202-10051-01, March
202-10051-01, March
Product and Publication Details
This page intentionally left blank
Contents
Chapter Optimizing Wireless Connectivity and Security
Appendix C Preparing Your Network
Appendix D Wireless Networking Basics
Glossary
This page intentionally left blank
Chapter About This Manual
Audience, Scope, Conventions, and Formats
How to Use This Manual
How to Print this Manual
Printing a Page in the Html View
This page intentionally left blank
Getting to Know Your Netgear Wireless Router
Package Contents
Front Panel
Status Light Descriptions
OFF
Rear Panel
WGR826V Rear Panel
First, Connect the Wireless Router to Your Network
Chapter Connecting the Router to the Internet
Prepare to Install Your Wireless Router
DEOH��
Restart Your Network in the Correct Sequence
202 10051 01, March
Open a Browser and LOG in to the Router
Settings main
Configure Your Wireless Router to Connect to the Internet
Configure the Wireless Settings
Wireless Settings menu
Now, Set Up a Computer for Wireless Connectivity
Troubleshooting Tips
Make sure the Ethernet cables are securely plugged
This page intentionally left blank
Firewall Rules
Chapter Content Filtering
Content Filtering Overview
Firewall Rules menu
Content Filtering
Outbound Services
Outbound Services menu
Content Filtering
Inbound Services
Inbound Services menu
Content Filtering
Blocking Access to Internet Sites
Block Sites menu
Blocking Access to Internet Services
Block Services menu
Configuring a User Defined Service
Add Services menu
Scheduling When Blocking Will Be Enforced
Schedule menu
Viewing Logs of Web Access or Attempted Web Access
Logs menu
Log entries are described in Table
Configuring E-Mail Alert and Web Access Log Notifications
Email menu
Content Filtering
Content Filtering
Optimizing Wireless Connectivity and Security
Observe Performance, Placement, and Range Guidelines
Implement Appropriate Wireless Security
WGR826V wireless data security options
Understanding Wireless Settings
Basic Wireless Security Options
Default Factory Settings
802.11g Wireless Network Name Ssid
Changing the Administrator Password
Chapter Doing Basic Router Housekeeping
Reviewing the Router Status
Router Status
Doing Basic Router Housekeeping
Reviewing the Attached Devices
Attached Devices
Backing up Your Settings
Backup Settings
Doing Basic Router Housekeeping
Using Diagnostics
Diagnostics
Reviewing the VoIP and QoS Settings
VoIP and QoS Settings
Doing Basic Router Housekeeping
Doing Basic Router Housekeeping
Phone Status
Click Digit Map to look at the digit map configured
Doing Basic Router Housekeeping
Setting Up Advanced Router Configurations
Using the LAN IP Setup Options
Configuring LAN TCP/IP Setup Parameters
Using the Router as a Dhcp server
Configuring Static Routes
Using Address Reservation
Static Route Summary Table
Configuring WAN Setup Options
Setting Up a Default DMZ Server
WAN Setup menu
Setting the MTU Size
Port Triggering
Port Triggering menus
Access Control List
Access Control pages
UPnP Setting
UPnP Settings
Setting Up Advanced Router Configurations
This page intentionally left blank
Basic Functioning
Chapter Troubleshooting Common Problems
Power Light Not On
LAN or Internet WAN Port Lights Not On
Troubleshooting the Web Configuration Interface
Lights Never Turn Off
Troubleshooting the ISP Connection
Troubleshooting Common Problems
Troubleshooting a TCP/IP Network Using a Ping Utility
Testing the LAN Path to Your Router
Testing the Path from Your Computer to a Remote Device
Restoring the Default Configuration and Password
This page intentionally left blank
Appendix a Technical Specifications
Interface Specifications
Technical Specifications
Related Publications Basic Router Concepts
What is a Router?
