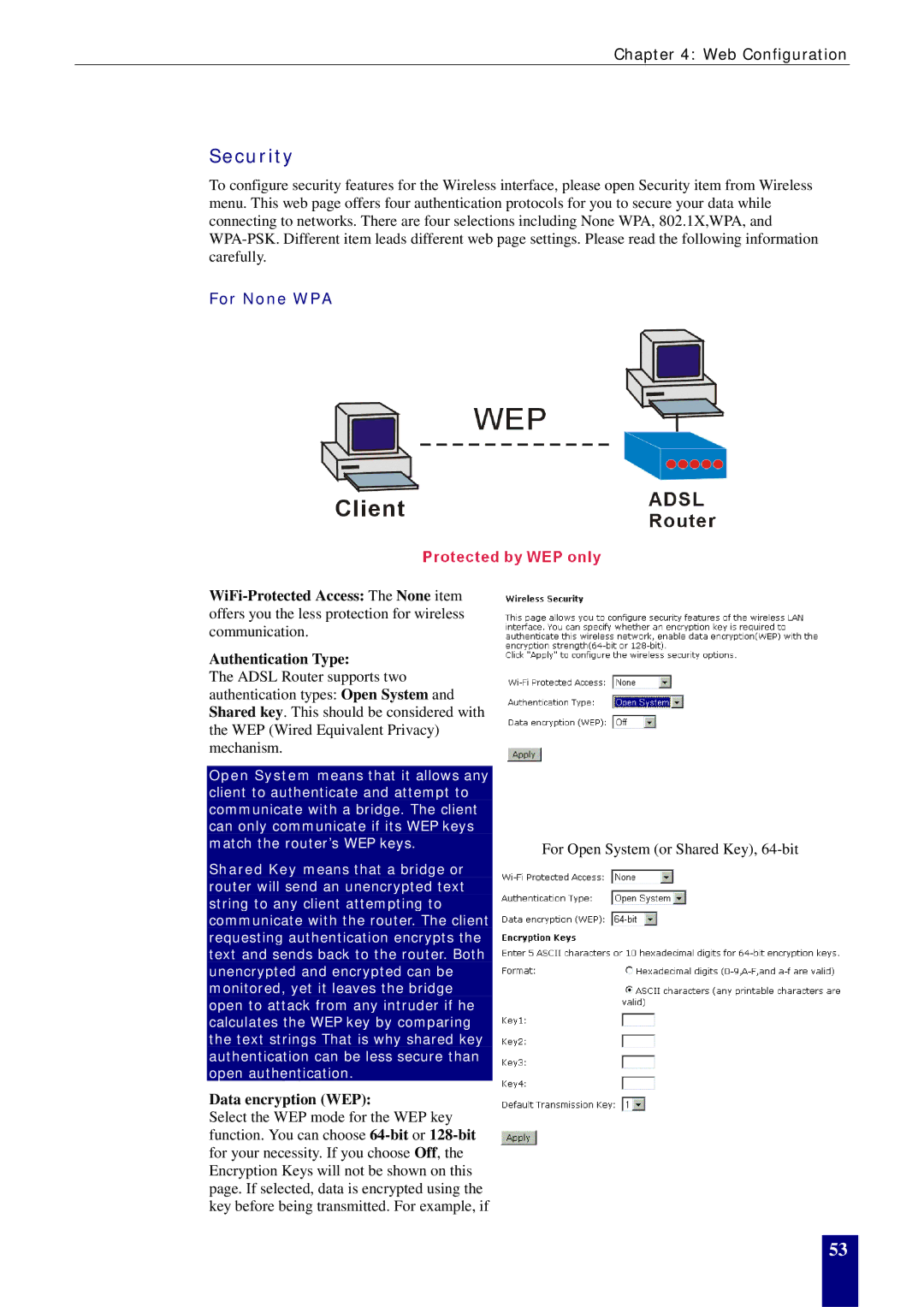
Security is a prominent consideration in the design of the RTA770. It features advanced encryption protocols, including WPA3, which offers improved protection against unauthorized access and ensures that personal information remains secure while browsing the internet. The router also supports guest network capability, allowing visitors to access the internet without exposing the primary network.
In terms of connectivity, the RTA770 boasts several ports including Gigabit Ethernet ports that facilitate wired connections for devices such as gaming consoles, smart TVs, and computers. This ensures optimal network performance for devices that require stable connections.
Furthermore, the Dynalink RTA770 includes an easy-to-use web interface for quick setup and management of network settings. Users can conveniently monitor connected devices, configure parental controls, and manage bandwidth allocation.
Overall, the Dynalink RTA770 stands out as a robust networking solution, combining dual-band performance, cutting-edge Wi-Fi 6 technology, enhanced security features, and user-friendly management tools. This makes it a compelling choice for both home users and small businesses looking to improve their network infrastructure.