9.Configure the wireless security settings. Select the method your network is using, WPA, WPA2, WEP
WPA
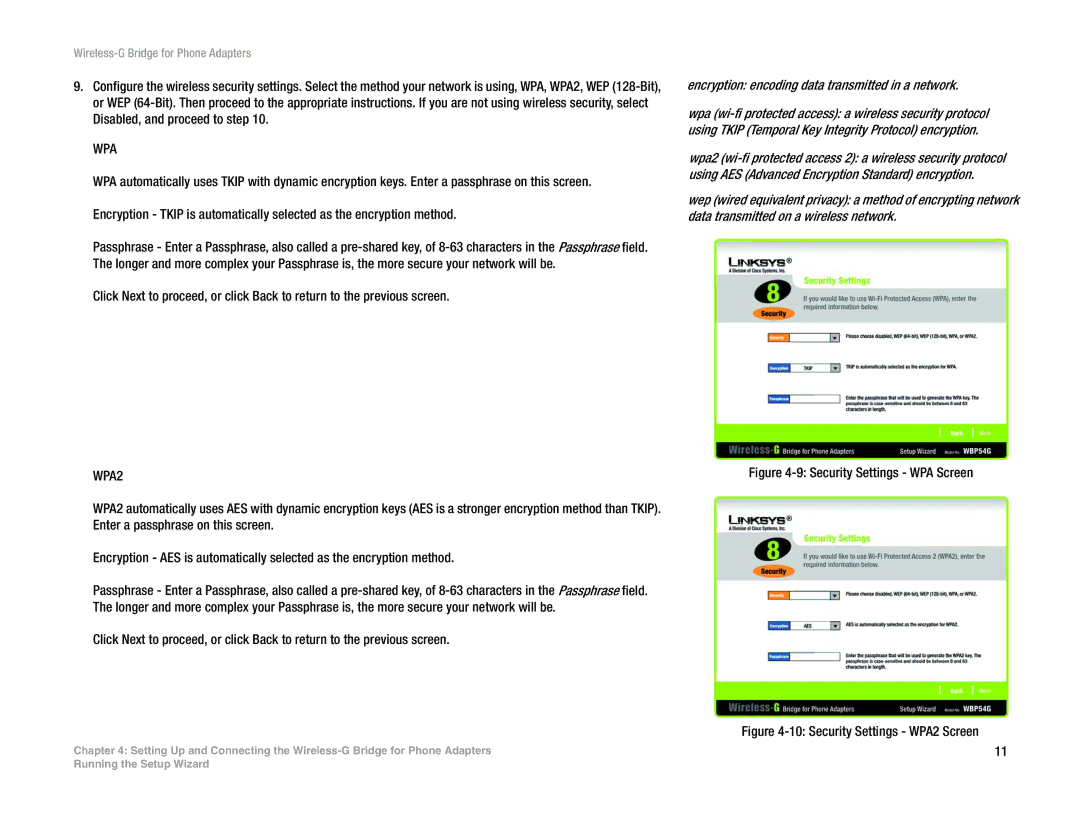
WPA automatically uses TKIP with dynamic encryption keys. Enter a passphrase on this screen. Encryption - TKIP is automatically selected as the encryption method.
Passphrase - Enter a Passphrase, also called a
Click Next to proceed, or click Back to return to the previous screen.
WPA2
WPA2 automatically uses AES with dynamic encryption keys (AES is a stronger encryption method than TKIP). Enter a passphrase on this screen.
Encryption - AES is automatically selected as the encryption method.
Passphrase - Enter a Passphrase, also called a
Click Next to proceed, or click Back to return to the previous screen.
Chapter 4: Setting Up and Connecting the
encryption: encoding data transmitted in a network.
wpa
wpa2
wep (wired equivalent privacy): a method of encrypting network data transmitted on a wireless network.
Figure 4-9: Security Settings - WPA Screen
Figure 4-10: Security Settings - WPA2 Screen
11
Running the Setup Wizard