Text Part Number
Americas Headquarters
Copyright 2007-2009 Cisco Systems, Inc. All rights reserved
RPR
Startup Configuration File
Iii
Configuring POS Interface Framing Mode
Understanding VLANs
Configuring Encapsulation over EtherChannel or POS Channel
IP ACLs
Vii
Role of Sonet Circuits
Viii
Configuration Guidelines
Using Technical Support C-1
Page
11-7
11-3
11-4
11-5
14-22
14-13
14-17
14-18
11-12
10-5
10-6
11-11
17-8
13-3
17-7
Date
Preface
Revision History
This section provides the following information
Related Documentation
Document Objectives
Audience
Italic
Document Conventions
Convention Application
Boldface
Warnung Wichtige Sicherheitshinweise
Bewaar Deze Instructies
Aviso Instruções Importantes DE Segurança
Avvertenza Importanti Istruzioni Sulla Sicurezza
Page
GEM Disse Anvisninger
Viii
Cisco Optical Networking Product Documentation CD-ROM
Where to Find Safety and Warning Information
Obtaining Optical Networking Information
Page
ML-Series Card Description
Overview of the ML-Series Card
IRB
ML-Series Feature List
Bundling the two POS ports LEX encapsulation only
Cisco IOS Release 12.228SV
Key ML-Series Features
Cisco IOS
GFP-F Framing
Rmon
Link Aggregation FEC and POS
TL1
Refresh
CTC Operations on the ML-Series Card
Displaying ML-Series POS Statistics in CTC
ML-Series POS Statistics Fields and Buttons
ML-Series Ethernet Statistics Fields and Buttons
Displaying ML-Series Ethernet Statistics in CTC
Button Description
CTC
Provisioning Sonet Circuits
Displaying Sonet Alarms
Displaying J1 Path Trace
78-18133-01
Page
Cisco IOS on the ML-Series Card
Initial Configuration of the ML-Series Card
Hardware Installation
Telnetting to the Node IP Address and Slot Number
Opening a Cisco IOS Session Using CTC
CTC Node View Showing IP Address
Telnetting to a Management Port
RJ-11 Pin RJ-45 Pin
Connecting a PC or Terminal to the Console Port
ML-Series IOS CLI Console Port
RJ-11 to RJ-45 Console Cable Adapter
Startup Configuration File
Router enable
Passwords
Configuring the Management Port
Command Purpose
Nvram
Configuring the Hostname
Click the IOS startup config button
Loading a Cisco IOS Startup Configuration File Through CTC
Database Restore of the Startup Configuration File
Cisco IOS Command Modes
Enter the line console
Mode What You Use It For How to Access Prompt
Enter the configure terminal
Interface fastethernet 0 for
Getting Help
Using the Command Modes
Router# configure ?
Exit
Page
MAC Addresses
Configuring Interfaces on the ML-Series Card
General Interface Guidelines
MLSeries# show interfaces fastethernet
Interface Port ID
MLSeriesconfig# interface fastethernet number
Basic Interface Configuration
MLSeries# configure terminal
Configuring the Fast Ethernet Interfaces
Basic Fast Ethernet and POS Interface Configuration
Configuring the POS Interfaces
Hdlc
Monitoring Operations on the Fast Ethernet Interfaces
FCR
Example 4-3 show controller Command Output
Daytona# show run interface fastethernet
Example 4-4 show run interface Command Output
Available Circuit Sizes and Combinations
Configuring POS on the ML-Series Card
