Manufacturing Part Number T1417-90009 E0905
Edition
Copyright Notices
Legal Notices
Page
Page
Contents
Configuring the Kerberos Server with Ldap
Administering the Kerberos Server
Contents
Contents
Propagating the Kerberos Server
Managing Multiple Realms
Contents
Tables
Table A-2. Configuration Worksheet Explanation
Figures
Figures
Intended Audience
What Is in This Document
Glossary
Interoperability with Windows 2000, on
Width
Typographic Conventions
Index
Bold fixed
Publishing History
HP-UX Release Name and Release Identifier
Related Software Products
Related Documentation
Accessing the World Wide Web
Related Request for Comments RFCs
HP Encourages Your Comments
Overview
Overview
Introduction
How the Kerberos Server Works
Authentication Process
Illustrates the actions of the components and the Kerberos
Authentication Process
Step
Authentication Process
DES Versus 3DES Key Type Settings
Ldap Advantages
Introduction to Ldap
Integrating Kerberos Server v3.1 with Ldap
Integrating a Kerberos Principal in to the Ldap Directory
Installing the Kerberos Server
Installing the Kerberos Server
Prerequisites
Version Compatibility
System Requirements
Hardware Requirements
Software Requirements
Installing the Server
Installing the Server Chapter
Migrating to a Newer Version
Migrating to a Newer Version of the Kerberos Server
Migrating from Kerberos Server Version 1.0 to
Copy the dump file to the new system where you are installing
Upon success, the following message appears
Migrating from Kerberos Server Version 1.0 to
Version
Migrating from Kerberos Server Version 2.0 to
Copy the dump file to the system on which you are installing
Migrating from Kerberos Server Version 3.0 to Version
Migrating to a Newer Version of the Kerberos Server
Interoperability with Windows
Interoperability with Windows
Understanding the Terminology
Table of Analogous Terms Kerberos Server Windows
Scenario
Kerberos Server and Windows 2000 Interoperability
Establishing Trust Between Kerberos Server and Windows
Fqdn qualifier specifies the fully qualified domain name
Single Realm Domain Authentication
Interrealm Interdomain Authentication
Postdated Tickets
Special Considerations for Interoperability
Database Considerations
Encryption Considerations
Special Considerations for Interoperability Chapter
Special Considerations for Interoperability Chapter
Configuring the Kerberos
Security Server Files That Require Configuration
Configuration Files for the Kerberos Server
Configuration File Function
Krb.conf File Format
Krb.conf File
Krb.realms File
Krb.realms File Format
Wildcard Character Description
Wildcard Characters
Autoconfiguring the Kerberos Server
To configure the server, select option
Configuring the Kerberos Server with C-Tree
Value, DES-MD5, is selected
Server with Ldap
File Function
Configuration Files for Ldap Integration
Krb5ldap.conf File
Ldap Configuration Files
Parameter Description
Krb5ldap.conf File Format
This line indicates a space
Krb5schema.conf File
Krb5schema.conf File Format
Ticket’ Syntax
Configuration Files for Ldap Integration
Krb5map.conf File Format
Krb5map.conf File
HpKrbAuthzData HpKrbKeyVersion HpKrbKeyData
Before You Begin
Planning Your Ldap Configuration
Setting up Your Ldap Configuration
For example, ou=people, o=bambi.com
For example, ou=accounts, ou=people, o=bambi.com
