HP-UX Directory Server Version
Page
Table of Contents
Table of Contents
Table of Contents
3.3
3.4
Nsssl3ciphers
Nsslapd-state Nsslapd-backend
113
Password Storage Schemes
Schema reload plug-in
Nsslapd-pluginEnabled
Nsslapd-idl-switch
Cn=userRoot, cn=ldbm database, cn=plugins, cn=config
Cn=ldbm database, cn=plugins, cn=config
NsMaxResponseDelay
NsMaxTestResponseDelay
169
173
189
239
Finding and executing command-line scripts 215
215
257
243
247
Page
Directory Server configuration
Using Directory Server command-line utilities
Directory Server configuration
Directory Server instance file reference
Using Directory Server command-line scripts
Introduction
Overview of the Directory Server configuration
Ldif and schema configuration files
Directory Server Ldif configuration files
How the server configuration is organized
Configuration attributes
Configuration of plug-in functionality
Directory Server Ldif configuration files
Accessing and modifying server configuration
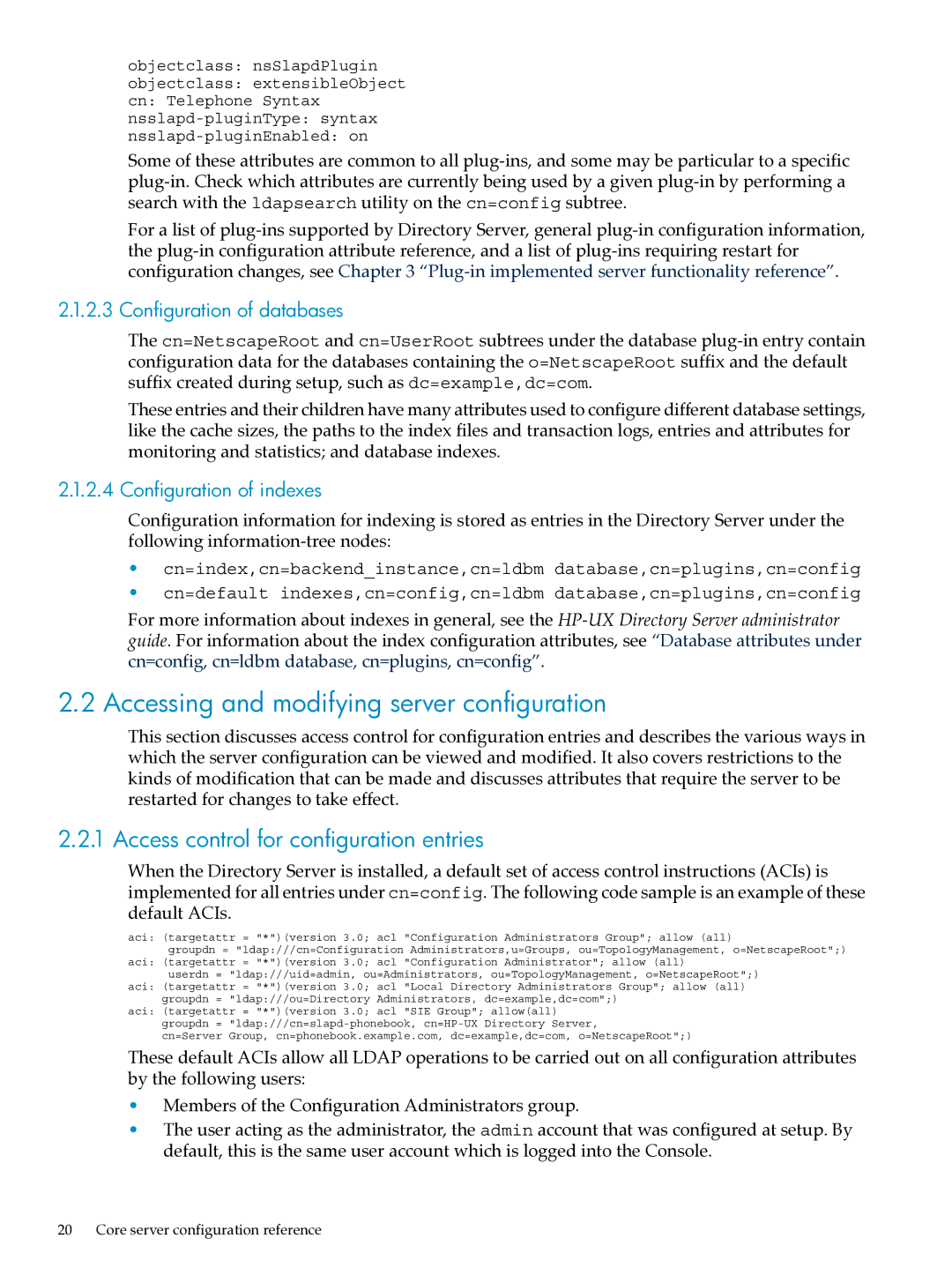
Access control for configuration entries
Configuration of databases
Configuration of indexes
Where
Changing configuration attributes
Modifying configuration entries using Ldap
Core server configuration attributes reference
Configuration changes requiring server restart
1 cn=config
Nsslapd-accesslog Access log
Nsslapd-accesslog-level Access log level
Nsslapd-accesslog-list List of access log files
Nsslapd-accesslog-logbuffering Log buffering
Attribute values for enabling or disabling access logging
Nsslapd-accesslog-logging-enabled Access log enable logging
Default Value Syntax Directory String Example
Valid Values
Valid Range
SyntaxDirectoryString Example
EntryDN Cn=config Valid Range
Disk space allowed to the access log is unlimited in size
Syntax DirectoryString Example
Nsslapd-accesslog-logrotationtime Access log rotation time
Nsslapd-accesslog-maxlogsize Access log maximum log size
Nsslapd-accesslog-mode Access log file permission
SyntaxInteger Example
ValidRange Through Default Value 600 Syntax Integer Example
Default Value Off Syntax DirectoryString Example
Nsslapd-attribute-name-exceptions
Nsslapd-auditlog Audit log
Nsslapd-auditlog-list
Attribute values for enabling or disabling audit logging
Provides a list of audit log files
EntryDN
Nsslapd-auditlog-logging-enabled Audit log enable logging
Entry DN Cn=config Valid Values
Turns audit logging on and off
Disk space allowed to the audit log is unlimited in size
Valid Range Through Default Value
Syntax Integer Example Nsslapd-auditlog-logrotationsynchour
Time between audit log file rotation is unlimited
Nsslapd-auditlog-logrotationtime Audit log rotation time
Syntax Integer Example Nsslapd-auditlog-logrotationsyncmin
None Read only Execute only
Nsslapd-auditlog-maxlogsize Audit log maximum log size
Nsslapd-auditlog-mode Audit log file permission
Write access to the server user ID
Nsslapd-certdir Certificate and key database directory
Nsslapd-certmap-basedn Certificate map search base
Write only Read and write Write and execute
Nsslapd-config
This read-only attribute is the config DN