Understanding POS on the ML-Series Card
Mbps STS-1 STS-1-1v STS-1-2v
J1 Path Trace, and Sonet Alarms
Lcas Support
Ccat High Order Vcat High Order
GFP-F Framing Hdlc Framing
Configuring the POS Interface
Encapsulations LEX default Cisco Hdlc
CRC Sizes Bit default None FCS disabled
Admindown
Configuring POS Interface Framing Mode
Framing mode changes on POS ports are
Allowed only when the interface is shut down
GFP default-The ML-Series card supports
Sets the framing mode employed by the ONS
Not a keyword choice in the command. The no
Form of the command sets the framing mode
Configuring Sonet Alarms
Sonet Alarms
All -All alarms/signals
Configuring Sonet Delay Triggers
Monitoring and Verifying POS
Hdlc
Page
These sections describe how the spanning-tree features work
Configuring STP and Rstp on the ML-Series Card
STP Features
Bridge Protocol Data Units
STP Overview
Supported STP Instances
Election of the Root Switch
Bit
Bridge ID, Switch Priority, and Extended System ID
Spanning-Tree Timers
Switch Priority Value
Spanning-Tree Interface States
Creating the Spanning-Tree Topology
Spanning-Tree Interface States
Blocking State
Forwarding State
Disabled State
Listening State
Learning State
Spanning Tree and Redundant Connectivity
Spanning-Tree Address Management
STP and Ieee 802.1Q Trunks
Supported Rstp Instances
Rstp Features
Accelerated Aging to Retain Connectivity
Port State Comparison
Port Roles and the Active Topology
Is Port Included
Rapid Convergence
Proposal and Agreement Handshaking for Rapid Convergence
Synchronization of Port Roles
Rstp Bpdu Flags
Bridge Protocol Data Unit Format and Processing
Bit Function
Processing Inferior Bpdu Information
Topology Changes
Processing Superior Bpdu Information
Interoperability with Ieee 802.1D STP
Configuring STP and Rstp Features
Disabling STP and Rstp
Default STP and Rstp Configuration
Feature Default Setting
Port-channel-number
Configuring the Root Switch
Configuring the Port Priority
Configuring the Switch Priority of a Bridge Group
Configuring the Path Cost
Configuring the Hello Time
Verifying and Monitoring STP and Rstp Status
Configuring the Forwarding-Delay Time for a Bridge Group
Configuring the Maximum-Aging Time for a Bridge Group
Displays brief summary of STP or Rstp information
Commands for Displaying Spanning-Tree Status
Example 6-1 show spanning-tree Commands
Displays detailed STP or Rstp information
Page
Understanding VLANs
Configuring VLANs on the ML-Series Card
Configuring Ieee 802.1Q Vlan Encapsulation
MLSeriesconfig-subif# end
Ieee 802.1Q Vlan Configuration
Returns to privileged Exec mode
Optional Saves your configuration changes to
Bridging Ieee 802.1Q VLANs
ML-Series#show vlans
Example 7-2 Output for show vlans Command
Monitoring and Verifying Vlan Operation
Page
Understanding Ieee 802.1Q Tunneling
Ieee 802.1Q Tunnel Ports in a Service-Provider Network
FCS
Configuring an Ieee 802.1Q Tunneling Port
Configuring Ieee 802.1Q Tunneling
Ieee 802.1Q Tunneling and Compatibility with Other Features
Ieee 802.1Q Example
