Americas Headquarters
Configuration Guide for Cisco Secure ACS
Page
N T E N T S
Deploying ACS in a NAC/NAP Environment
Error Messages
Overview
Profile Setup
Profile Setup
Organization
Audience
Boldface font
Conventions
Product Documentation
Convention
Available Formats
Related Documentation
ACSTroubleshooting.html
OpenSSL License
License Issues
OpenSSL/Open SSL Project
Original SSLeay License
Summary of Configuration Steps
Overview of ACS Configuration
Click System Configuration
Click Interface Configuration
Peap EAP-FAST EAP-TLS Leap EAP-MD5
Overview of ACS Configuration Summary of Configuration Steps
EAP-TLS, SSL
Configuration Flowchart
OL-14390-02
Determining the Deployment Architecture
Deploy the Access Control Servers
Size Users
Access Types
Wired LAN Access
Campus LAN
Small LAN Environment
ACS in a Campus LAN
Geographically Dispersed Wired LAN
Simple Wlan
Wireless Access Topology
Campus Wlan
Regional Wlan Setting
6shows a regional Wlan
Large Enterprise Wlan Setting
Small Dial-Up Network Access
Dial-up Access Topology
Small Dial-up Network
Large Dial-Up Network Access
Number of Users
Placement of the Radius Server
Determining How Many ACSs to Deploy Scalability
WAN Latency and Dependability
Number of Network Access Servers
LAN Versus WAN Deployment Number of LANs in the Network
Database Replication Considerations
Configuration components for replication-What is replicated
Deploying ACS Servers to Support Server Failover
Load Balancing and Failover
Replication Design
Database Synchronization Considerations
Cisco AAA server product
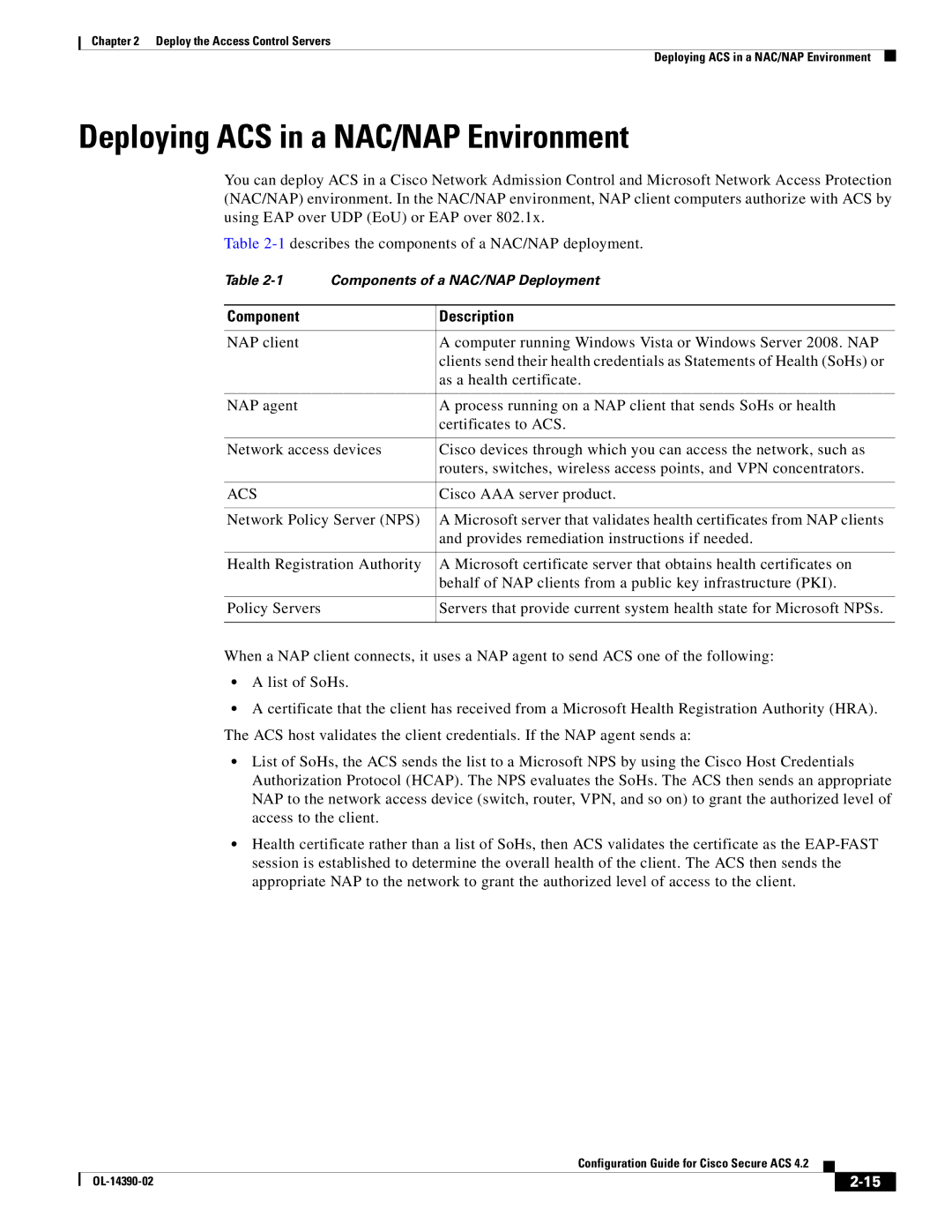
Deploying ACS in a NAC/NAP Environment
Component Description
ACS
Additional Topics
Remote Access Policy
Security Policy
Administrative Access Policy
Separation of Administrative and General Users
Type of Database
Database Considerations
Network Latency and Reliability
Number of Users
OL-14390-02
New Global EAP-FAST Configuration Options
Configuring New Features in ACS
PAC
Option Description
Use PAC and Do Not Use PAC Options
2shows the new options on the NAP Protocols
Disabling NetBIOS
Click Internet Protocol TCP/IP and choose Properties
Configuring ACS 4.2 Enhanced Logging Features
To disable NetBIOS over TCP/ IP in Windows 2000, XP, or
Right-clickMy Network Places and choose Properties
Click Submit
Configuring Group Filtering at the NAP Level
Active Directory Multi-Forest Support
Configuring Syslog Time Format in ACS
Check the Disable Dynamic users check box
Option to Not Log or Store Dynamic Users
Click Submit and Restart
Click Database Configuration
RSA Support on the ACS SE
Click Upload scconf.rec
Click Create New Configuration
Click Configure
Click RSA SecureID Token Server
Field
FTP Server Login Password Directory
External User Databases Configuration page opens
Purging the RSA Node Secret File
Click RSA SecurID Token and Ldap Group Mapping
Configuring RSA SecurID Token and Ldap Group Mapping
Click Configure Ldap
Click Purge Node Secret
Choose Process all usernames
RSA SecurID Token and Ldap Group Mapping Configuration
Configuring New Features in ACS RSA Support on the ACS SE
Configuring New Features in ACS RSA Support on the ACS SE
Uid=joesmith,ou=members,ou=administrators,o=cisco
Turning Ping On and Off
ACS 4.2 provides enhanced support for Rdbms Synchronization
New Rdbms Synchronization Features in ACS Release
Check the Rdbms Synchronization check box
Using Rdbms Synchronization to Configure dACLs
Enable dACLs
Create a Text File to Define the dACLs
Keyword Value
Example 4-1shows a sample text file
Code the information in the file as described in Table
Example 4-2shows a sample accountActions CSV file
