Page
Page
User Services Overview
Getting More Information and Help
Concepts
Cloud Infrastructure Concepts
Steps to Provisioning Your Cloud Infrastructure
Service Offerings
Setting Up Networking for Users
Working With Virtual Machines
Working With Hosts 103
Working with Templates 113
Working With Storage 129
Working with Usage 141
Managing Networks and Traffic 147
Page
Tuning 249
Troubleshooting 251
Working with System Virtual Machines 229
System Reliability and High Availability 233
Event Types 259 Alerts 261
Getting More Information and Help
Additional Documentation Available
Citrix Knowledge Center Contacting Support
Chapter
Page
What Is CloudPlatform?
Concepts
What Can CloudPlatform Do?
Multiple Hypervisor Support
Deployment Architecture Overview
Management Server Overview
Cloud Infrastructure Overview
Networking Overview
More Information
Page
Page
About Zones
Cloud Infrastructure Concepts
About Regions
Cloud Infrastructure Concepts
About Pods
About Clusters
About Hosts
About Primary Storage
About Secondary Storage
About Physical Networks
Basic Zone Network Traffic Types
Advanced Zone Guest IP Addresses
Basic Zone Guest IP Addresses
Advanced Zone Network Traffic Types
Advanced Zone Public IP Addresses
System Reserved IP Addresses
All zones
A zone that uses advanced networking
Page
Accounts
Accounts, Users, and Domains
Behavior of Dedicated Hosts, Clusters, Pods, and Zones
How to Use Dedicated Hosts
Dedicating Resources to Accounts and Domains
Adding an Ldap Server
Using an Ldap Server for User Authentication
Configuring an Ldap Server
Trust Store Trust Store Password
Search Base
Example Ldap Configuration Commands
Removing an Ldap Configuration
ApacheDS
Query Filter
Active Directory
SSL Keystore Path and Password
Search User Bind DN
Page
User Services Overview
Page
User Interface
Supported Browsers
Log In to the UI
End Users UI Overview
Root Administrators UI Overview
Logging In as the Root Administrator
Creating an Instance from a Template that Supports SSH Keys
Using SSH Keys for Authentication
Changing the Root Password
Output is something similar to what is given below
Creating the SSH Keypair
Creating an Instance
Logging In Using the SSH Keypair
Resetting SSH Keys
Page
Using Projects to Organize Users and Resources
Configuring Projects
Setting Up Invitations
Overview of Projects
Setting Resource Limits for Projects
Setting Project Creator Permissions
Sending Project Membership Invitations
Creating a New Project
Adding Members to a Project
Accepting a Membership Invitation
Adding Project Members From the UI
Using the Project View
Suspending or Deleting a Project
Page
Steps to Provisioning Your Cloud Infrastructure
Overview of Provisioning Steps
Adding a Region
First Region The Default Region
Adding Regions optional
Adding Third and Subsequent Regions
Deleting a Region
Prepare the System VM Template
Adding a Zone
Create a Secondary Storage Mount Point for the New Zone
Steps to Add a New Zone
Basic Zone Configuration
Network Offering Description
Steps to Provisioning Your Cloud Infrastructure
Page