Untagged will be switched based on this bridge-group. Other
Displays the tunnel ports on the switch
Optional Saves your entries in the configuration file
VLAN-Transparent Service Versus VLAN-Specific Services
VLAN-Transparent Services VLAN-Specific Services
Example 8-2 MLSeries B Configuration
Example 8-3applies to ML-Series card a
Example 8-3 ML-Series Card a Configuration
Example 8-5applies to ML-Series card C
Example 8-4 ML-Series Card B Configuration
Example 8-5 ML-Series Card C Configuration
Example 8-4applies to ML-Series card B
Understanding Layer 2 Protocol Tunneling
Configuring Layer 2 Protocol Tunneling
Default Layer 2 Protocol Tunneling Configuration
Default Layer 2 Protocol Tunneling Configuration
Layer 2 Protocol Tunneling Configuration Guidelines
2shows the default Layer 2 protocol tunneling configuration
Configuring Layer 2 Tunneling on a Port
Monitoring and Verifying Tunneling Status
Configuring Layer 2 Tunneling Per-VLAN
Understanding Link Aggregation
Configuring Link Aggregation on the ML-Series Card
Configuring Fast EtherChannel
Configuring Link Aggregation
Cisco IOS Configuration Fundamentals Configuration Guide
EtherChannel Configuration Example
Assigns an IP address and subnet mask to the POS
Configuring POS Channel
Configure one POS channel on the ML-Series card
Creates the POS channel interface. You can
POS Channel Configuration Example
Understanding Encapsulation over FEC or POS Channel
Configuring Encapsulation over EtherChannel or POS Channel
Encapsulation over EtherChannel Example
Configuration mode and enable other
Supported interface commands to meet
Example 9-5 MLSeries a Configuration
Monitoring and Verifying EtherChannel and POS
Example 9-6 MLSeries B Configuration
Port
Load Balancing on the ML-Series cards
For the Frame
XOR Result Port Channel
EtherChannel
Used Member
Interface for
Frame
Fourth
Second
First
Third
Used Member
This chapter includes the following major sections
Configuring IRB on the ML-Series Card
Cisco IOS Command Reference publication
Understanding Integrated Routing and Bridging
10-2
Configuring IRB
10-3
IRB Configuration Example
10-4
Example 10-1 Configuring MLSeries a
Example 10-2 Configuring MLSeries B
Monitoring and Verifying IRB
10-5
10-6
Field Description
11-1
Configuring Quality of Service on the ML-Series Card
11-2
IP Precedence and Differentiated Services Code Point
Understanding QoS
Priority Mechanism in IP and Ethernet
11-3
Ethernet CoS
11-4
ML-Series QoS
Classification
11-5
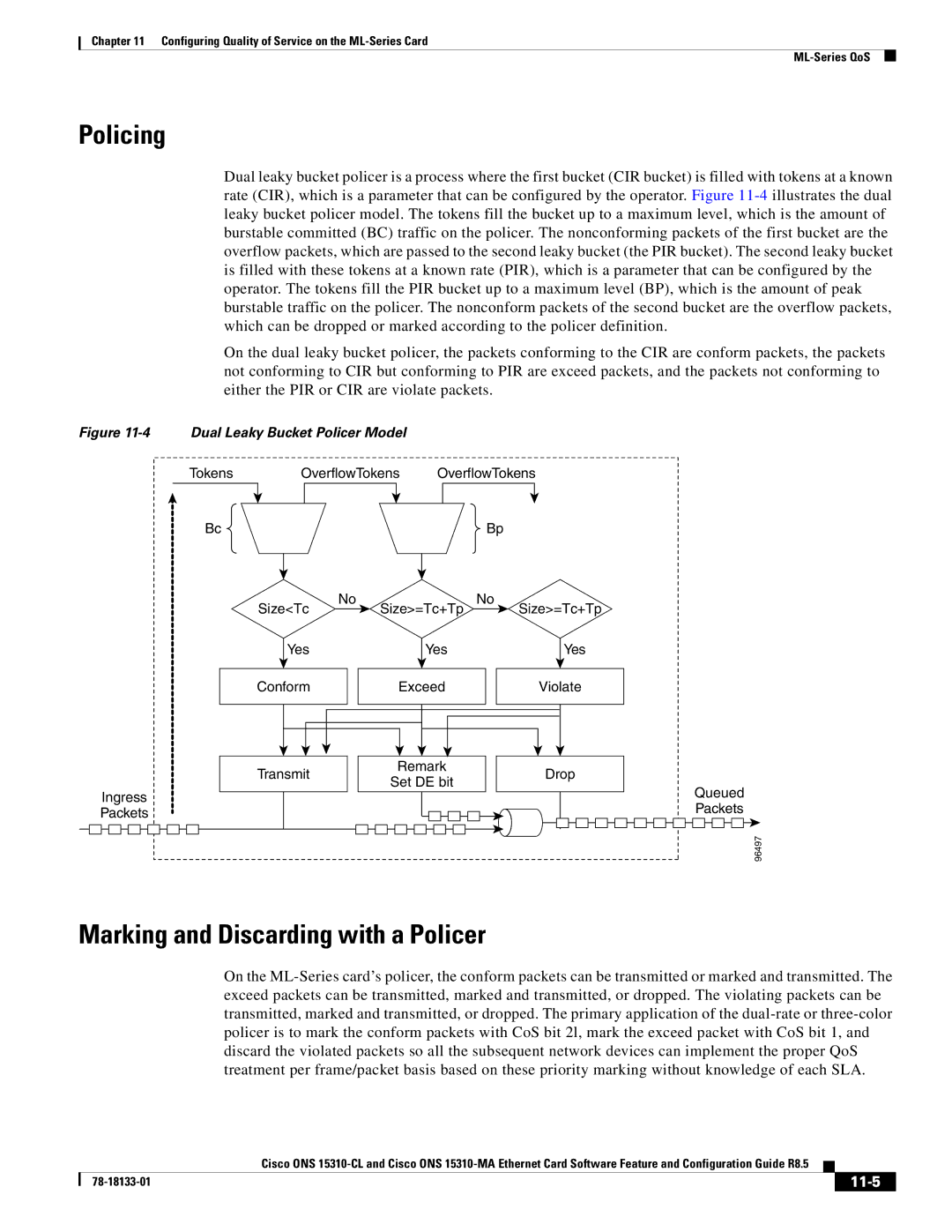
Policing
Marking and Discarding with a Policer
11-6
Queuing
Scheduling
11-7
Control Packets and L2 Tunneled Protocols
11-8
Egress Priority Marking
Ingress Priority Marking
QinQ Implementation
11-9
QoS on RPR
Flow Control Pause and QoS
11-10
Configuring QoS
Creating a Traffic Class
11-11
Creating a Traffic Policy
Maximum of 40 alphanumeric characters
Syntax of the class command is
Policy-map policy-nameno policy-map policy-name
Class class-map-name no class class-map-name
11-13
11-14
Command
11-15
Attaching a Traffic Policy to an Interface