Sample accountActions CSV File
Click Rdbms Synchronization
Configure Rdbms Synchronization to Use a Local CSV File
Action Code Name Required Description
Rdbms Synchronization Setup Page ACS for Windows
Configuration Guide for Cisco Secure ACS OL-14390-02
ACS for Windows
Perform Rdbms Synchronization
Running Rdbms Synchronization from the ACS GUI
Running CSDBSync Manually to Create the dACLs
View the dACLs
Performing Rdbm Synchronization Using a Script
Entry for the Sample dACL
NAF
Error Messages
Explanation
Reading, Updating, and Deleting dACLs
User has write access to the ACS
On the ACS is configured correctly
Enabled correctly in the ACS GUI
Deletedacl
Updatedacl
Readdacl
Daclreplace
Deleteuserdacl Ungn
Updateuserdacl UNGN, VN
Readnas
Updatenas
Creating, Reading, Updating and Deleting AAA clients
OL-14390-02
Password Policy Configuration Scenario
Add and Edit a New Administrator Account
Administration Control
Privileges that you want to grant
Configure Password Policy
Server 4.2, Administrators and Administrative Policy
To specify password restrictions
Administrator Password Policy Setup
Password Inactivity Options
Specify Password Validation Options
Specify Password Lifetime Options
Password Lifetime Options
Incorrect Password Attempt Options section, configure
Configure Session Policy
Specify Password Inactivity Options
Specify Incorrect Password Attempt Options
Session Policy Setup
Before You Begin
Configure Access Policy
Click Access Policy
Access Policy Setup page appears, as shown in Figure
Click the appropriate IP Address Filtering option
Access Policy Setup
Must differ only in the last octet Class C format
IP Address Ranges table contains ten rows for configuring
IP address ranges. The ranges are always inclusive that is,
Range includes the Start and End IP addresses
Displays an error
Viewing Administrator Entitlement Reports
Configuration ACS Certificate Setup to access
Installation process. With SSL enabled, ACS begins using
Click Entitlement Reports
View Privilege Reports
OL-14390-02
Overview of Agentless Host Support
Agentless Host Support Configuration Scenario
1shows the flow of MAB information
Using Audit Servers and Game Group Feedback
See Configure a Radius AAA Client, page 6-5for details
Configure a Radius AAA client
Install ACS
Basic Configuration Steps for Agentless Host Support
Configure a Radius AAA Client
Click Submit + Apply
Install and Set Up an ACS Security Certificate
Go to selecteddrive\Certs
Obtain Certificates and Copy Them to the ACS Host
Click Submit
Enable Security Certificates on the ACS Installation
Select Install Certificate
Click ACS Certificate Setup Click Install ACS Certificate
Add a Trusted Certificate
Install the CA Certificate
To install the CA Certificate
Create one or more Ldap database configurations in ACS
Configure Ldap Support for MAB
Configure an External Ldap Database for MAB Support
802.1x device n 802.1x device n+1
Description of the Settings in the Sample Ldap Schema
How the Ldap User Groups Work
How the Subtrees Work
Click Generic Ldap
Create One or More Ldap Database Configurations in ACS
1describes the attributes of the sample Ldap groups
6shows the Common Ldap Configuration section
Specify the common Ldap configuration
OL-14390-02
ACS SE Only
Ldap Server Configuration Sections
Configure User Groups for MAB Segments
Click Add Profile
Enable Agentless Request Processing
Create a New NAP
Profile Setup
Profile Setup page opens, shown in Figure
Check the check box for Allow Agentless Request Processing
Enable Agentless Request Processing for a NAP
You are now ready to enable agentless request processing
