SIEMENS se5880 Ethernet Security Router | Chapter 6 Security Setup |
User’s Guide | IKE/IPSec Configuration |
|
|
IKE Proposals Definition
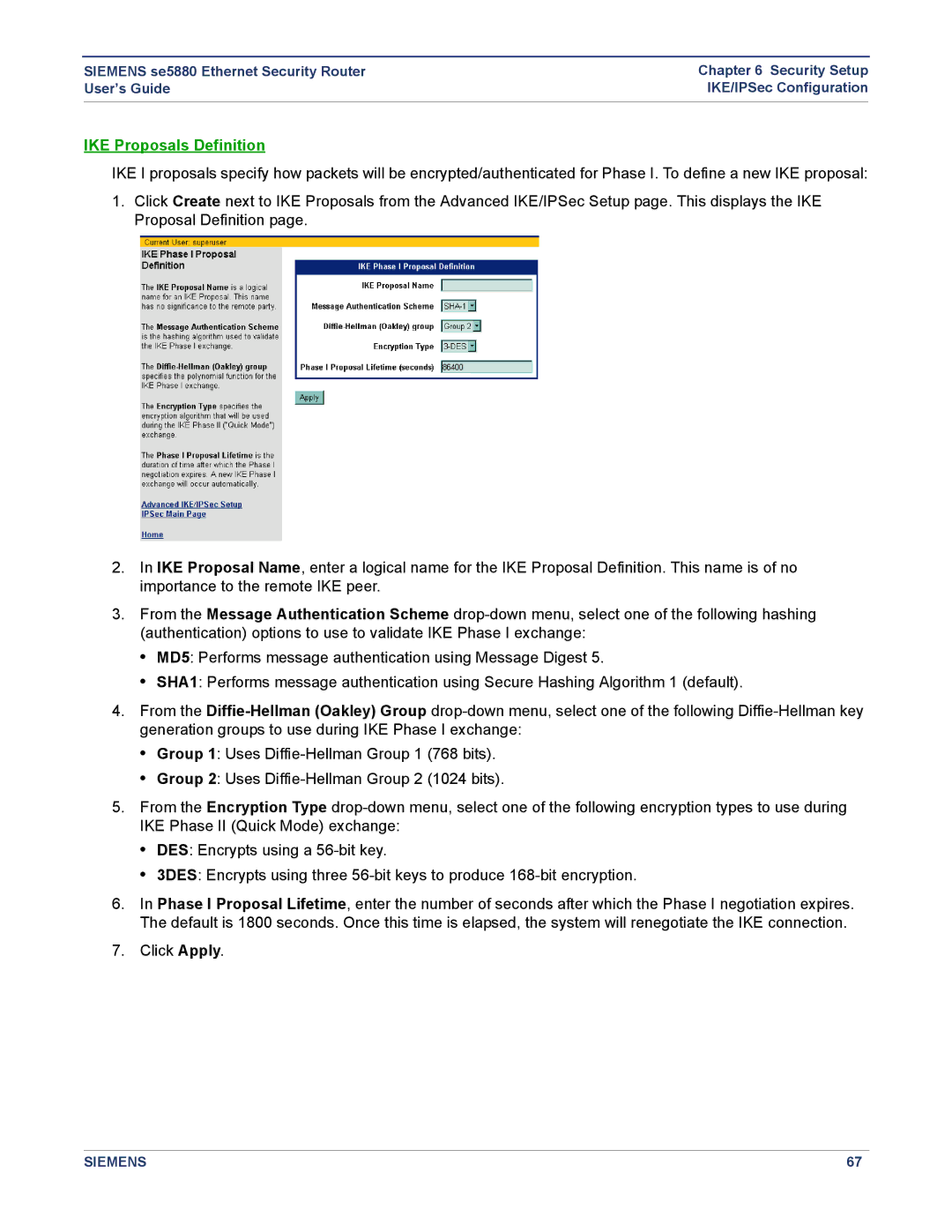
IKE I proposals specify how packets will be encrypted/authenticated for Phase I. To define a new IKE proposal:
1.Click Create next to IKE Proposals from the Advanced IKE/IPSec Setup page. This displays the IKE Proposal Definition page.
2.In IKE Proposal Name, enter a logical name for the IKE Proposal Definition. This name is of no importance to the remote IKE peer.
3.From the Message Authentication Scheme
•MD5: Performs message authentication using Message Digest 5.
•SHA1: Performs message authentication using Secure Hashing Algorithm 1 (default).
4.From the
•Group 1: Uses
•Group 2: Uses
5.From the Encryption Type
•DES: Encrypts using a
•3DES: Encrypts using three
6.In Phase I Proposal Lifetime, enter the number of seconds after which the Phase I negotiation expires. The default is 1800 seconds. Once this time is elapsed, the system will renegotiate the IKE connection.
7.Click Apply.
SIEMENS | 67 |