Advanced Zone Configuration
Page
Steps to Provisioning Your Cloud Infrastructure
Page
NFS
Adding a Pod
Vmfs
Add Cluster OVM
Adding a Cluster
Add Cluster KVM or XenServer
Adding a vSphere Cluster
Add Cluster vSphere
VMware Cluster Size Limit
Steps to Provisioning Your Cloud Infrastructure
Page
Requirements for XenServer, KVM, and OVM Hosts Warning
Adding a Host
Adding a Host XenServer, KVM, or OVM
Adding a XenServer, KVM, or OVM Host
KVM Host Additional Requirements
Adding Primary Storage
Adding a Host vSphere
Adding Secondary Storage
Adding an NFS Secondary Staging Store for Each Zone
Initialize and Test
Steps to Provisioning Your Cloud Infrastructure
Creating a New Compute Offering
Service Offerings
Compute and Disk Service Offerings
Creating a New Disk Offering
Creating a New System Service Offering
System Service Offerings
Modifying or Deleting a Service Offering
For more information, see .7, Stopping and Starting VMs
Page
Page
Setting Up Networking for Users
Overview of Setting Up Networking for Users
About Virtual Networks
Isolated Networks
Network Service Providers
Network Service Providers Support Matrix
Runtime Allocation of Virtual Network Resources
Individual
Support Matrix for an Isolated Network Combination
ACL
Support Matrix for Shared Network Combination
Network Offerings
Support Matrix for Basic Zone
Creating a New Network Offering
Supported Services Description Isolated Shared
See Section Remote Access VPN
Changing the Network Offering on a Guest Network
Creating and Changing a Virtual Router Network Offering
Page
Page
Best Practices for Virtual Machines
Working With Virtual Machines
About Working with Virtual Machines
Monitor VMs for Max Capacity
Install Required Tools and Drivers
VM Lifecycle
Creating VMs
Creating a VM from a template
Configuring Usage of Linked Clones on VMware
Creating a VM from an ISO
Accessing VMs
Appending a Display Name to the Guest VM’s Internal Name
Stopping and Starting VMs
Assigning VMs to Hosts
Affinity Groups
Creating a New Affinity Group
Assign a New VM to an Affinity Group
Change Affinity Group for an Existing VM
Delete an Affinity Group
Virtual Machine Snapshots for VMware
View Members of an Affinity Group
Limitations on VM Snapshots
Configuring VM Snapshots
Using VM Snapshots
Changing the VM Name, OS, or Group
Changing the Service Offering for a VM
CPU and Memory Scaling for Running VMs
Configuring Dynamic CPU and RAM Scaling
How to Dynamically Scale CPU and RAM
Updating Existing VMs
Limitations
Resetting the Virtual Machine Root Volume on Reboot
Moving VMs Between Hosts Manual Live Migration
Working with ISOs
Recovering a Destroyed VM
Deleting VMs
Adding an ISO
Attaching an ISO to a VM
Changing a VMs Base Image
Page
102
Scheduled Maintenance and Maintenance Mode for Hosts
VCenter and Maintenance Mode
XenServer and Maintenance Mode
Working With Hosts
To take a server out of Maintenance Mode
Disabling and Enabling Zones, Pods, and Clusters
Removing Hosts
Working With Hosts
Re-Installing Hosts
Using Cisco UCS as Bare Metal Host CloudPlatform
Maintaining Hypervisors on Hosts