For example, uid. cn, homedirectory, gidnumber, uidnumber
Configuring the Kerberos Server with Ldap
Autoconfiguring the Kerberos Server With Ldap Integration
Step Select one of the following options
Qualified host name or the IP address
HpKrbKey
Autoconfiguring the Kerberos Server With Ldap Integration
Editing the Configuration Files
Manually Configuring the Kerberos Server with Ldap
Manually Configuring the Kerberos Server with Ldap
Manually Configuring the Kerberos Server with Ldap Chapter
Configuring the Primary
Configuring the Primary Security Server
Create the Principal Database After Installation
To add an Administrative Principal Using the HP Kerberos
Add an Administrative Principal
Administrator
To Add an Administrative Principal Through the Command Line
Start the Kerberos Daemons
Define Secondary Security Server Network Locations
Adminaclfile
Password Policy File
Security Policies
Starting the Security Server
Creating the Principal Database
Configuring the Secondary Security Servers with C-Tree
Copying the Kerberos Configuration File
Creating a host/fqdn Principal and Extracting the Key
Configuring the Secondary Security Servers with Ldap
Creating a stash file using the kdbstash utility
106
Using Indexes to Improve Database Performance
108
Administering the Kerberos
110
Administering the Kerberos Database
Configuration Files Required for kadmind
Kadmind Command
File Name Description
Adminaclfile File
Assigning Administrative Permissions
Chapter 115
Adding Entries to adminaclfile
Using Restricted Administrator
Creating Administrative Accounts
How the r/R Modifiers Work
118
Password Policy Setting Default Value
Password Policy File
Editing the Default File
Default Password Policy Settings for the Base Group
120
Principals
122
Adding User Principals
Adding New Service Principals
Reserved Service Principals
Chapter 125
126
Removing User Principals
Removing Special Privilege Settings
Protecting a Secret Key
Removing Service Principals
Chapter 129
Kadmin and kadminl Utilities
Administration Utilities Name Description
Administration Utilities
HP Kerberos Administrator
Button Name Action
Standard Functionality of the Administrator
Function of OK, Apply, and Cancel Buttons
Cancel
Using kadminlui
Local Administrator kadminlui
Chapter 135
Principals Tab
Principals Tab Components
Principals Tab
List of Principals
Component Name Description List All
Search String
Search
Principal Information Window
General Tab Principal Information Window
Principal Information Window Components
Attributes Tab
Password Tab
Field Name Description
General Tab
Maximum Renew Time
General Tab Components
Field Name Description Principal Expiration
Maximum Ticket Lifetime
Last Modified
Field Name Description Password Policy
Modified By
Adding Principals to the Database
Change Password Window
Adding Multiple Principals with Similar Settings
Creating an Administrative Principal
Administering the Kerberos Server
148
Search Criteria
Searching for a Principal
Character Description
150
Deleting a Principal
Loading Default Values for a Principal
Restoring Previously Saved Values for a Principal
Changing Ticket Information
Rules for Setting Maximum Ticket Lifetime
Rules for Setting Maximum Renew Time
Chapter 157
Changing Password Information
Chapter 159
Displays the Ldap DN that you are editing