Appendix B Network, Routing, and Firewall Basics
IP Addresses and the Internet
Routing Information Protocol
Figure B-1 Three Main Address Classes
Netmask
Subnet Addressing
Figure B-2 Example of Subnetting a Class B Address
Netmask Notation Translation Table for One Octet
Private IP Addresses
Single IP Address Operation Using NAT
Figure B-3 Single IP Address Operation Using NAT
Domain Name Server
MAC Addresses and Address Resolution Protocol
Related Documents
IP Configuration by Dhcp
Internet Security and Firewalls
Ethernet Cabling
What is a Firewall?
Denial of Service Attack
Stateful Packet Inspection
Table B-1 UTP Ethernet cable wiring, straight-through
Category 5 Cable Quality
Inside Twisted Pair Cables
Figure B-4illustrates straight-through twisted pair cable
Uplink Switches, Crossover Cables, and MDI/MDIX Switching
Network, Routing, and Firewall Basics
Network, Routing, and Firewall Basics
What You Need To Use a Router with a Broadband Modem
Computer Network Configuration Requirements
Appendix C Preparing Your Network
Cabling and Computer Hardware
Internet Configuration Requirements
Where Do I Get the Internet Configuration Parameters?
Preparing Your Computers for TCP/IP Networking
Record Your Internet Connection Information
Configuring Windows 95, 98, and Me for TCP/IP Networking
Install or Verify Windows Networking Components
Preparing Your Network
Preparing Your Network
Locate your Network Neighborhood icon
Selecting Windows’ Internet Access Method
Verifying TCP/IP Properties
Configuring Windows NT4, 2000 or XP for IP Networking
Dhcp Configuration of TCP/IP in Windows XP, 2000, or NT4
Dhcp Configuration of TCP/IP in Windows XP
Preparing Your Network
Dhcp Configuration of TCP/IP in Windows
Preparing Your Network
Obtain an IP address automatically is selected
