|
|
|
Configuring | Configuring NAT mode |
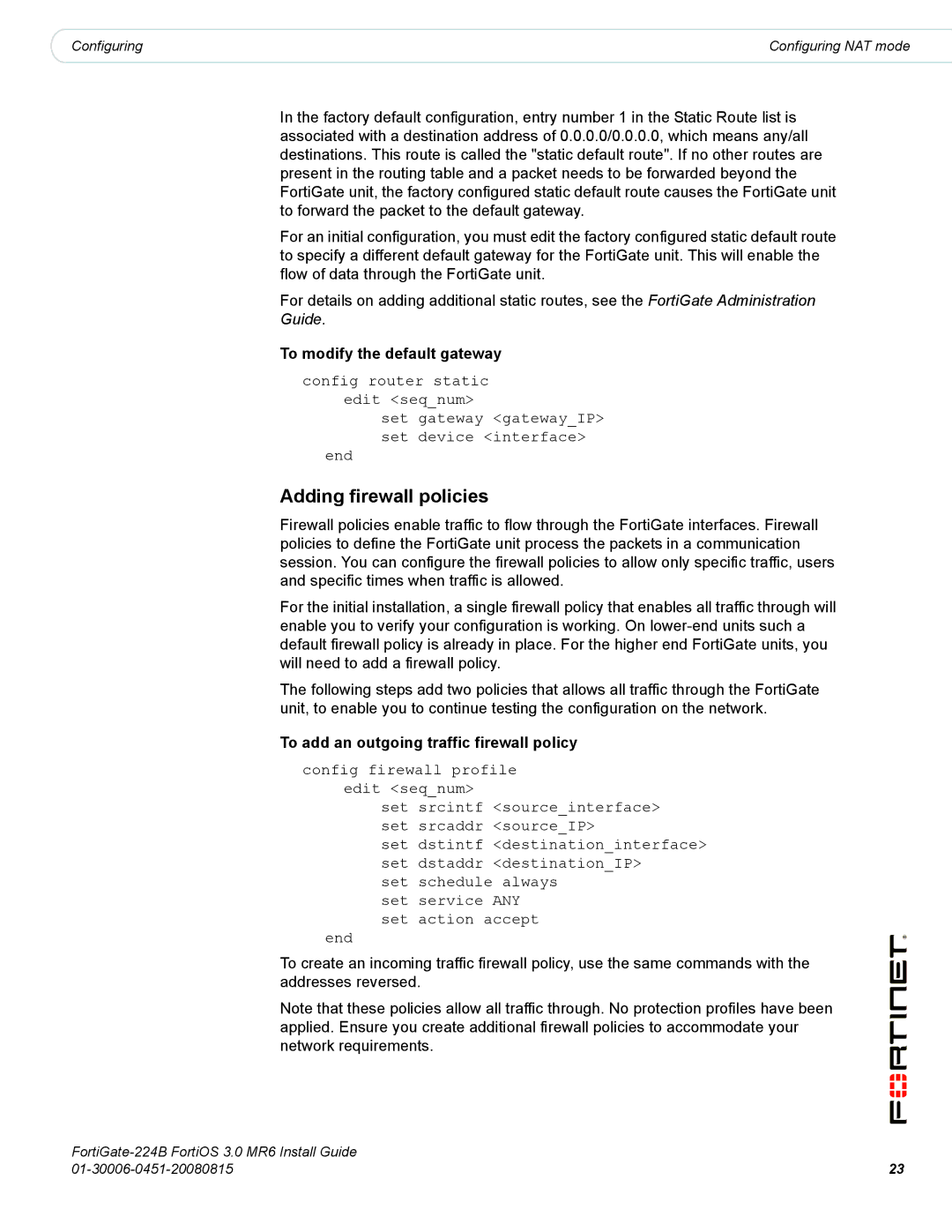
In the factory default configuration, entry number 1 in the Static Route list is associated with a destination address of 0.0.0.0/0.0.0.0, which means any/all destinations. This route is called the "static default route". If no other routes are present in the routing table and a packet needs to be forwarded beyond the FortiGate unit, the factory configured static default route causes the FortiGate unit to forward the packet to the default gateway.
For an initial configuration, you must edit the factory configured static default route to specify a different default gateway for the FortiGate unit. This will enable the flow of data through the FortiGate unit.
For details on adding additional static routes, see the FortiGate Administration Guide.
To modify the default gateway
config router static edit <seq_num>
set gateway <gateway_IP> set device <interface>
end
Adding firewall policies
Firewall policies enable traffic to flow through the FortiGate interfaces. Firewall policies to define the FortiGate unit process the packets in a communication session. You can configure the firewall policies to allow only specific traffic, users and specific times when traffic is allowed.
For the initial installation, a single firewall policy that enables all traffic through will enable you to verify your configuration is working. On
The following steps add two policies that allows all traffic through the FortiGate unit, to enable you to continue testing the configuration on the network.
To add an outgoing traffic firewall policy
config firewall profile
edit <seq_num>
set srcintf <source_interface> set srcaddr <source_IP>
set dstintf <destination_interface> set dstaddr <destination_IP>
set schedule always set service ANY set action accept
end
To create an incoming traffic firewall policy, use the same commands with the addresses reversed.
Note that these policies allow all traffic through. No protection profiles have been applied. Ensure you create additional firewall policies to accommodate your network requirements.
| |
23 |