Nsslapd-conntablesize
Nsslapd-counters
Nsslapd-ds4-compatible-schema
Default Value Syntax DirectoryString Example
Default Value Off Core server configuration reference
Nsslapd-csnlogging
Attribute values for enabling or disabling error logging
Nsslapd-errorlog Error log
Nsslapd-errorlog-level Error log level
Nsslapd-errorlog-list
This read-only attribute provides a list of error log files
Nsslapd-errorlog-logging-enabled Enable error logging
Turns error logging on and off
Disk space allowed to the error log is unlimited in size
Nsslapd-errorlog-logrotationtime Error log rotation time
Time between error log file rotation is unlimited
Nsslapd-errorlog-maxlogsize Maximum error log size
Nsslapd-groupevalnestlevel
Nsslapd-errorlog-mode Error log file permission
Nsslapd-idletimeout Default idle timeout
Nsslapd-ioblocktimeout IO block time out
Default Value Syntax Integer Example Nsslapd-idletimeout
Nsslapd-instancedir Instance directory
Nsslapd-lastmod Track modification time
Nsslapd-listenhost Listen to IP address
Nsslapd-ldapilisten Enable Ldapi socket
Nsslapd-ldapifilepath Ldapi socket file path
Default Value SyntaxDirectoryString Example
Nsslapd-localhost Local host
Nsslapd-localuser Local user
Nsslapd-lockdir Server lock file directory
Nsslapd-maxbersize Maximum message size
Nsslapd-maxdescriptors Maximum file descriptors
Nsslapd-maxsasliosize Maximum Sasl packet size
This attribute value is specified in bytes
Nsslapd-maxthreadsperconn Maximum threads per connection
Nsslapd-nagle
Nsslapd-outbound-ldap-io-timeout
Default Value Core server configuration reference
Nsslapd-plugin
Nsslapd-port Port number
But the request is for this entry
Nsslapd-readonly Read only
Nsslapd-referral Referral
Nsslapd-referralmode Referral mode
Nsslapd-reservedescriptors Reserved file descriptors
Nsslapd-return-exact-case Return exact case
Nsslapd-rewrite-rfc1274
Nsslapd-rootdn Manager DN
Nsslapd-rootpw Root password
Default Value Syntax
Nsslapd-rootpwstoragescheme Root password storage scheme
Nsslapd-saslpath
Nsslapd-schemacheck Schema checking
Nsslapd-schemadir
Nsslapd-securePort Encrypted port number
Nsslapd-schemareplace
Nsslapd-securelistenhost
Nsslapd-security Security
Nsslapd-sizelimit Size limit
Nsslapd-timelimit Time limit
Default Value Syntax Integer Example Nsslapd-threadnumber
Nsslapd-threadnumber Thread number
PasswordChange Password change
Indicates whether users may change their passwords
Nsslapd-tmpdir
Nsslapd-versionstring
PasswordCheckSyntax Check password syntax
PasswordExp Password expiration
PasswordGraceLimit Password expiration
PasswordHistory Password history
PasswordInHistory Number of passwords to remember
Default Value Syntax Integer Example PasswordGraceLimit
PasswordLockoutDuration Lockout duration
PasswordIsGlobalPolicy Password policy and replication
PasswordLockout Account lockout
PasswordMaxAge Password maximum age
PasswordMaxFailure Maximum password failures
PasswordMaxRepeats Password syntax
Default Value Syntax Integer Example PasswordMaxFailure
Default Value Syntax Integer Example PasswordMinAge