Removing XenServer and KVM Hosts
Registering a UCS Manager
Associating a Profile with a UCS Blade
Changing Host Password
Disassociating a Profile from a UCS Blade
Over-Provisioning and Service Offering Limits
Setting Over-Provisioning Ratios
Limitations on Over-Provisioning in XenServer and KVM
Requirements for Over-Provisioning
Balloon Driver
Service Offering Limits and Over-Provisioning
Vlan Provisioning
Vlan Allocation Example
Adding Non Contiguous Vlan Ranges
Assigning VLANs to Isolated Networks
Default Template
Working with Templates
Creating Templates Overview
Requirements for Templates
Working with Templates
Private and Public Templates
Creating a Template from an Existing Virtual Machine
Creating a Template from a Snapshot
Uploading Templates
Working with Templates
System Preparation for Windows Server 2008 R2
Exporting Templates
Creating a Windows Template
Working with Templates
Page
Working with Templates
System Preparation for Windows Server 2003 R2
Importing Amazon Machine Images
Create a grub entry in /boot/grub/grub.conf
Exit out of chroot
Converting a Hyper-V VM to a Template
Adding Password Management to Your Templates
Deleting Templates
Linux OS Installation
Windows OS Installation
128
Primary Storage
Working With Storage
Storage Overview
Storage Tags
Working With Storage
Fiber Channel support
NFS support Local storage support Storage over-provisioning
Maintenance Mode for Primary Storage
Secondary Storage
Best Practices for Secondary Storage
Changing the Secondary Storage IP Address
Working With Volumes
Creating a New Volume
Using Local Storage for Data Volumes
Changing Secondary Storage Servers
Uploading an Existing Volume to a Virtual Machine
To Create a New Volume
Attaching a Volume
Hypervisor Disk Image Format
Detaching and Moving Volumes
VM Storage Migration
Migrating a Data Volume to a New Storage Pool
Migrating a VM Root Volume to a New Storage Pool
Resizing Volumes
Reset VM to New Root Disk on Reboot
Volume Deletion and Garbage Collection
To enable root disk reset on VM reboot
Working with Snapshots
Automatic Snapshot Creation and Retention
Incremental Snapshots and Backup
Volume Status
Snapshot Job Throttling
Snapshot Restore
VMware Volume Snapshot Performance
Configuring the Usage Server
Working with Usage
Working with Usage
Alerttypeusagesanityresult =
Setting Usage Limits
Globally Configured Limits
Parameter Name Definition
Default Account Resource Limits
Per-Domain Limits
Networking in a Pod
Managing Networks and Traffic
Guest Traffic
Networking in a Zone
Managing Networks and Traffic
Configuring Isolated Guest Network
Basic Zone Physical Network Configuration
Advanced Zone Physical Network Configuration
Configure Public Traffic in an Advanced Zone
Configuring a Shared Guest Network
Using Security Groups to Control Traffic to VMs
About Security Groups
Security Groups in Advanced Zones KVM Only
Limitation
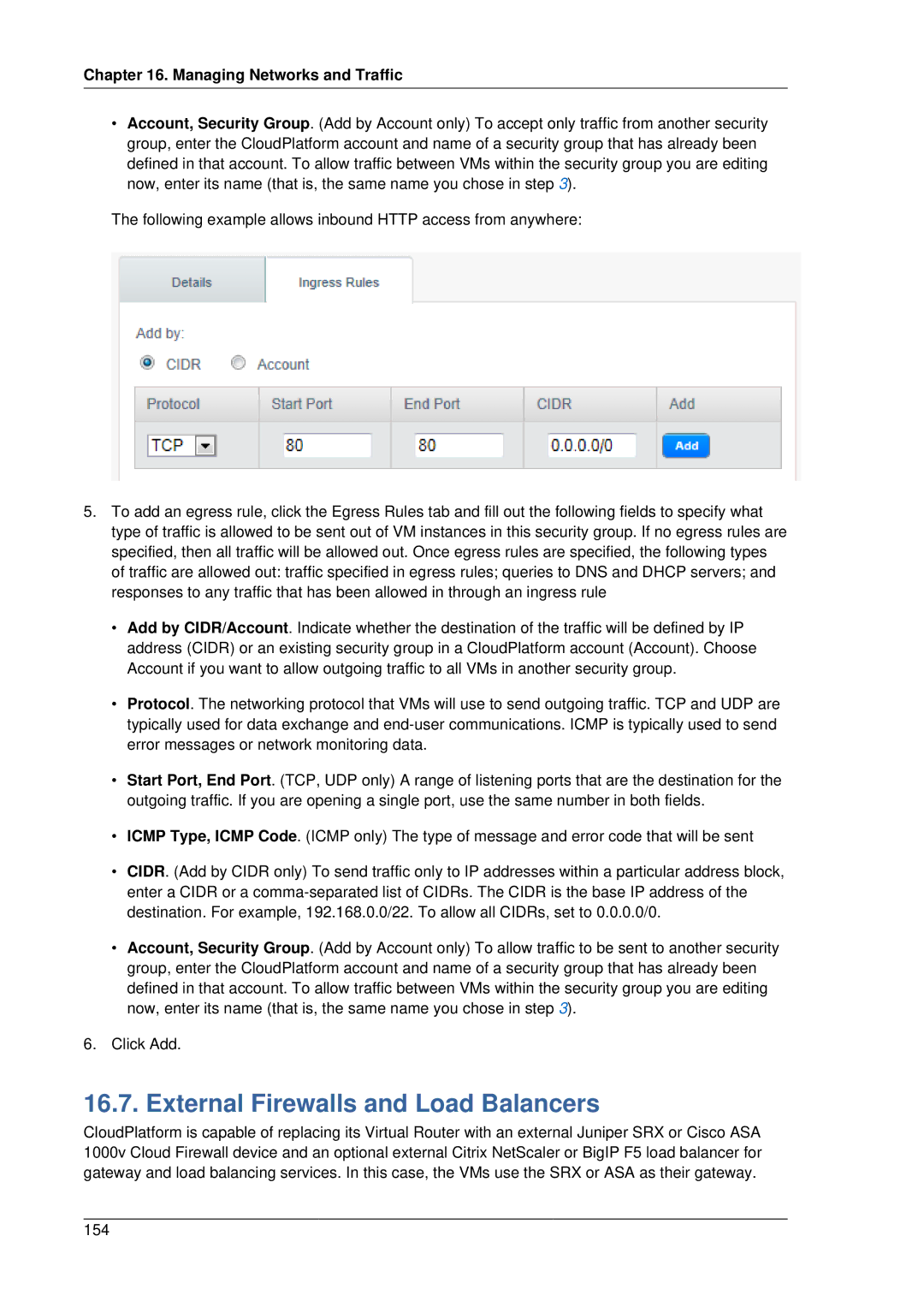
Adding Ingress and Egress Rules to a Security Group
Enabling Security Groups
Adding a Security Group
External Firewalls and Load Balancers