Traffic class
Monitoring and Verifying QoS Configuration
Configuring CoS-Based QoS
Displays all configured traffic policies
11-17
QoS Configuration Examples
11-18
Traffic Classes Defined Example
Traffic Policy Created Example
Match spr1 Interface Example
Example 11-6 Class Map Match All Command Example
Example 11-7 Class Map Match Any Command Example
Example 11-8 Class Map SPR Interface Command Example
11-20
Example 11-9 ML-Series VoIP Commands
ML-Series VoIP Example
ML-Series Policing Example
ML-Series CoS-Based QoS Example
Example 11-10 ML-Series Policing Commands
Routerconfig# class-map match-all policer
Routerconfig# policy-map policef0
ML-Series CoS Example
11-22
11-23
Default Multicast QoS
11-24
Configuring Multicast Priority Queuing QoS
Multicast Priority Queuing QoS Restrictions
11-25
11-26
QoS not Configured on Egress
ML-Series Egress Bandwidth Example
Bandwidth
11-27
11-28
Understanding CoS-Based Packet Statistics
Fast Ethernet
Statistics Collected Interface Subinterface Vlan
11-29
Configuring CoS-Based Packet Statistics
MLSeries# show interface pos0 cos
Understanding IP SLA
11-30
MLSeries# show interface fastethernet 0 cos
11-31
IP SLA on the ML-Series
IP SLA Restrictions on the ML-Series
11-32
12-1
Understanding the SDM
Understanding SDM Regions
Lookup Type
Configuring SDM
Configuring SDM Regions
Default Size
Entries
Configuring Access Control List Size in Tcam
Task Command
Monitoring and Verifying SDM
12-4
13-1
Configuring Access Control Lists on ML-Series Card
Understanding ACLs
ML-Series ACL Support
13-2
IP ACLs
Named IP ACLs
User Guidelines
13-3
Creating IP ACLs
Creating Numbered Standard and Extended IP ACLs
13-4
Creating Named Standard IP ACLs
Creating Named Extended IP ACLs Control Plane Only
Applying the ACL to an Interface
Applying ACL to Interface
Controls access to an interface
Modifying ACL Tcam Size
13-5
13-6
14-1
Configuring Resilient Packet Ring on ML-Series Card
Understanding RPR
14-2
Role of Sonet Circuits
Packet Handling Operations
14-3
Ring Wrapping
14-4
RPR Framing Process
RPR Frame for ML-Series Card
DA-MAC and 0x00 for Unknown DA-MAC
RPR as the source
14-5
CTM and RPR
Configuring RPR
MAC Address and Vlan Support
RPR QoS
14-7
Configuring CTC Circuits for RPR
CTC Circuit Configuration Example for RPR
Three-Node RPR Example
14-8
14-9
14-10
Configures a station ID. The user must configure a
Optional Sets the RPR ring wrap mode to either wrap
Immediate delayed
14-11
Assigning the ML-Series Card POS Ports to the SPR Interface
14-12
14-13
14-14
RPR Cisco IOS Configuration Example
Example 14-1 SPR Station-ID 1 Configuration
Example 14-2 SPR Station-ID 2 Configuration
14-15
CRC Threshold Configuration and Detection
Example 14-3 SPR Station-ID 3 Configuration
Example 14-5 Example of show run interface spr 1 Output
Monitoring and Verifying RPR
14-16
Example 14-4 Example of show interface spr 1 Output
14-17
Add an ML-Series Card into an RPR
Three-Node RPR After the Addition
14-18
14-19
Adding an ML-Series Card into an RPR
14-20
Cisco ONS 15454 Procedure Guide