PasswordMin8Bit Password syntax
PasswordMinAge Password minimum age
PasswordMinAlphas Password syntax
PasswordMinCategories Password syntax
PasswordMinDigits Password syntax
PasswordMinLength Password minimum length
PasswordMinTokenLength Password syntax
PasswordMinLowers Password syntax
PasswordMinSpecials Password syntax
PasswordStorageScheme Password storage scheme
PasswordMinUppers Password syntax
PasswordMustChange Password must change
PasswordUnlock Unlock account
PasswordWarning Send warning
2 cn=changelog5,cn=config
Nsslapd-changelogdir
3 cn=encryption,cn=config
Nssslsessiontimeout
Nsslapd-changelogmaxage Max changelog age
Nsslapd-changelogmaxentries Max changelog records
Means disallow certificate-based authentication
Default Value Off Syntax DirectoryString Example Nsssl2 off
Nssslclientauth
NsSSL2
4 cn=features,cn=config
5 cn=mapping tree,cn=config
Suffix configuration attributes under cn=suffixName
Nsssl3ciphers
Nsslapd-state
Nsslapd-backend
Determines how the suffix handles operations
To requests made by client applications
NsDS5ReplicaChangeCount
NsDS5Flags
NsDS5ReplicaBindDN
NsDS5ReplicaPurgeDelay
NsDS5ReplicaId
NsDS5ReplicaLegacyConsumer
NsDS5ReplicaName
NsDS5ReplicaTombstonePurgeInterval
NsDS5ReplicaReferral
NsDS5ReplicaRoot
NsState
NsDS5ReplicaType
NsDS5ReplicaReapActive
Description
NsDS5ReplConflict
8.1 cn
NsDS5ReplicaBindMethod
NsDS5ReplicaBusyWaitTime
Schema
NsDS5ReplicaChangesSentSinceStartup
NsDS5ReplicaCredentials
NsDS5ReplicaHost
NsDS5ReplicaLastInitEnd
NsDS5ReplicaLastInitStart
NsDS5ReplicaLastInitStatus
Time
NsDS5ReplicaLastUpdateEnd
NsDS5ReplicaLastUpdateStart
NsDS5ReplicaLastUpdateStatus
NsDS5ReplicaPort
Default Value SyntaxInteger ExamplensDS5ReplicaPort389
NsDS5ReplicaPriority
NsDS5BeginReplicaRefresh
NsDS5ReplicaSessionPauseTime
NsDS5ReplicatedAttributeList
NsDS5ReplicaTimeout
Valid Range Default Value SyntaxDirectoryString Example
NsDS5ReplicaTransportInfo
NsDS5ReplicaUpdateInProgress
NsDS5ReplicaUpdateSchedule
Sunday
NsDS5ReplicaLastUpdateEnd
NsDS50ruv
Nsds7NewWinGroupSyncEnabled
Nsds7NewWinUserSyncEnabled
Nsds7DirectoryReplicaSubtree
Nsds7DirsyncCookie
10 cn=monitor
Nsds7WindowsDomain
Nsds7WindowsReplicaSubtree
WinSyncInterval
For example
Connection table
Greenwich Mean Time
This is the number of completed operations
12 cn=SNMP,cn=config
Nssnmpenabled
This attribute sets whether Snmp is enabled
11 cn=replication
Nssnmporganization
Nssnmplocation
Nssnmpcontact
Nssnmpdescription
Snmp statistic attributes
Nssnmpmasterhost
Nssnmpmasterport
Snmp statistic attributes
14 cn=tasks,cn=config
Snmp statistic attributes
Task invocation attributes for entries under cn=tasks
Entry DN
14.2 cn=import,cn=tasks,cn=config
Default Value Syntax DirectoryString Example Ttl
NsFilename file1.ldif NsFilename file2.ldif
Default Value Syntax Integer Example NsImportChunkSize
14.3 cn=export,cn=tasks,cn=config
Valid Values Any DN Core server configuration reference
Default Value Syntax DN, multi-valued Example
Syntax Case-insensitive string Example NsUseOneFile true
Syntax Case-insensitive string Example NsExportReplica true