Password Tab Principal Information
Password Tab Components
Window
Expiration/Date
Component Name Description Password
Password Last
Change Password
Change Password Window Password Tab
Change Password Window Components
Entering a password
Verification
Components Description New Password
Changing a DES-CRC or DES-MD5 Principal Key Type
Changing a Key Type
To 3DES
166
Changing Principal Attributes
12 describes the components of the Attributes tab
Attributes Tab Principal Information
Attributes Tab Components
Tickets
Components Description
Allow Postdated
Allow Renewable
170
Session Keys
Components Description Allow Forwardable
Allow Proxy
Allow Duplicate
Change
Preauthentication
Require Password
Components Description Require
Components Description Lock Principal
Allow As Service
Components Description Require Initial
Authentication
Set As Password
Change Service
Ldap Attributes Tab Prinicpal Information Window
176
Deleting a Service Principal
Extracting Service Keys
Chapter 179
Extracting a Service Key Table
Table Type
Extract Service Key Table Components
Service Key
Component Description Principal
Editing the Default Group
Using Groups to Control Settings
Chapter 183
Group Information Window Principal
Group Information Window Components
InformationEditEdit Default Group to display the Group
Component Description Group
Component Description
Setting the Default Group Principal Attributes
Default Principal Attributes
Principal Attributes
Chapter 187
Setting Administrative Permissions
11 Administrative Permissions Window
Administrative Permissions
Principals Inquire about
Add Principals
Principals
Modify
Component Description Restricted
Override the Principal InformationEditEdit Group Default
Defaults
InformationEditEdit Default GroupGroup Information
192
Realms Tab
Realms Tab Components
Realms Tab
Realm Information Window Components
Realm Information Window
Adding a Realm
Deleting a Realm
Remote Administrator kadminui
Logon Screen
Logon screen displays as shown in Figure
200
Chapter 201
Manual Administration Using kadmin
Chapter 203
Adding a New Principal
Adding a Random Key
Specifying a New Password
Deleting a Principal
Changing Password to a New Randomly Generated
3DES
Extracting a Principal
Modifying a Principal
Listing the Attributes of a Principal
Number of Authentication Failures fcnt
Key Version Number Attribute
Attributes
Policy Name
Allow Postdated Attribute
Allow Renewable Attribute
Allow Forwardable Attribute
Allow Proxy Attribute
Allow Duplicate Session Key Attribute
Require Password Change Attribute
Require Preauthentication Attribute
Lock Principal Attribute
Allow As Service Attribute
Principal InformationEditEdit Administrative Permissions
Require Initial Authentication Attribute
Authentication Set As Password Change Service Attribute
Authentication Select Require Initial
No text shows
Password Expiration Attribute
Maximum Ticket Lifetime Attribute
Principal Expiration Attribute
Key Type Attribute
Maximum Renew Time Attribute
Salt Type Attribute
Principal Database Utilities
Principal Database Utilities
Utility Task
Kerberos Database Utilities
226
Database Encryption
Database Master Password
Destroying the Kerberos Database
230
Dumping the Kerberos Database
Loading the Kerberos Database
Stashing the Master Key
234
Starting and Stopping Daemons