Enables the port
Endpoint of the first newly created circuit
14-21
Stop. You have completed this procedure
Delete an ML-Series Card from an RPR
Endpoint of the second newly created circuit
Three-Node RPR Before the Deletion
14-22
14-23
Deleting an ML-Series Card from an RPR
Log into Adjacent Node 1 with CTC
Double-click the ML-Series card in Adjacent Node
14-24
Cisco Proprietary RPR Shortest Path
Configuring Cisco Proprietary RPR KeepAlive
Configuring Shortest Path and Topology Discovery
Cisco Proprietary RPR KeepAlive
14-26
Redundant Interconnect
Monitoring and Verifying Shortest Path andTopolgy Discovery
Redundant Interconnect is only supported on 454 platforms
15-1
Configuring Security for the ML-Series Card
Understanding Security
Understanding SSH
Secure Login on the ML-Series Card
Disabling the Console Port on the ML-Series Card
Secure Shell on the ML-Series Card
This section has configuration information
Configuring SSH
Configuration Guidelines
Setting Up the ML-Series Card to Run SSH
15-4
Configuring the SSH Server
Router config# ip ssh timeout
Displaying the SSH Configuration and Status
Router # configure terminal
Router config# ip ssh version 1
15-6
Radius Relay Mode
Radius on the ML-Series Card
15-7
Radius Stand Alone Mode
Configuring Radius Relay Mode
15-8
Configuring Radius
Understanding Radius
15-9
Default Radius Configuration
Identifying the Radius Server Host
15-10
Switchconfig# radius-server host host1
Configuring AAA Login Authentication
Router# configure terminal Enter global configuration mode
Router config# aaa new-model Enable AAA
15-12
Router config# aaa authentication
Router config# line console tty
15-13
Router config# end Return to privileged Exec mode
Router# show running-config Verify your entries
Defining AAA Server Groups
Router # show running-config
Router config# aaa group server
Router config-sg-radius# server
Router config-sg-radius# end
15-15
Radius
15-16
Starting Radius Accounting
15-17
Configuring a nas-ip-address in the Radius Packet
Configuring Settings for All Radius Servers
15-18
Default is 0 the range is 1 to 1440 minutes
Deadtime minutes
Marked as dead, the skipping will not take place
15-19
Send accounting authentication
15-20
Displaying the Radius Configuration
16-1
Configuring Bridging on the ML-Series Card
Understanding Bridging
16-2
Configuring Bridging
16-3
For any statically configured forwarding entries
Monitoring and Verifying Bridging
Brief displays summary information about spanning tree
Displays detailed information about spanning tree
Bridge-group-number restricts the spanning tree information
To specific bridge groups
17-1
CE-100T-8 Ethernet Operation
CE-100T-8 Overview
Sonet
17-2
CE-100T-8 Ethernet Features
Autonegotiation, Flow Control, and Frame Buffering
17-3
Ethernet Link Integrity Support
17-4
Enhanced State Model for Ethernet and Sonet Ports
Ieee 802.1Q CoS and IP ToS Queuing
CoS Priority Queue Mappings
17-5
IP ToS Priority Queue Mappings
17-6
CE-100T-8 Sonet Circuits and Features
Rmon and Snmp Support
Statistics and Counters
17-7