Syntax Case-insensitive string Example NsPrintKey false
14.4 cn=backup,cn=tasks,cn=config
Syntax Case-insensitive string Example NsUseId2Entry true
Syntax Case-insensitive string Example NsNoWrap false
Syntax Case-insensitive string Example NsDumpUniqId true
14.5 cn=restore,cn=tasks,cn=config
14.6 cn=index,cn=tasks,cn=config
Syntax Case-exact string Example
14.7 cn=schema reload task,cn=tasks,cn=config
NsIndexAttribute attributeindex1,index2
14.8 cn=memberof task,cn=tasks,cn=config
15 cn=uniqueid generator,cn=config
112
Server plug-in functionality reference
Server plug-in functionality reference
1 7-bit check plug-in
Attribute uniqueness plug-in
ACL plug-in
ACL preoperation plug-in
Binary syntax plug-in
Boolean syntax plug-in
Plug-in Name Chaining Database DN of Configuration Entry
Description Syntax for handling DNs Configurable Options
Case exact string syntax plug-in
Case ignore string syntax plug-in
Class of service plug-in
Country string syntax plug-in
Distinguished name syntax plug-in
Dependencies None Performance Related
Distributed numeric assignment plug-in
Generalized time syntax plug-in
Details of distributed numeric assignment plug-in
Plug-in Name
Http client plug-in
Internationalization plug-in
Jpeg syntax plug-in
Ldbm database plug-in
Legacy replication plug-in
Information Further Information
Details of MemberOf plug-in
MemberOf plug-in
Multi-master replication plug-in
OID syntax plug-in
Password Storage Schemes
Octet string syntax plug-in
Password storage plugins
Postal address string syntax plug-in
PTA plug-in
Referential integrity postoperation plug-in
Retro Changelog plug-in
Roles plug-in
Both presence and equality
Applications
Space insensitive string syntax plug-in
Schema reload plug-in
Details of schema reload plug-in
Telephone syntax plug-in
URI syntax plug-in
Views plug-in
Resource Locators
List of attributes common to all plug-ins
Account policy plug-in
Nsslapd-pluginPath
This attribute specifies the full path to the plug-in
Nsslapd-pluginEnabled
Nsslapd-pluginInitfunc
Nsslapd-pluginType
Nsslapd-pluginId
Attributes allowed by certain plug-ins
Nsslapd-pluginVersion
Nsslapd-pluginVendor
Nsslapd-pluginDescription
Nsslapd-plugin-depends-on-named
Nsslapd-pluginLoadGlobal
Nsslapd-plugin-depends-on-type
Database plug-in attributes
NsLookthroughLimit
Nsslapd-cache-autosize
Nsslapd-cache-autosize-split
Platforms
Nsslapd-dbcachesize
Nsslapd-db-checkpoint-interval
Default Value Database plug-in attributes
Nsslapd-db-circular-logging
Nsslapd-db-debug
Nsslapd-db-durable-transactions
Nsslapd-db-home-directory
Nsslapd-db-idl-divisor
Nsslapd-db-logdirectory
Automatically adjusted to the minimum value
Nsslapd-db-logbuf-size
Valid Range Bytes to 64 kilobytes Default Value
Nsslapd-db-logfile-size
Nsslapd-db-page-size
Nsslapd-db-private-import-mem
Nsslapd-db-spin-count
Nsslapd-db-transaction-batch-val
Nsslapd-dbncache
Nsslapd-db-trickle-percentage
Nsslapd-db-verbose
Nsslapd-exclude-from-export
Nsslapd-idl-switch
Nsslapd-directory
Nsslapd-import-cache-autosize
Nsslapd-idlistscanlimit
Nsslapd-import-cachesize
No access for other users
