Chapter 4 Configuring the VSA
Configuration Tasks
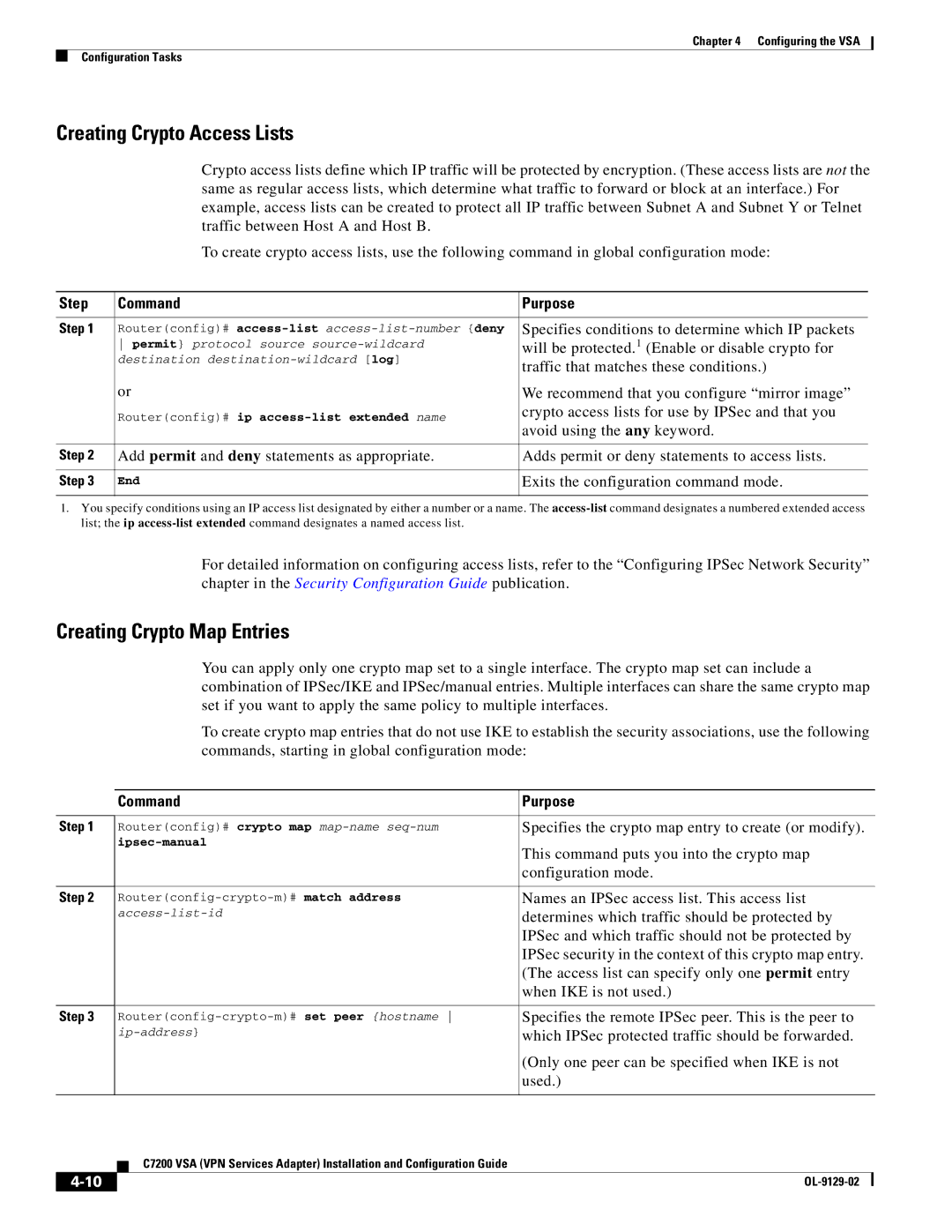
Creating Crypto Access Lists
Crypto access lists define which IP traffic will be protected by encryption. (These access lists are not the same as regular access lists, which determine what traffic to forward or block at an interface.) For example, access lists can be created to protect all IP traffic between Subnet A and Subnet Y or Telnet traffic between Host A and Host B.
To create crypto access lists, use the following command in global configuration mode:
Step | Command | Purpose |
|
|
|
Step 1 | Router(config)# | Specifies conditions to determine which IP packets |
| permit} protocol source | will be protected.1 (Enable or disable crypto for |
| destination | traffic that matches these conditions.) |
|
| |
| or | We recommend that you configure “mirror image” |
| Router(config)# ip | crypto access lists for use by IPSec and that you |
| avoid using the any keyword. | |
|
| |
|
|
|
Step 2 | Add permit and deny statements as appropriate. | Adds permit or deny statements to access lists. |
|
|
|
Step 3 | End | Exits the configuration command mode. |
|
|
|
1.You specify conditions using an IP access list designated by either a number or a name. The
For detailed information on configuring access lists, refer to the “Configuring IPSec Network Security” chapter in the Security Configuration Guide publication.
Creating Crypto Map Entries
Step 1
Step 2
Step 3
You can apply only one crypto map set to a single interface. The crypto map set can include a combination of IPSec/IKE and IPSec/manual entries. Multiple interfaces can share the same crypto map set if you want to apply the same policy to multiple interfaces.
To create crypto map entries that do not use IKE to establish the security associations, use the following commands, starting in global configuration mode:
Command | Purpose |
|
|
Router(config)# crypto map | Specifies the crypto map entry to create (or modify). |
This command puts you into the crypto map | |
| |
| configuration mode. |
|
|
Names an IPSec access list. This access list | |
determines which traffic should be protected by | |
| IPSec and which traffic should not be protected by |
| IPSec security in the context of this crypto map entry. |
| (The access list can specify only one permit entry |
| when IKE is not used.) |
|
|
Specifies the remote IPSec peer. This is the peer to | |
which IPSec protected traffic should be forwarded. | |
| (Only one peer can be specified when IKE is not |
| used.) |
|
|
C7200 VSA (VPN Services Adapter) Installation and Configuration Guide
|
| |
|