UPI-C42/UPI-L42
290414 – 14
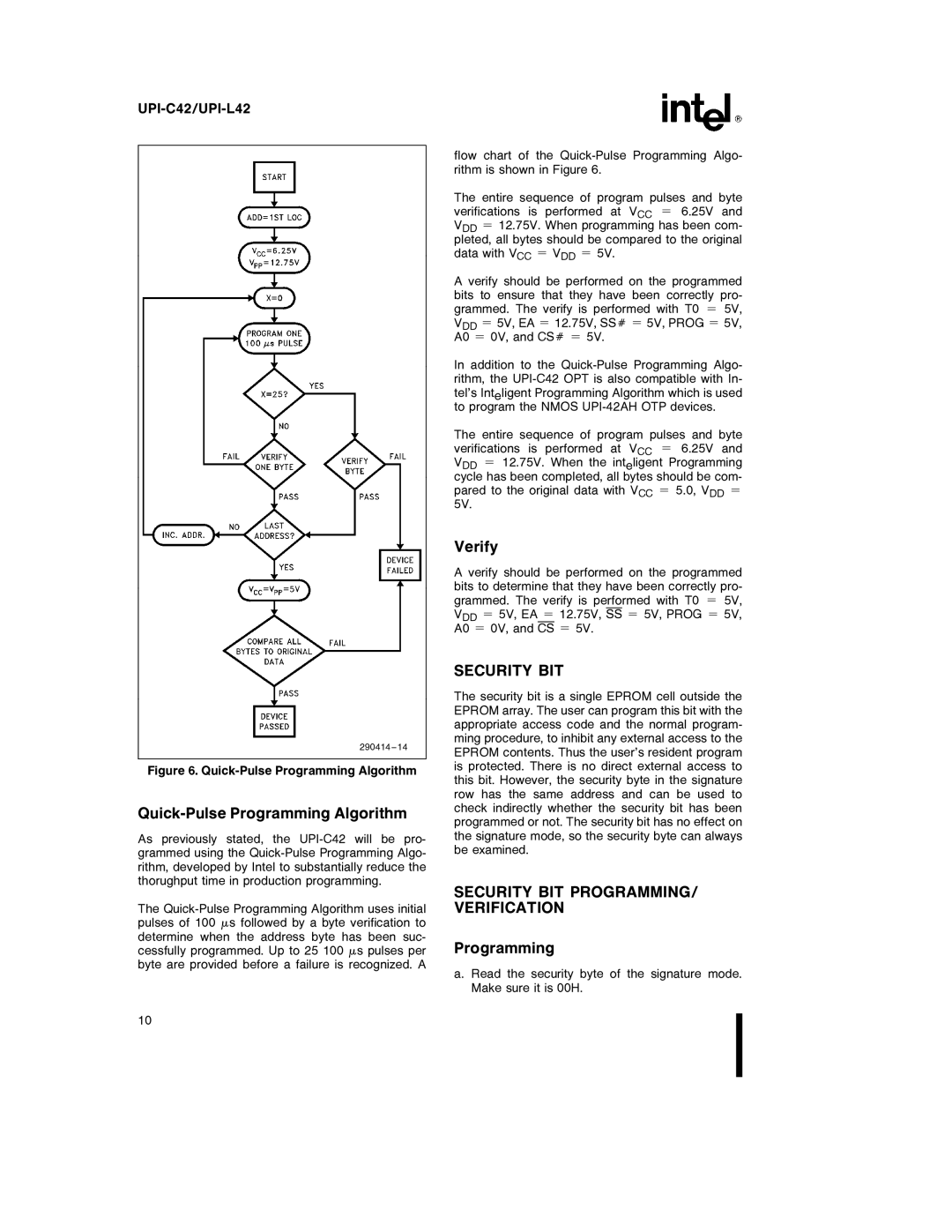
Figure 6. Quick-Pulse Programming Algorithm
Quick-Pulse Programming Algorithm
As previously stated, the
The
flow chart of the
The entire sequence of program pulses and byte verifications is performed at VCC e 6.25V and VDD e 12.75V. When programming has been com- pleted, all bytes should be compared to the original data with VCC e VDD e 5V.
A verify should be performed on the programmed bits to ensure that they have been correctly pro- grammed. The verify is performed with T0 e 5V, VDD e 5V, EA e 12.75V, SSÝ e 5V, PROG e 5V, A0 e 0V, and CSÝ e 5V.
In addition to the
The entire sequence of program pulses and byte verifications is performed at VCC e 6.25V and VDD e 12.75V. When the inteligent Programming cycle has been completed, all bytes should be com- pared to the original data with VCC e 5.0, VDD e 5V.
Verify
A verify should be performed on the programmed bits to determine that they have been correctly pro- grammed. The verify is performed with T0 e 5V, VDD e 5V, EA e 12.75V, SS e 5V, PROG e 5V,
A0 e 0V, and CS e 5V.
SECURITY BIT
The security bit is a single EPROM cell outside the EPROM array. The user can program this bit with the appropriate access code and the normal program- ming procedure, to inhibit any external access to the EPROM contents. Thus the user’s resident program is protected. There is no direct external access to this bit. However, the security byte in the signature row has the same address and can be used to check indirectly whether the security bit has been programmed or not. The security bit has no effect on the signature mode, so the security byte can always be examined.
SECURITY BIT PROGRAMMING/ VERIFICATION
Programming
a. Read the security byte of the signature mode. Make sure it is 00H.
10