Using the Belkin Wireless Client Utility
Securing your Wi-Fi Network
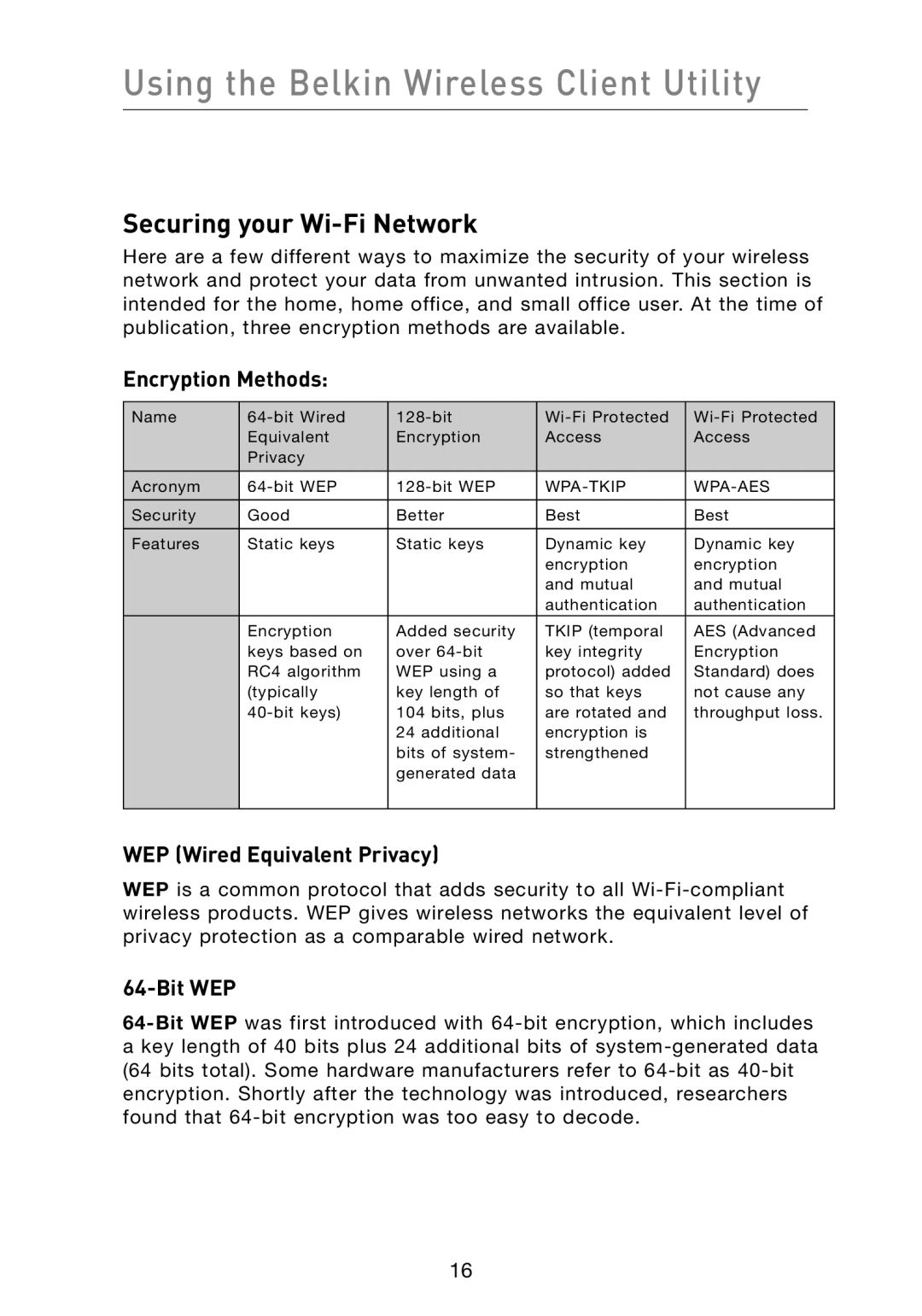
Here are a few different ways to maximize the security of your wireless network and protect your data from unwanted intrusion. This section is intended for the home, home office, and small office user. At the time of publication, three encryption methods are available.
Encryption Methods:
Name | ||||
| Equivalent | Encryption | Access | Access |
| Privacy |
|
|
|
Acronym |
|
| ||
Security | Good | Better | Best | Best |
Features | Static keys | Static keys | Dynamic key | Dynamic key |
|
|
| encryption | encryption |
|
|
| and mutual | and mutual |
|
|
| authentication | authentication |
| Encryption | Added security | TKIP (temporal | AES (Advanced |
| keys based on | over | key integrity | Encryption |
| RC4 algorithm | WEP using a | protocol) added | Standard) does |
| (typically | key length of | so that keys | not cause any |
| 104 bits, plus | are rotated and | throughput loss. | |
|
| 24 additional | encryption is |
|
|
| bits of system- | strengthened |
|
|
| generated data |
|
|
WEP (Wired Equivalent Privacy)
WEP is a common protocol that adds security to all
64-Bit WEP
16