You are now ready to configure MAB settings
Configure MAB
13 MAC Address Input Area
Click Internal ACS DB
Configuring Reports for MAB Processing
Configure Logging and Reports
Configure Game Group Feedback
Configuration Steps for Audit Server Support
Specify EAP-TLS options
Configure Security Certificates
To configure PEAP-TLS Configure security certificates
Configure global authentication settings
Obtain Certificates and Copy Them to the ACS Host
Enable Security Certificates on the ACS Installation
Add a Trusted Certificate
Install the CA Certificate
Global Authentication Setup page opens, as shown in Figure
Configure Global Authentication Settings
Click Global Authentication Setup
EAPMSCHAP2 EAP-GTC
Optional Configure Authentication Policy
Specify EAP-TLS Options
Logging page opens, shown in Figure
Configuring Syslog Logging
Overview
Click Logging
Logging Configuration
Enable Logging
Facility Codes
Format of Syslog Messages in ACS Reports
Message Length Restrictions
OL-14390-02
Install ACS
NAC Configuration Scenario
This section describes
Perform Network Configuration Tasks
Add AAA Client
Configure the AAA Server
This section describes the following tasks
Set Up System Configuration
Click Submit and Apply
Click ACS Certification Authority Setup
Set Up the ACS Certification Authority
Click ACS Certificate Setup
Edit the Certificate Trust List
Choose ACS Certificate Setup Edit Certificate Trust List
Click the Read certificate from file radio button
Set Up Global Configuration
Install the ACS Certificate
Install ACS Certificate page opens, as shown in Figure
Global Authentication Setup Page appears, as shown in Figure
Set Up Global Authentication
Global Authentication Setup
Click Submit + Restart
Allow EAP-MSCHAPv2
Allow EAP-GTC
Allow Posture Validation
EAP Fast Configuration page appears, as shown in Figure
Set Up EAP-FAST Configuration
Click EAP-FAST Configuration
Provisioning check boxes
Check the Allow EAP-FASTcheck box
-8, this is ACS NAC Server. However, this can be any string
Click Service Control
Configure the Logging Level
Configure Logs and Reports
Check the Log to CSV Passed Authentications Report check box
Check the Log to CSV Radius Accounting Report check box
Add Administrator page opens, as shown in Figure
Set Up Administration Control
Add Remote Administrator Access
Click Add Administrator
10 Add Administrator
Click Grant All
Click Network Access Filtering
Set Up Shared Profile Components
Configure Network Access Filtering Optional
11 Edit Network Access Filtering
Configure Downloadable IP ACLs
List of dACLs appears, as shown in Figure
Adding an ACL
To add a new ACL
Choose Shared Profile Components Downloadable IP ACLs
13 Downloadable IP ACLs
Adding an ACE
14 Downloadable IP ACL Content
New ACL appears on the list of downloadable ACLs
Configure Radius Authorization Components
Saving the dACL
16 Radius Authorization Components
Click Radius Authorization Components
17 RAC Attribute Add/Edit
18 Attribute Selection for the CiscoFullAccess RAC
19 Attribute Selection for the CiscoRestricted RAC
ACL
Attribute
Number Attribute Name Description
Add the Posture Attribute to the ACS Dictionary
Configure an External Posture Validation Audit Server
Click Add Server
Configure the External Posture Validation Audit Server
20 External Posture Validation Audit Server Setup
21 Use These Audit Servers Section
Configure Internal Posture Validation Policies
Configure Posture Validation for NAC
Click Add Rule
Click Internal Posture Validation Setup
Add/Edit Condition page appears, as shown in Figure
Click Add Condition Set
26 Edit External Posture Validation Servers
Configure External Posture Validation Policies