About Using a NetScaler Load Balancer
MPX
Configuring SNMPCommunity String on a Rhel Server
VPX
Initial Setup of External Firewalls and Load Balancers
Load Balancer Rules
Adding a Load Balancer Rule
Configuring AutoScale
Prerequisites
Configuration
Managing Networks and Traffic
Disabling and Enabling an AutoScale Configuration
Updating an AutoScale Configuration
Runtime Considerations
Sticky Session Policies for Load Balancer Rules
Health Checks for Load Balancer Rules
Components of Gslb
Global Server Load Balancing
About Global Server Load Balancing
How Gslb Works in CloudPlatform
Configuring Gslb
For more information, see Configuring a Gslb Virtual Server4
Prerequisites and Guidelines
Enabling Gslb in NetScaler
Adding a Gslb Rule
Assigning Load Balancing Rules to Gslb
Adding an Additional Guest Network
Using Multiple Guest Networks
Reconfiguring Networks in VMs
Selecting the Default Network
Prerequisites
Adding a Network
Removing a Network
Releasing an IP Address
Guest IP Ranges
Acquiring a New IP Address
Reserving Public IP Addresses and VLANs for Accounts
Dedicating IP Address Ranges to an Account
Start IP End IP
Dedicating Vlan Ranges to an Account
Gateway Netmask
IP Reservation in Isolated Guest Networks
IP Reservation Considerations
Reserving an IP Range
Configuring Multiple IP Addresses on a Single NIC
Best Practices
Port Forwarding and StaticNAT Services Changes
Use Cases
Guidelines
Assigning Additional IPs to a VM
Adding Multiple Subnets to a Shared Network
Multiple Subnets in Shared Network
Prerequisites and Guidelines
About Elastic IP
Managing Networks and Traffic
Portable IPs
About Portable IP
Guidelines
Configuring Portable IPs
Acquiring a Portable IP
Enabling or Disabling Static NAT
Static NAT
Transferring Portable IP
Egress Firewall Rules in an Advanced Zone
Configuring an Egress Firewall Rule
IP Forwarding and Firewalling
Deny
Configuring the Default Egress Policy
Allow
Firewall Rules
IP Load Balancing
Port Forwarding
DNS and Dhcp
Remote Access VPN
Configuring Remote Access VPN
Using Remote Access VPN with Windows
Using Remote Access VPN with Mac OS
Setting Up a Site-to-Site VPN Connection
See .27, Configuring a Virtual Private Cloud
Creating and Updating a VPN Customer Gateway Note
Managing Networks and Traffic
Page
Creating a VPN gateway for the VPC
Updating and Removing a VPN Customer Gateway
Creating a VPN Connection Note
Cidr
Managing Networks and Traffic
Restarting and Removing a VPN Connection
Isolation in Advanced Zone Using Private Vlan
About Private Vlan
Creating a PVLAN-Enabled Guest Network
Prerequisites
About Inter-VLAN Routing
Page
Major Components of a VPC
Configuring a Virtual Private Cloud
About Virtual Private Clouds
VPC Network Considerations
Network Architecture in a VPC
Connectivity Options for a VPC
Adding a Virtual Private Cloud
Adding Tiers
Managing Networks and Traffic
Creating ACL Lists
Configuring Network Access Control List
About Network ACL Lists
Creating an ACL Rule
Creating a Tier with Custom ACL List
Assigning a Custom ACL List to a Tier
Adding a Private Gateway to a VPC