Ccat High Order Vcat High Order Vcat Low Order
Number of STS-3c Circuits Maximum Number of STS-1 Circuits
Maximum Number of STS-1-2v Circuits
17-8
CE-100T-8 Maximum Service Densities
CE-100T-8 STS/VT Allocation Tab
7x=1-12 6x=1-14 5x=1-16 =1-21
17-9
CE-100T-8 Vcat Characteristics
17-10
CE-100T-8 POS Encapsulation, Framing, and CRC
17-11
CE-100T-8 Loopback, J1 Path Trace, and Sonet Alarms
17-12
Command Reference for the ML-Series Card
Rstp
Related Commands bridge-group
Drpri-rstp
Ieee
Router# clear counters
Related Commands show interface
Clear counters
Clock timezone
Syntax Description Defaults Command Modes Usage Guidelines
No clock auto
Clock summertime
Interface spr
Defaults Command Modes
MLSeriesconfig-if # pos mode gfp fcs-disable
No pos mode gfp fcs-disabled
Related Commands shutdown
No pos pdi holdoff time
Pos trigger defects
No pos report alarm
Related Commands
Non pos trigger defects condition
Syntax Description Defaults
Related Commands pos trigger delay
Command is 50 milliseconds
No pos trigger delay time
Time Delay time in milliseconds, 200 to
Default value is 200 milliseconds
Immediate
No pos vcat defect immediate delayed
Delayed
Parameter Description
MLSeries# show controller pos 0 Interface POS0
Show controller pos interface-numberdetails
Related Commands show interface pos Clear counters
Show interface pos interface-number
Use this command to display the status of the POS interface
Related Commands show controller pos Clear counters
MLSeries# show ons alarm
Show ons alarm
78-18133-01
Vcg
Eqpt
Sts
MLSeries# show ons alarm defect sts
Related Commands show controller pos Show ons alarm failures
ML-Series#show ons alarm failure port
MLSeries# show ons alarm failure eqpt
MLSeries# show ons alarm failure sts
Interface spr Spr station-id Spr wrap
Assigns the POS interface to the SPR interface
Port-based
Related Commands interface spr
No spr load-balance auto port-based
Auto
Spr-intf-id Spr wrap
Configures a station ID
DefaultsN/A
Following example sets an ML-Series card SPR station ID to
Interface spr Spr-intf-id Spr station-id
Spr wrap immediate delayed
Wraps RPR traffic after the carrier delay time expires
Unsupported Global Configuration Commands
Unsupported CLI Commands for the ML-Series Card
Unsupported Privileged Exec Commands
Page
Unsupported POS Interface Configuration Commands
Unsupported FastEthernet Interface Configuration Commands
Unsupported Port-Channel Interface Configuration Commands
Rate-limit Random-detect Timeout Tx-ring-limit
Unsupported BVI Interface Configuration Commands
Gathering Information About Your Internetwork
Using Technical Support
Getting the Data from Your ML-Series Card
Providing Data to Your Technical Support Representative
Page
IN-5
IN-6
IS,AINS
IN-7
CRC
RPR
Rstp SDM
SSH
IN-9
Rstp STP
IN-10
See also framing
GFP-F
IN-11
Lcas
IN-12
POS
RPR SDM
IN-13
IN-14
Rmon
Rstp
IN-15
Snmp
See also Bpdu
IN-16
Tcam
Vcat
VTP Layer 2 protocol tunneling Vty
Configuring as Layer 2 tunnel Configuring Ieee 802.1Q
Customer numbering in service-provider
SDM STP and Rstp status
IN-18