27 Add/Edit External Posture Validation Server
Configure an External Posture Validation Audit Server
28 External Posture Validation Audit Server Setup
29 Use These Audit Servers Section
30 Audit Flow Settings and Game Group Feedback Sections
Authorization Policy and NAC Audit
EAP-FAST GTC
Set Up Templates to Create NAPs
Sample NAC Profile Templates
Sample NAC Layer 3 Profile Template
31 Create Profile From Template
Profile Setup
32 Profile Setup Page for Layer 3 NAC Template
Protocols Policy for the NAC Layer 3 Template
EAP Configuration section, Posture Validation is enabled
34 Authentication Page for Layer 3 NAC Profile Template
Authentication Policy
From the Template drop-down list, choose NAC L2 IP
Sample NAC Layer 2 Template
Sample Posture Validation Rule
Go to Network Access Profiles
To enable the profile setup
36 Profile Setup Page for NAC Layer 2 Template
ACS and Attribute-Value Pairs
Default ACLs
37shows the Protocols settings for the NAC Layer 2 template
Protocols Settings
38 Authentication Settings for NAC Layer 2 Template
39 Sample Posture Validation Policy for NAC Layer 2 Template
Sample NAC Layer 2 802.1x Template
40 Create Profile From Template
41 Profile Setup Page for NAC Layer 2 802.1x Template
Protocols Policy
42 Protocols Setting for NAC Layer 802.1x Template
Authorization Policy
Sample Wireless NAC L2 802.1x Template
45 Create Profile From Template
46 Profile Setup Page for Wireless NAC L2 802.1xTemplate
47 Protocols Setting for Wireless NAC 802.1x Template
Authorization Policy
Using a Sample Agentless Host Template
50 Create Profile From Template
Profile Setup
52 Protocols Setting for Agentless Host for Layer 3 Template
Enter a Name for the rule
Choose Network Access Profiles
Map Posture Validation Components to Profiles
Choose the relevant profile Posture Validation policy
Click Apply + Restart
Click Back to return to the Posture Validation policy
Click Select Audit
Check the Do not reject when Audit failed check box
Map an Audit Server to a Profile
Check the Allow Agentless Request Processing check box
Click Apply and Restart
Optional Configure Game Group Feedback
Configure an external audit server
Import NAC Attribute-Value Pairs
Import an Audit Vendor File by Using CSUtil
Import a Device-Type Attribute File by Using CSUtil
Restart ACS Navigation bar, click System Configuration
Configure Database Support for Agentless Host Processing
Enable Posture Validation
Configure an External Audit Server
\ACSInstallDir\bin\CSUtil -addAVP filename
56 External Posture Validation Audit Server Setup
57 Use These Audit Servers Section
58 Audit Flow Settings and Game Group Feedback Sections
ACS Solution Engine
Enable Game Group Feedback
PDA
Unix
Mac Integrated Device
Posture-validation server
Being authenticated
Authentication agent installed, such as Cisco Trust Agent
Resource usage
GL-2
Authenticate the device, instead of using an IP address
GL-3
Radius Attribute Component
Network access
Microsoft, and RSA Security submitted to the Ietf
ACE
Updatenas Updateuserdacl
Adduser
CA certificate Installing
Audit servers Configuring
Configuring audit flow settings for 9-35,9-43,9-78
NAP
Deleteuserdacl
Createuserdacl
Layer 2 NAC 802.1x template
Configuring new features in ACS 4.2
ACS configuration for
Specifying Certificate Binary Comparison for
NAC L2 IP
Netbios
NAC
NAC/NAP
RSA
Reliability
Readdacl Readnas
Reading dACLs Regional Wlan Related documentation
Security policies Security protocols
Using Windows Certificate Import Wizard
Installing the CA certificate
Purging Node Secret file purging Sarbanes-Oxley
Significance Windows Certificate Import Wizard