Introduction
PCR Module Firewall Network affecting No
PCR Module FFS File TTY Network affecting No
PCR 02396 Module Dhcp Network affecting No
PCR Module IPG Network affecting No
PCR Module VRRP, TRG Network affecting No
PCR Module CORE, FFS, File Network affecting No
Source net mask has been removed from Dvmrp prune, graft
DVMRP. This issue has been resolved
PCR Module Dvmrp Network affecting No
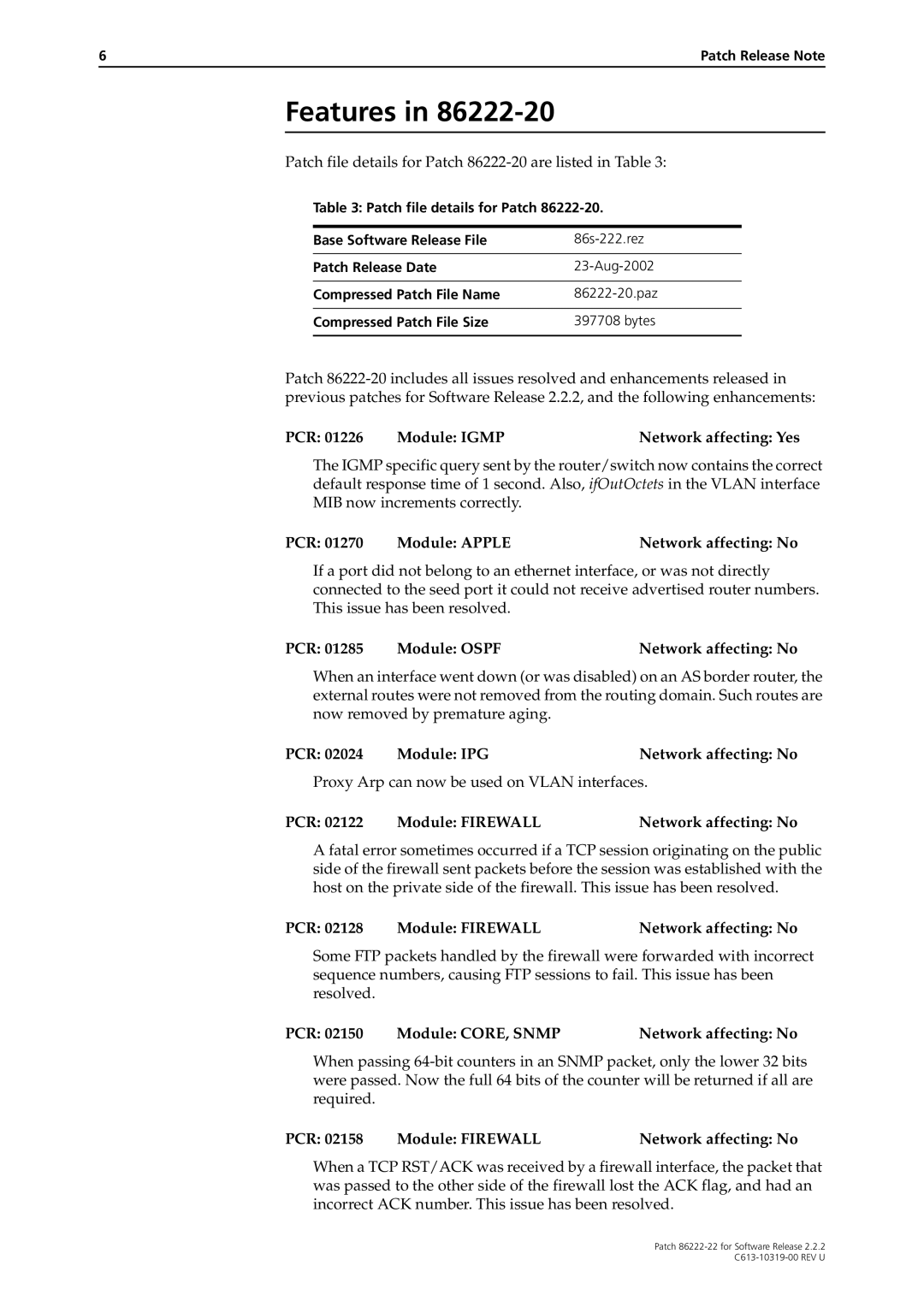
Patch file details are listed in Table
PCR 02343 Module PPPNetwork affecting No
PCR 02329 Module DHCPNetwork affecting No
PCR 02332 Module IPSECNetwork affecting No
PCR 02368 Module IPG/IGMPNetwork affecting No
PCR Module Ospf Network affecting No
PCR Module Igmp Network affecting Yes
PCR Module Apple Network affecting No
PCR Module CORE, Snmp Network affecting No
PCR 02198 Module Dhcp Network affecting Yes
PCR Module LOG Network affecting No
Log messages are no longer stored in NVS
PCR Module DHCP, IPG Network affecting No
PCR Module File Network affecting No
PCR Module Vrrp Network affecting No
PCR Module DNS Network affecting No
PCR Module PIM, DVMRP, SWI Network affecting No
PCR Module DUART, TM Network affecting No
PCR Module Tpad Network affecting No
Patch file details for Patch 86222-19 are listed in Table
PCR Module STP Network affecting No
PCR Module IPG Network affectingNo
PCR Module Dhcp Network affecting No
PCR Module Load Network affecting No
PCR Module FILE, FFS Network affecting No
Patch file details for Patch 86222-18 are listed in Table
PCR Module OSPF, IPG Network affecting No
PCR Module Ospf Network affecting Yes
PCR Module TRG Network affecting No
Patch file details for Patch 86222-16 are listed in Table
PCR 02015 Module Snmp Network affecting No
PCR 02099 Module Dhcp Network affecting No
Patch file details for Patch 86222-15 are listed in Table
PCR 02070 Module Core Network affecting No
PCR Module Switch Network affecting No
PCR 02035 Module Vlan Network affecting No
PCR Module Ping Network affecting No