Default Value 600 Database plug-in attributes
Nsslapd-mode
Memory to importCache
Nsslapd-serial-lock
Nsslapd-search-bypass-filter-test
Nsslapd-search-use-vlv-index
Nsslapd-cachesize
Nsslapd-cachememsize
Nsslapd-suffix
Nsslapd-readonly
Nsslapd-require-index
Database plug-in attributes
This attribute provides the name of the attribute to index
5.1 cn
NsSystemIndex
NsIndexType
NsMatchingRule
NsSubStrBegin
Indexed attribute representing a subentry
NsSubStrEnd
NsSubStrMiddle
Encrypted attributes under the cn=config node
Database link plug-in attributes chaining attributes
NsEncryptionAlgorithm
NsActiveChainingComponents
Database link plug-in attributes chaining attributes
Nspossiblechainingcomponents
NsMaxResponseDelay
NsMaxTestResponseDelay
NsBindConnectionsLimit
NsTransmittedControls
NsAbandonedSearchCheckInterval
NsBindTimeout
Default Value Syntax Integer Example
NsBindRetryLimit
NsCheckLocalACI
NsConcurrentBindLimit
NsConcurrentOperationsLimit
NsConnectionLife
NsOperationConnectionsLimit
NsSizeLimit
NsProxiedAuthorization
NsReferralOnScopedSearch
NsTimeLimit
NsBindMechanism
Valid Values Empty
NsFarmServerURL
NsMultiplexorBindDN
Encryption schema
NsMultiplexorCredentials
Nshoplimit
NsUseStartTLS
Retro changelog plug-in attributes
Nsslapd-changelogdir
Distributed numeric assignment plug-in attributes
Nsslapd-changelogmaxage Max changelog age
DnaFilter
DnaMagicRegen
DnaNextValue
DnaMaxValue
DnaNextRange
DnaRangeRequestTimeout
Default Value Syntax Integer Example DnaNextValue
DnaPrefix
Bit systems
DnaThreshold
DnaScope
DnaSharedCfgDN
MemberOf plug-in attributes
DnaType
Memberofattr
Memberofgroupattr
Account policy plug-in attributes
Backup files
Configuration files
Overview of Directory Server files
Database files
Setup-ds-admin.plscript is run
At setup for example, dc=example,dc=com
Used internally by the database and should not be moved
Deleted, or modified in any way
Ldif files
Lock files
Log files
PID files
Tools
Scripts
Access log reference
Access logging levels
Default access logging content
Example 5-1 Example access log
Connection number
File descriptor
Error number
Slot number
Operation number
Method type
Ldap request type
Number of entries
Elapsed time
Unindexed search indicator
Ldap response type
VLV-related entries
Search scope
Extended operation OID
Change sequence number
Abandon message
LDAPv3 extended operations supported by Directory Server
Sasl multi-stage bind logging
Access log content for additional access logging levels
Message ID
Options description
Common connection codes
Connection description
Error log reference
Error log logging levels
Error log levels
Common connection codes
Error log content
Error log levels
Error log content for other log levels
Example 5-3 Error log excerpt
Example 5-4 Replication error log entry
Into pending list
Timestamp Pluginname message Timestamp function message
Audit log reference
Example 5-6 Config file processing log entry
Example 5-7 Access control summary logging
Example 5-8 Audit log content
Ldap result codes
Audit log does not have any other log level to set
Ldap result codes
