3 Module Objectives
This section describes the assurance levels for each of the areas described in the FIPS
3.1 Security Levels
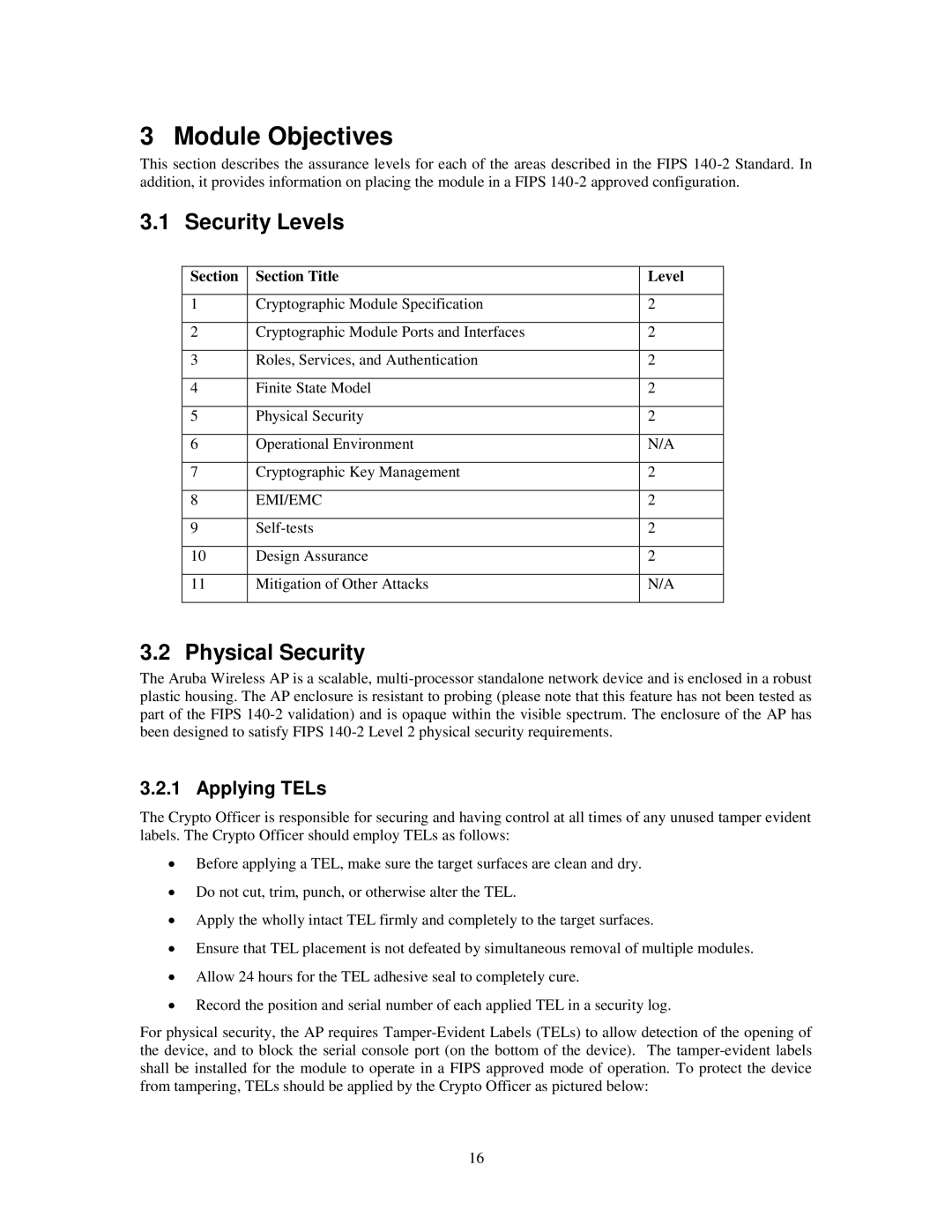
Section | Section Title | Level |
|
|
|
1 | Cryptographic Module Specification | 2 |
|
|
|
2 | Cryptographic Module Ports and Interfaces | 2 |
|
|
|
3 | Roles, Services, and Authentication | 2 |
|
|
|
4 | Finite State Model | 2 |
|
|
|
5 | Physical Security | 2 |
|
|
|
6 | Operational Environment | N/A |
|
|
|
7 | Cryptographic Key Management | 2 |
|
|
|
8 | EMI/EMC | 2 |
|
|
|
9 | 2 | |
|
|
|
10 | Design Assurance | 2 |
|
|
|
11 | Mitigation of Other Attacks | N/A |
|
|
|
3.2 Physical Security
The Aruba Wireless AP is a scalable,
3.2.1 Applying TELs
The Crypto Officer is responsible for securing and having control at all times of any unused tamper evident labels. The Crypto Officer should employ TELs as follows:
∙Before applying a TEL, make sure the target surfaces are clean and dry.
∙Do not cut, trim, punch, or otherwise alter the TEL.
∙Apply the wholly intact TEL firmly and completely to the target surfaces.
∙Ensure that TEL placement is not defeated by simultaneous removal of multiple modules.
∙Allow 24 hours for the TEL adhesive seal to completely cure.
∙Record the position and serial number of each applied TEL in a security log.
For physical security, the AP requires
16