Patch file details for Patch 86222-13 are listed in Table
PCR Module Telnet Network affecting No
Patch file details for Patch 86222-12 are listed in Table
Has been added to the following commands
PCR 01257 Module Dhcp Network affecting No
PCR Module IPG/VRRP Network affecting No
PCR Module PPP Network affecting No
PCR Module Ipgigmp Network affecting No
PCR 02007 Module Dhcp Network affecting No
PCR Module Trigger Network affecting No
PCR Module IPG, VLAN, SWI Network affecting No
Patch file details for Patch 86222-11 are listed in Table
PCR Module STP, SWI Network affecting Yes
Patch file details for Patch 86222-10 are listed in Table
Patch file details for Patch 86222-09 are listed in Table
PCR Module SWI, CORE, IPG Network affecting No
PCR Module PRI Network affecting No
Patch file details for Patch 86222-08 are listed in Table
PCR Module L2TP Network affecting Yes
PCR 01237 Module SWINetwork affecting No
PCR 01233 Module PIMNetwork affecting No
PCR 01236 Module PPPNetwork affecting No
PCR 01018 Module Dhcp Network affecting No
PCR Module TCP Network affecting No
PCR Module L2TP, IPG Network affecting No
PCR Module Q931 Network affecting No
PCR 01202 Module Dhcp Network affecting No
PCR Module TRG, Snmp Network affecting No
PCR Module VLAN,SWI Network affecting No
Patch file details for Patch 86222-06 are listed in Table
PCR Module PIM Network affecting No
PCR Module PKI Network affecting No
Patch file details for Patch 86222-05 are listed in Table
PCR Module Core Network affecting No
PCR Module IPv6 Network affecting No
Patch file details for Patch 86222-04 are listed in Table
PCR 01186 Module FIREWALLNetwork affecting No
PCR 01187 Module IPGNetwork affecting No
PCR Module CORE, SWI Network affecting No
PCR 01165 Module Dhcp Network affecting No
PCR 01167 Module Enco Network affecting No
PCR Module ETH, Trigger Network affecting No
Patch file details for Patch 86222-01 are listed in Table
PCR 01100 Module Dhcp Network affecting No
PKI enrolment no longer causes message validation to fail
Availability