Adminlimitexceeded Ldap
Ldap result codes
Referral Ldap
Ldap
Finding and executing command-line utilities
Using special characters
Command-line utilities quick reference
Commonly-used command-line utilities
Ldapsearch
Ldapsearch syntax
Commonly-used ldapsearch options
Ldapsearch syntax
Commonly-used ldapsearch options
Persistent search options
Ldapsearch SSL options
Commonly-used ldapsearch options
Persistent search options
Ldapsearch Sasl options
Additional SSL ldapsearch options
Sasl options
Description of CRAM-MD5 mechanism options
Do not permit mechanisms that allow anonymous access
Description of CRAM-MD5 mechanism options
Do not permit mechanisms susceptible to active attacks
Require forward secrecy
Maxbufsize
Following UID. For example
Description of DIGEST-MD5 Sasl mechanism options
Required Mech=DIGEST-MD5 Gives the Sasl Mechanism
10 Additional ldapsearch options
Additional ldapsearch options
Description of Gssapi Sasl mechanism options
10 Additional ldapsearch options
Ldapmodify
Ldapmodify syntax
Commonly-used ldapmodify options
11 Commonly-used ldapmodify options
12 ldapmodify SSL options
Ldapmodify SSL options
11 Commonly-used ldapmodify options
13 Sasl options
Ldapmodify Sasl options
12 ldapmodify SSL options
14 Additional ldapmodify options
Ldapdelete
Additional ldapmodify options
Ldapdelete syntax
Commonly-used ldapdelete options
Ldapdelete SSL options
15 Commonly-used ldapdelete options
17 Sasl options
Ldapdelete Sasl options
16 ldapdelete SSL options
Ldappasswd
Additional ldapdelete options
Ldappasswd syntax
18 Additional ldapdelete options
Ldappasswd-specific options
General ldappasswd options
19 ldappasswd-specific options
20 General ldappasswd options
Ldappasswd Sasl options
20 General ldappasswd options
Six values
Ldappasswd examples
21 Sasl options
Example 6-2 Directory Manager generating a users password
Example 6-3 User changing his own password
Ldif
Ldif
Ldif command has the following format
Dbscan
Ldif syntax
Ldif options
Dbscan options
Dbscan examples
23 Common options
24 Entry file options
Example 6-8 Displaying VLV index file contents
Example 6-13 Displaying the changelog file contents
Example 6-14 Dumping the index file uid.db4 with raw mode
Example 6-7 Dumping the entry file
Finding and executing command-line scripts
Command-line scripts quick reference
Saveconfig
Shell scripts in /opt/dirsrv/slapd-instancename
Shell scripts
Perl scripts in /opt/dirsrv/slapd-instancename
Scripts in /opt/dirsrv/bin
This section covers the following scripts
1 bak2db Restores a database from backup
Cl-dump Dumps and decodes the changelog
Syntax
Bak2db options
Dbverify Checks for corrupt databases
Cl-dump options
Options
Dbverify options
4 db2bak Creates a backup of a database
5 db2ldif Exports database contents to Ldif
6 db2index Reindexes database index files
Ldif2db Import
Reindex cn and givenname in the database instance userRoot
Db2index options
Pwdhash Prints encrypted passwords
Ldif2ldap Performs import operation over Ldap
Ldif2db options
10 ldif2ldap options
Monitor Retrieves monitoring information
