Identifying the user
Identifying the user
This section describes methods for authorising and tracking users and preventing them from changing their identity on the network.
IP spoofing and tracking
Unknown users who attempt to change IP
Changing IP address for malicious reasons is most commonly called IP spoofing, and is also known as ARP spoofing, ARP poisoning, and ARP poison routing (APR). The net result is the same for all of these: the victim ends up with false information in its ARP table.
The trouble with ARP
IP Spoofing takes advantage of the inherently insecure design of ARP. In an Ethernet network, a client may use a Gratuitous ARP (GARP), or merely send an ARP request or reply with false information, to announce a phoney identity to the local subnet.
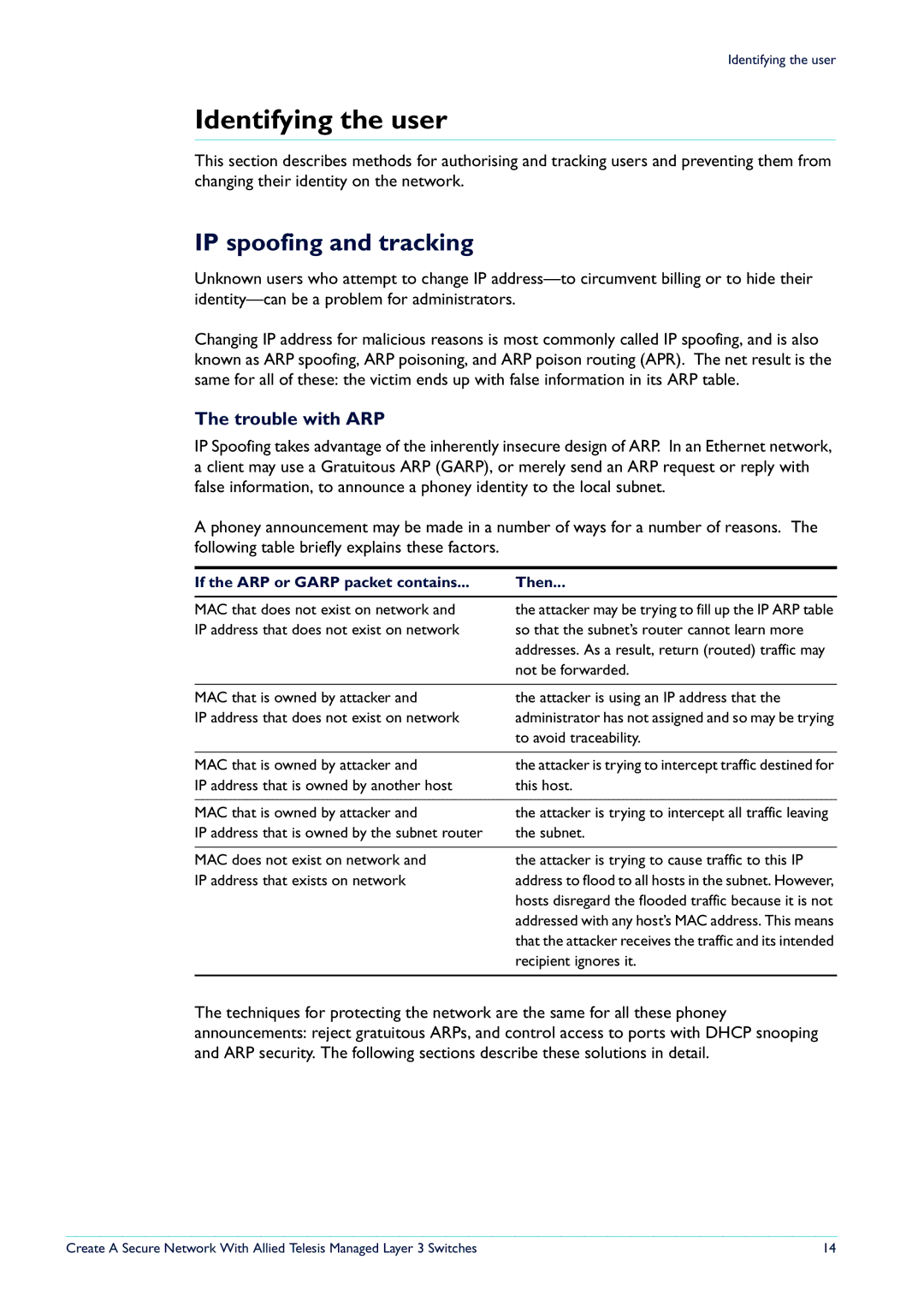
A phoney announcement may be made in a number of ways for a number of reasons. The following table briefly explains these factors.
If the ARP or GARP packet contains... | Then... |
MAC that does not exist on network and IP address that does not exist on network
the attacker may be trying to fill up the IP ARP table so that the subnet’s router cannot learn more addresses. As a result, return (routed) traffic may not be forwarded.
MAC that is owned by attacker and | the attacker is using an IP address that the |
IP address that does not exist on network | administrator has not assigned and so may be trying |
| to avoid traceability. |
|
|
MAC that is owned by attacker and | the attacker is trying to intercept traffic destined for |
IP address that is owned by another host | this host. |
|
|
MAC that is owned by attacker and | the attacker is trying to intercept all traffic leaving |
IP address that is owned by the subnet router | the subnet. |
|
|
MAC does not exist on network and | the attacker is trying to cause traffic to this IP |
IP address that exists on network | address to flood to all hosts in the subnet. However, |
| hosts disregard the flooded traffic because it is not |
| addressed with any host’s MAC address. This means |
| that the attacker receives the traffic and its intended |
| recipient ignores it. |
|
|
The techniques for protecting the network are the same for all these phoney announcements: reject gratuitous ARPs, and control access to ports with DHCP snooping and ARP security. The following sections describe these solutions in detail.
Create A Secure Network With Allied Telesis Managed Layer 3 Switches | 14 |