4.1.2 User Authentication
Authentication for the User role depends on the module configuration. When the module is configured as a Remote Mesh Portal FIPS mode and Remote Mesh Point FIPS mode, the User role is authenticated via the WPA2
4.1.3 Wireless Client Authentication
The wireless client role defined in each of FIPS approved modes authenticates to the module via WPA2. Please notice that WEP and/or Open System configurations are not permitted in FIPS mode. In advanced Remote AP configuration, when Remote AP cannot communicate with the controller, the wireless client role authenticates to the module via
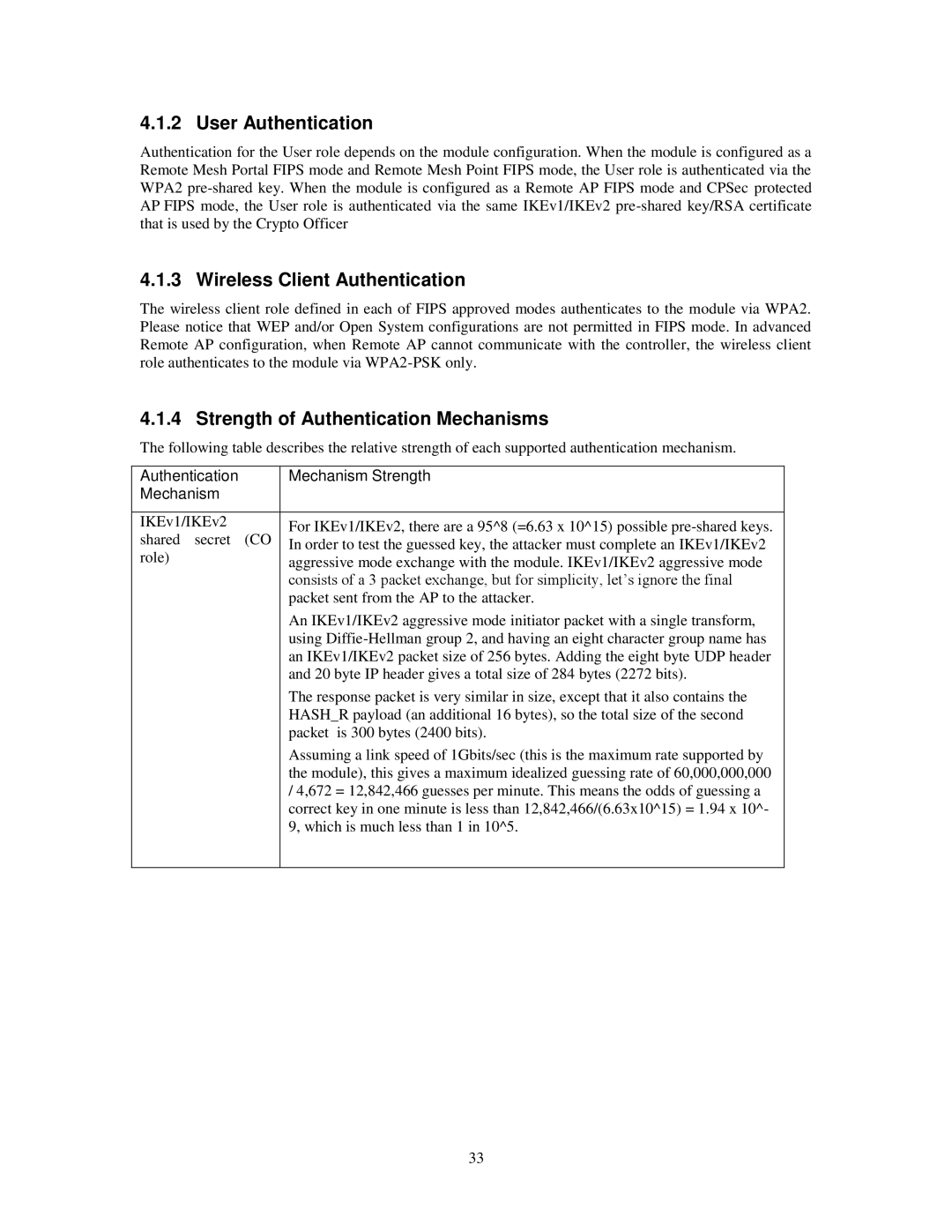
4.1.4 Strength of Authentication Mechanisms
The following table describes the relative strength of each supported authentication mechanism.
Authentication |
| Mechanism Strength | |
Mechanism |
|
| |
|
|
| |
IKEv1/IKEv2 |
| For IKEv1/IKEv2, there are a 95^8 (=6.63 x 10^15) possible | |
shared secret | (CO | ||
In order to test the guessed key, the attacker must complete an IKEv1/IKEv2 | |||
role) |
| ||
| aggressive mode exchange with the module. IKEv1/IKEv2 aggressive mode | ||
|
| ||
|
| consists of a 3 packet exchange, but for simplicity, let’s ignore the final | |
|
| packet sent from the AP to the attacker. | |
|
| An IKEv1/IKEv2 aggressive mode initiator packet with a single transform, | |
|
| using | |
|
| an IKEv1/IKEv2 packet size of 256 bytes. Adding the eight byte UDP header | |
|
| and 20 byte IP header gives a total size of 284 bytes (2272 bits). | |
|
| The response packet is very similar in size, except that it also contains the | |
|
| HASH_R payload (an additional 16 bytes), so the total size of the second | |
|
| packet is 300 bytes (2400 bits). |
Assuming a link speed of 1Gbits/sec (this is the maximum rate supported by the module), this gives a maximum idealized guessing rate of 60,000,000,000
/4,672 = 12,842,466 guesses per minute. This means the odds of guessing a correct key in one minute is less than 12,842,466/(6.63x10^15) = 1.94 x 10^- 9, which is much less than 1 in 10^5.
33