Starting and Stopping Daemons and Services Situation
Host/fqdn@REALM
Maintenance Tasks
Master Password
Protecting Security Server Secrets
Backing Up the Principal Database
Backing Up primary security server Data
238
Removing Unused Space from the Database
240
Propagating the Kerberos
242
Propagation Relationships
Propagation Hierarchy
Extracting a Key to the Service Key Table File
Service Key Table
Maintaining Secret Keys in the Key Table File
Deleting Older Keys from the Service Key Table File
Creating a New Service Key Table File
Propagation Tools If You Want To Use This Tool
Propagation Tools
One or more servers once Propagation is configured Started
Kpropd Daemon
Mkpropcf Tool
250
Kpropd.ini File
Sections
Defaultvalues Section
Chapter 253
Secsrvname Section
Configuration file
Examples
256
Prpadmin Administrative Application
Setting Up Propagation
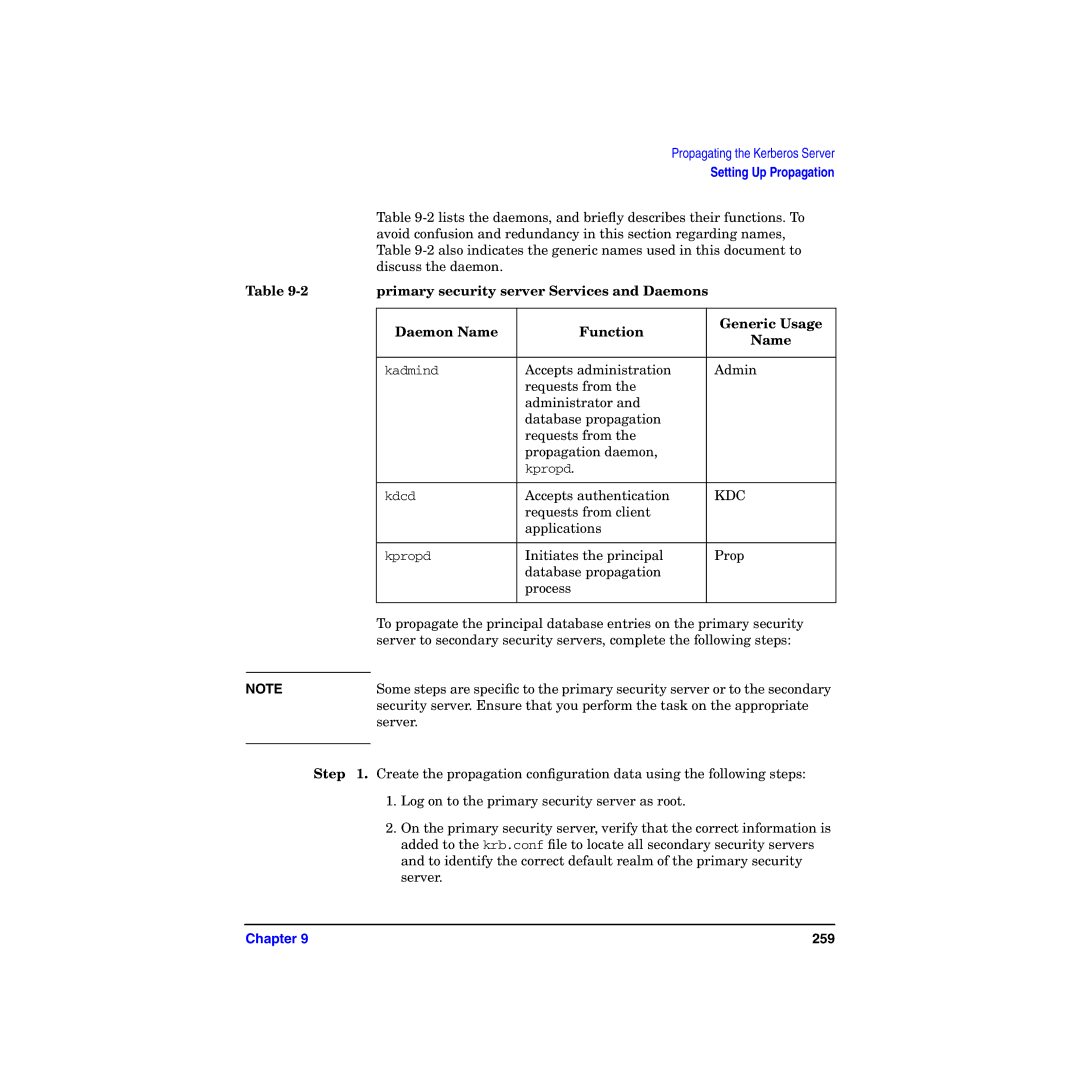
Daemon Name Function Generic Usage
Primary security server Services and Daemons
260
Chapter 261
262
Monitoring Propagation
Critical Error Messages
Monitoring the Log File
Monitoring Old File Date and Large File Size
Monitoring Propagation Queue Files
Updating the principal.ok Time Stamp
Authentication problems
Comparing the Database to Its Copies
Log files indicate problems
Administration appears normal
Mismatch between the number of principals
Kdbdump Utility
Restarting Propagation Using the Full Dump Method
Restarting Propagation Using a Simple Process
Propagation Failure
Security server
Converting a secondary security server to a primary
Cleaning the Temp Directory
Restarting Services
Number of Realms per Database
Configuring Multirealm Enterprises
Primary security servers Supporting Multiple Realms
Adding More Realms to a Multirealm Database
Multiple primary security servers Supporting a Single Realm
Database Propagation for Multirealm Databases
Managing Multiple Realms
276
One-Way Trust
Considering a Trust Relationship
Two-Way Trust
Other Types of Trust
Hierarchical Trust
Configuring Direct Trust Relationships
280
Hierarchical Chain of Trust
Hierarchical Interrealm Trust
Hierarchical Interrealm Configuration
Chapter 283
Configuring the Local Realm
Configuring the Intermediate Realm
Configuring the Target Realm
Hierarchical Interrealm Trust Chapter 287
288
Troubleshooting
290
Characterizing a Problem
292
Diagnostic Tools
Diagnostic Tools Summary
Tool Description Name
Error Messages
Troubleshooting Kerberos
Logging Capabilities
Unix Syslog File
Troubleshooting Techniques
Services Checklist
Troubleshooting Scenarios Cause Tips
Troubleshooting Scenarios
298
Server Scenario Cause Troubleshooting Tips
Troubleshooting Scenarios for your LDAP-based Kerberos
300
Chapter 301
302
Forgotten Passwords
General Errors
Clock Synchronization
Locking and Unlocking Accounts
Decrypt Integrity Check Failed
User Error Messages
Password Has Expired While Getting Initial Ticket
Administrative Error Messages
Service Key Not Available While Getting Initial Ticket
Chapter 307
Reporting Problems to Your HP Support Contact
Chapter 309
310
Configuration Worksheet
Appendix a
Appendix a 313
314
Sample krb.conf File
Appendix B
Services File
318
Sample krb.realms File
Appendix C
Key Distribution Center See KDC
Glossary
Glossary
Ticket-granting ticket See TGT
V5srvtab
Ticket-granting ticket
Index
Symbols
326
327