Source NAT on Private Gateway
See .27.5.2, ACL on Private Gateway
ACL on Private Gateway
Creating a Static Route
Blacklisting Routes
Deploying VMs to the Tier
Deploying VMs to VPC Tier and Shared Networks
Acquiring a New IP Address for a VPC
Releasing an IP Address Alloted to a VPC
Enabling or Disabling Static NAT on a VPC
Adding Load Balancing Rules on a VPC
Load Balancing Public Traffic Public LB
Creating a Network Offering for Public LB
Creating a Public LB Rule
Load Balancing Tier-to-Tier traffic Internal LB
How Does Internal LB Work in VPC?
Enabling Internal LB on a VPC Tier
Creating an Internal LB Rule
Adding a Port Forwarding Rule on a VPC
Removing Tiers
TCP UDP
Persistent Network Considerations
Persistent Networks
Editing, Restarting, and Removing a Virtual Private Cloud
Creating a Persistent Guest Network
Working with System Virtual Machines
System VM Template
Multiple System VM Support for VMware
Console Proxy
Changing the Console Proxy SSL Certificate and Domain
Working with System Virtual Machines
Configuring the Virtual Router
Virtual Router
Best Practices for Virtual Routers
Upgrading a Virtual Router with System Service Offerings
Secondary Storage VM
HA-Enabled Virtual Machines
System Reliability and High Availability
HA for Management Server
Dedicated HA Hosts
Configuring the API Request Rate
Primary Storage Outage and Data Loss
Secondary Storage Outage and Data Loss
Limiting the Rate of API Requests
Limitations on API Throttling
236
Using Tags to Organize Resources in the Cloud
Managing the Cloud
Managing the Cloud
Setting Configuration Parameters
About Configuration Parameters
Setting Global Configuration Parameters
Setting Local Configuration Parameters
Granular Global Configuration Parameters
Cluster.cpu.allocated.capacity.disablThethr
Changing the Database Configuration
Administrator Alerts
Snmp Alert Details
Customizing Alerts with Global Configuration Settings
Sending Alerts to External Snmp and Syslog Managers
Configuring Snmp and Syslog Managers
Syslog Alert Details
Customizing the Network Domain Name
Deleting an Snmp or Syslog Manager
Stopping and Restarting the Management Server
Provisioning and Authentication API
CloudPlatform API
Allocators
User Data and Meta Data
CloudPlatform API
Tuning
Performance Monitoring
Increase Management Server Maximum Memory
Set Database Buffer Pool Size
Set and Monitor Total VM Limits per Host
Configure XenServer dom0 Memory
Tuning
Troubleshooting
Events
Event Logs
Event Notification
Long Running Job Events
Troubleshooting
Standard Events
Event Log Queries
Deleting and Archiving Events and Alerts
Permissions
Procedure
Working with Server Logs
Using cloud-bugtool
Symptom
Log Collection Utility cloud-bugtool
Data Loss on Exported Primary Storage
Recovering a Lost Virtual Router
Maintenance mode not working on vCenter
Solution
Cause
Unable to power on virtual machine on VMware
Unable to deploy VMs from uploaded vSphere template
Load balancer rules fail after changing network offering
Appendix A. Event Types
260
Appendix B. Alerts
Appendix B. Alerts