Dhcp Configuration of TCP/IP in Windows NT4
Preparing Your Network
Verifying TCP/IP Properties for Windows XP, 2000, and NT4
TCP/IP Properties dialog box now displays
MacOS
Configuring the Macintosh for TCP/IP Networking
MacOS 8.6 or
Verifying TCP/IP Properties for Macintosh Computers
Verifying the Readiness of Your Internet Account
Are Login Protocols Used?
What Is Your Configuration Information?
Select the Gateway tab
Preparing Your Network
Restarting the Network
Preparing Your Network
Infrastructure Mode
Appendix D Wireless Networking Basics
Wireless Networking Overview
Network Name Extended Service Set Identification Essid
Authentication and WEP Data Encryption
Ad Hoc Mode Peer-to-Peer Workgroup
Authentication
Open System Authentication
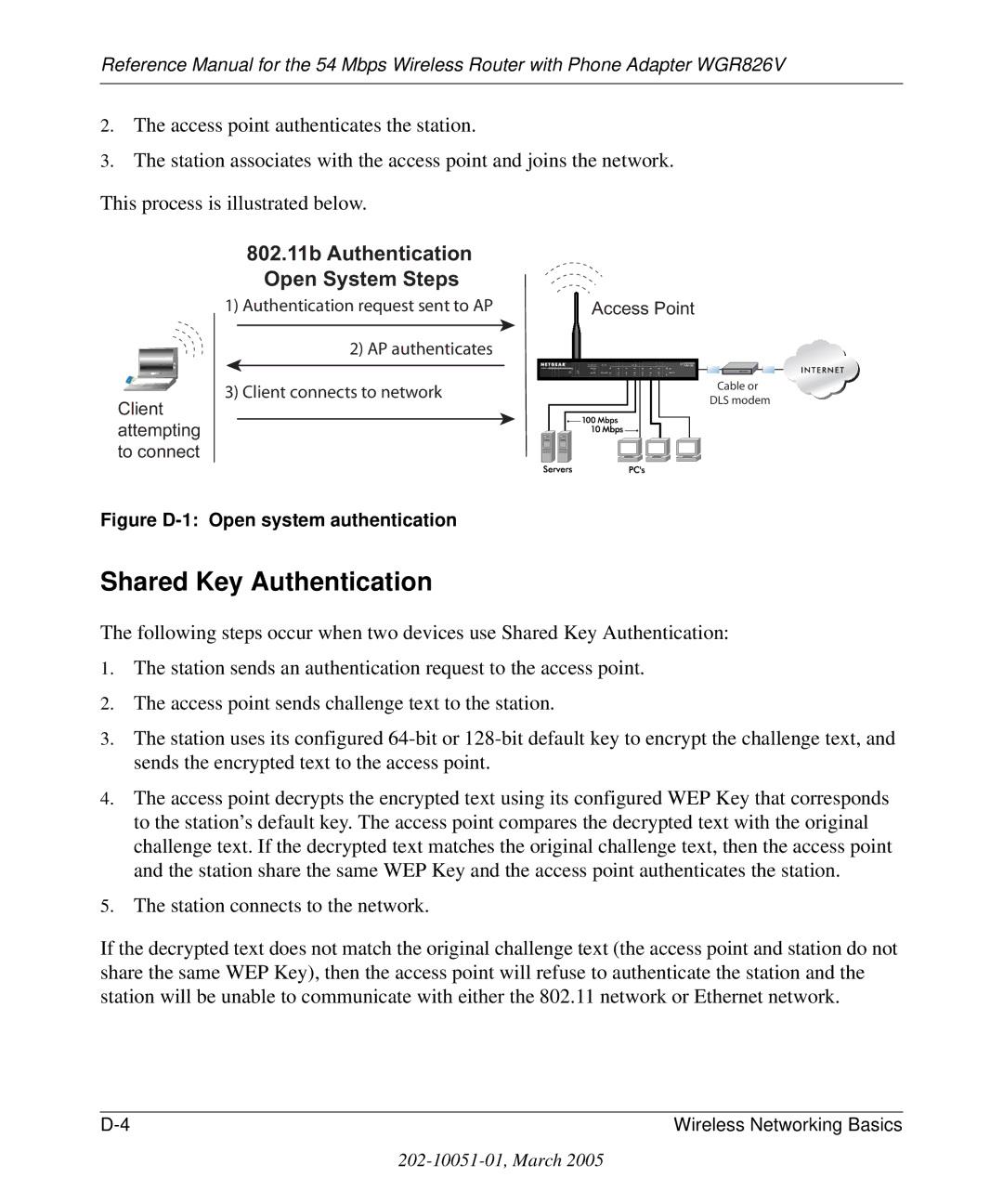
802.11b Authentication Open System Steps
802.11b Authentication Shared Key Steps
Key Size
Wireless Channels
WEP Configuration Options
WPA and WPA2 Wireless Security
How Does WPA Compare to WEP?
What are the Key Features of WPA and WPA2 Security?
How Does WPA Compare to WPA2 Ieee 802.11i?
Wireless Networking Basics
Figure D-3 WPA/WPA2 Overview
Access point replies with an EAP-request identity message
WPA/WPA2 Data Encryption Key Management
Temporal Key Integrity Protocol Tkip
Is WPA/WPA2 Perfect?
Product Support for WPA/WPA2
Changes to Wireless Access Points
Changes to Wireless Client Programs
Glossary
802.11e Standard
Access Point AP
Bridge
CSMA/CD Carrier Sense Multiple Action/Collision Detection
Essid more commonly referred to as Ssid Short Set Identifier
Ieee Institute of Electrical and Electronics Engineers
MAC Media Access Control
PHY
Range
Site survey
TCP/IP
War Driving
Wi-Fi Protected Access and Ieee 802.11i Comparison
Wi-Fi Protected Access in Mixed Mode Deployment
This page intentionally left blank