Chapter 4 Configuring the VSA
Basic IPSec Configuration Illustration
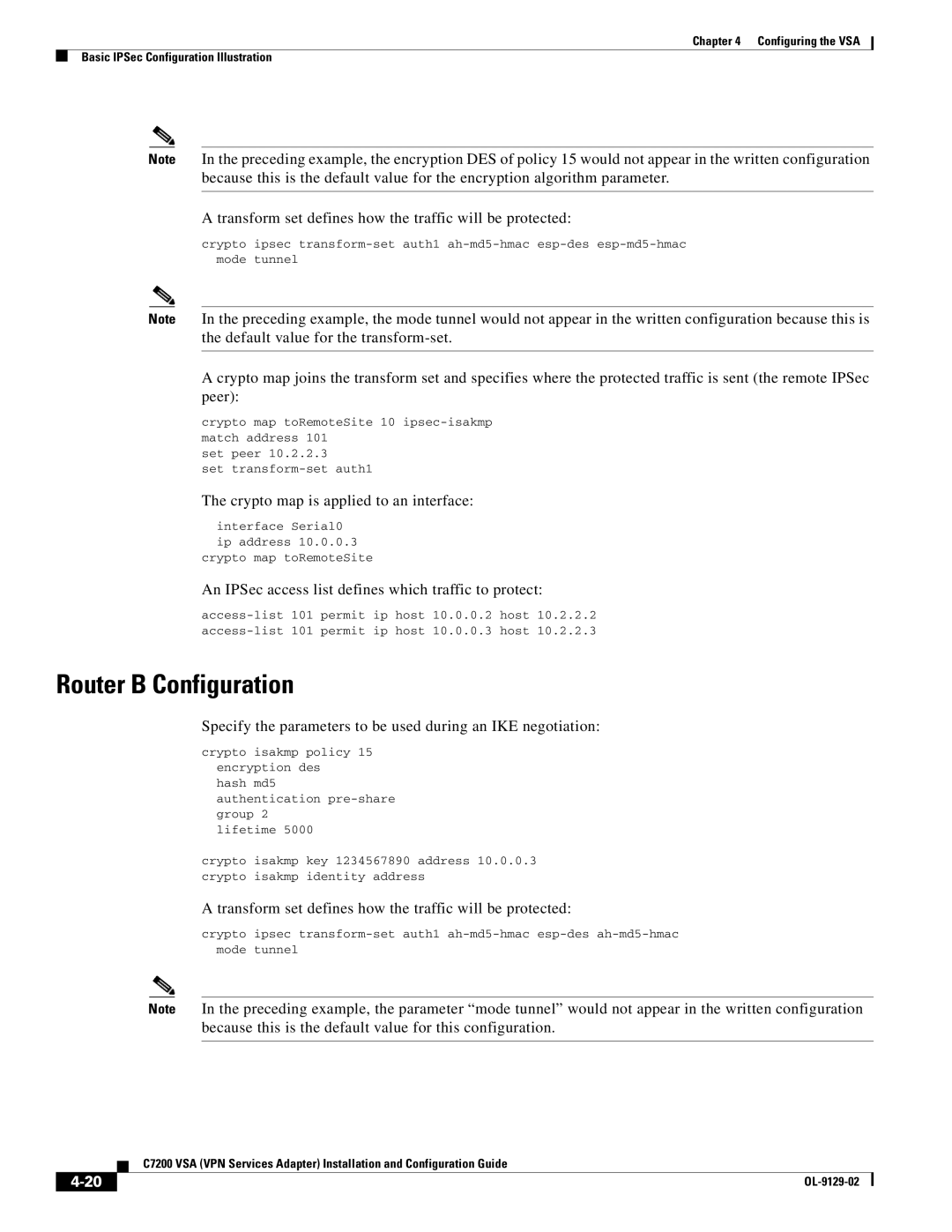
Note In the preceding example, the encryption DES of policy 15 would not appear in the written configuration because this is the default value for the encryption algorithm parameter.
A transform set defines how the traffic will be protected:
crypto ipsec
Note In the preceding example, the mode tunnel would not appear in the written configuration because this is the default value for the
A crypto map joins the transform set and specifies where the protected traffic is sent (the remote IPSec peer):
crypto map toRemoteSite 10
set peer 10.2.2.3
set
The crypto map is applied to an interface:
interface Serial0
ip address 10.0.0.3
crypto map toRemoteSite
An IPSec access list defines which traffic to protect:
Router B Configuration
Specify the parameters to be used during an IKE negotiation:
crypto isakmp policy 15 encryption des
hash md5
authentication
lifetime 5000
crypto isakmp key 1234567890 address 10.0.0.3 crypto isakmp identity address
A transform set defines how the traffic will be protected:
crypto ipsec
Note In the preceding example, the parameter “mode tunnel” would not appear in the written configuration because this is the default value for this configuration.
C7200 VSA (VPN Services Adapter) Installation and Configuration Guide
|
| |
|