|
|
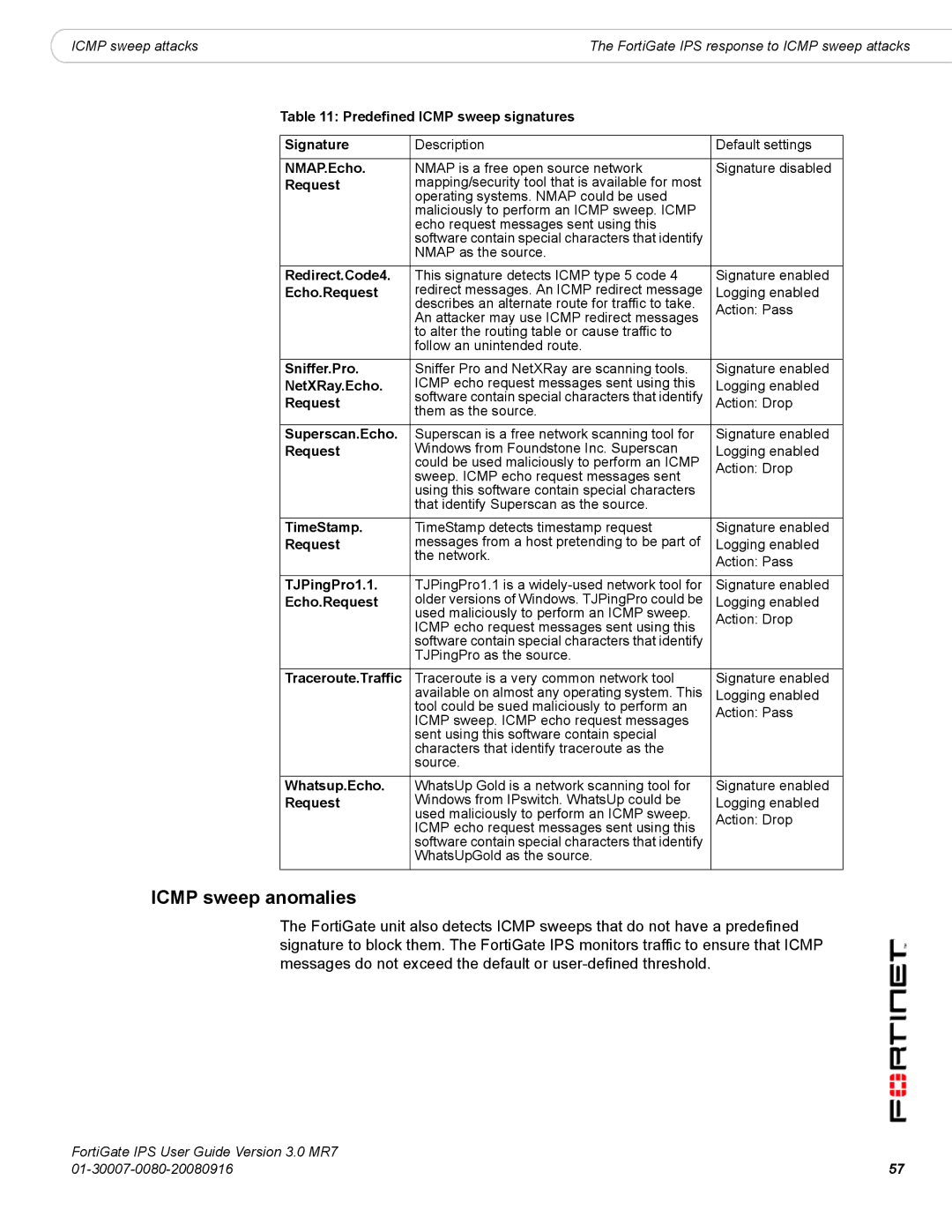
ICMP sweep attacks | The FortiGate IPS response to ICMP sweep attacks |
Table 11: Predefined ICMP sweep signatures
Signature | Description | Default settings |
|
|
|
NMAP.Echo. | NMAP is a free open source network | Signature disabled |
Request | mapping/security tool that is available for most |
|
| operating systems. NMAP could be used |
|
| maliciously to perform an ICMP sweep. ICMP |
|
| echo request messages sent using this |
|
| software contain special characters that identify |
|
| NMAP as the source. |
|
|
|
|
Redirect.Code4. | This signature detects ICMP type 5 code 4 | Signature enabled |
Echo.Request | redirect messages. An ICMP redirect message | Logging enabled |
| describes an alternate route for traffic to take. | Action: Pass |
| An attacker may use ICMP redirect messages | |
|
| |
| to alter the routing table or cause traffic to |
|
| follow an unintended route. |
|
|
|
|
Sniffer.Pro. | Sniffer Pro and NetXRay are scanning tools. | Signature enabled |
NetXRay.Echo. | ICMP echo request messages sent using this | Logging enabled |
Request | software contain special characters that identify | Action: Drop |
| them as the source. |
|
Superscan.Echo. | Superscan is a free network scanning tool for | Signature enabled |
Request | Windows from Foundstone Inc. Superscan | Logging enabled |
| could be used maliciously to perform an ICMP | Action: Drop |
| sweep. ICMP echo request messages sent | |
|
| |
| using this software contain special characters |
|
| that identify Superscan as the source. |
|
|
|
|
TimeStamp. | TimeStamp detects timestamp request | Signature enabled |
Request | messages from a host pretending to be part of | Logging enabled |
| the network. | Action: Pass |
|
| |
|
|
|
TJPingPro1.1. | TJPingPro1.1 is a | Signature enabled |
Echo.Request | older versions of Windows. TJPingPro could be | Logging enabled |
| used maliciously to perform an ICMP sweep. | Action: Drop |
| ICMP echo request messages sent using this | |
|
| |
| software contain special characters that identify |
|
| TJPingPro as the source. |
|
|
|
|
Traceroute.Traffic | Traceroute is a very common network tool | Signature enabled |
| available on almost any operating system. This | Logging enabled |
| tool could be sued maliciously to perform an | Action: Pass |
| ICMP sweep. ICMP echo request messages | |
|
| |
| sent using this software contain special |
|
| characters that identify traceroute as the |
|
| source. |
|
|
|
|
Whatsup.Echo. | WhatsUp Gold is a network scanning tool for | Signature enabled |
Request | Windows from IPswitch. WhatsUp could be | Logging enabled |
| used maliciously to perform an ICMP sweep. | Action: Drop |
| ICMP echo request messages sent using this | |
|
| |
| software contain special characters that identify |
|
| WhatsUpGold as the source. |
|
|
|
|
ICMP sweep anomalies
The FortiGate unit also detects ICMP sweeps that do not have a predefined signature to block them. The FortiGate IPS monitors traffic to ensure that ICMP messages do not exceed the default or
FortiGate IPS User Guide Version 3.0 MR7 |
|
57 |