Repl-monitor Monitors replication status
11 pwdhash options
Syntax monitor
Hostportbinddnbindpwdbindcert
Restart-slapd Restarts the Directory Server
Restoreconfig Restores Administration Server configuration
Saveconfig Saves Administration Server configuration
Start-slapd Starts the Directory Server
Stop-slapd Stops the Directory Server
Suffix2instance Maps a suffix to a backend name
Vlvindex Creates virtual list view indexes
1 bak2db.pl Restores a database from backup
Restores a database from a backup
Perl scripts
Options Either the -nor the -soption must be specified
3 db2bak.pl Creates a backup of a database
19 cl-dump.pl command options
Creates a backup of the database
Cl-dump.pl Dumps and decodes the changelog
5 db2ldif.pl Exports database contents to Ldif
4 db2index.pl Creates and generates indexes
Fixup-memberof.pl Regenerate memberOf attributes
22 db2ldif.pl options
24 ldif2db.pl options
Ldif2db.pl Import
23 fixup-memberof.pl options
24 ldif2db.pl options
25 Information extracted from access logs
Logconv.pl Log converter
26 logconv.pl options
28 ns-accountstatus.pl options
Ns-accountstatus.pl Establishes account status
27 logconv.pl options to display occurrences
Ns-activate.pl Activates an entry or group of entries
Ns-inactivate.pl Inactivates an entry or group of entries
Activates an entry or group of entries
29 ns-activate.pl options
Repl-monitor.pl Monitors replication status
31 ns-newpwdpolicy.pl options
Shows in-progress status of replication
32 repl-monitor.pl options
Where
Schema-reload.pl Reload schema files dynamically
33 schema-reload.pl options
Schemadirectory script uses the default schema directory
Verify-db.pl Check for corrupt databases
Usage information
Command, then it uses the default database directory
34 verify-db.pl option
How to contact HP technical support
Contacting HP
Information to collect before contacting HP
HP authorized resellers
Support and other resources
Related information
HP-UX Directory Server documentation set
Troubleshooting resources
Typographic conventions
HP-UX documentation set
This document uses the following typographical conventions
TIP
Finding and executing the ns-slapd command-line utilities
Exports the contents of the database to Ldif
Overview of ns-slapd
Utilities for exporting databases db2ldif
Utilities for restoring and backing up databases ldif2db
Table A-1 db2ldif options
Imports Ldif files to the database
Table A-2 ldif2db options
Utilities for creating and regenerating indexes db2index
Utilities for restoring and backing up databases archive2db
Utilities for restoring and backing up databases db2archive
Table A-5 db2index options
Glossary
247
Bind rule
Glossary
CoS definition
249
GSS-API
Ldap
251
NIS
Proxy
253
Sasl
Superuser
255
256
257
Symbols
Statistics for monitoring and optimizing directory
Suffix and replication configuration entries
Read-only monitoring configuration entries
259
Index
Database link plug-in configuration attributes
261
Distributed numeric assignment plug-in configuration
Ldap
263
NsDS5ReplicaChangesSentSinceStartup attribute
265
Page
267
Index
269
Index
271