6500 Series Residential Gateway User’s Guide | Configuring Advanced Features |
Attack Detection
If the Attack Detection System is enabled, the Gateway provides protection against the most common hacker attacks that attempt to access your computer/network from the Internet. Intrusion attempts can also be logged to provide a record of attempts and their source (when available).
To enable and configure the attack detection feature:
1.Select Attack Detection from the “Firewall Settings” window.
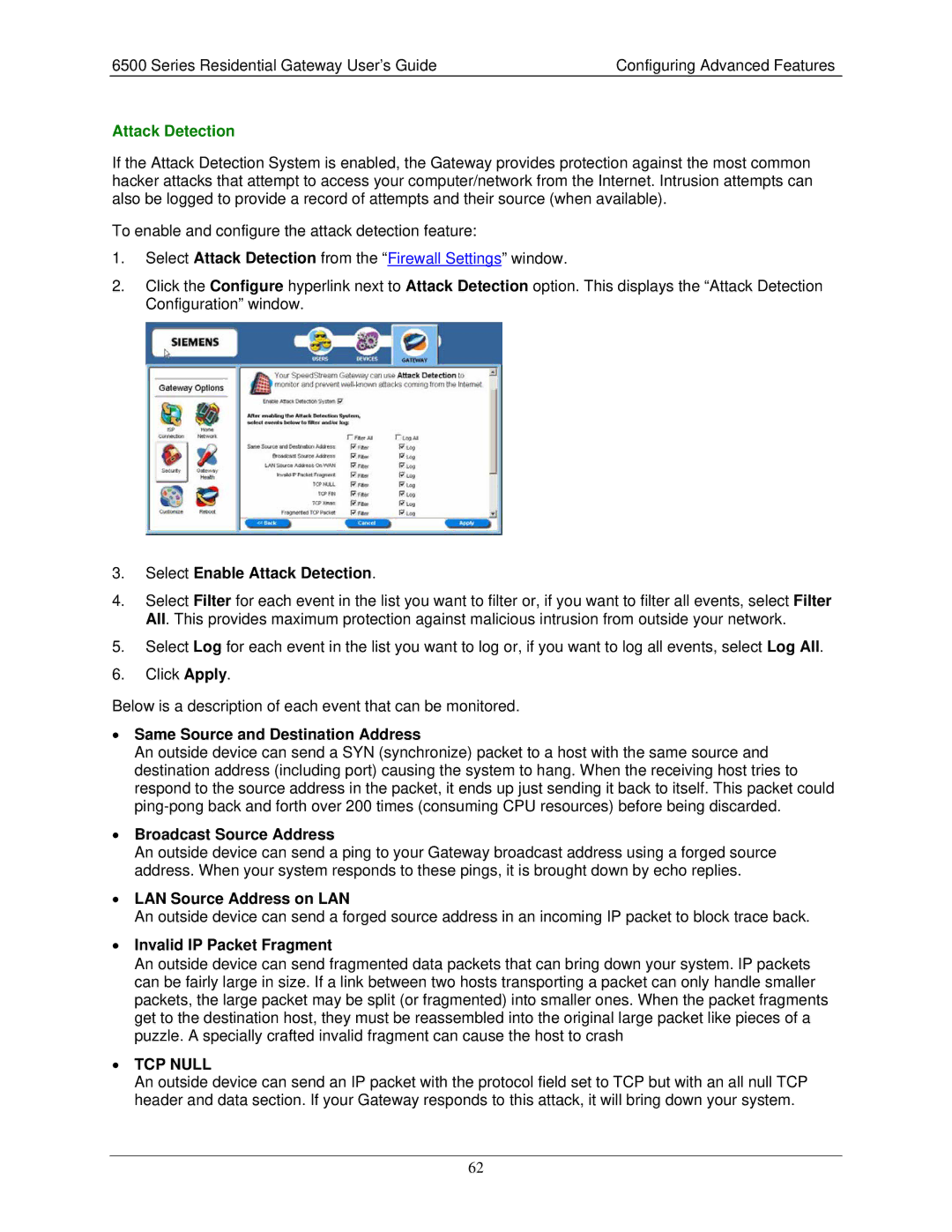
2.Click the Configure hyperlink next to Attack Detection option. This displays the “Attack Detection Configuration” window.
3.Select Enable Attack Detection.
4.Select Filter for each event in the list you want to filter or, if you want to filter all events, select Filter All. This provides maximum protection against malicious intrusion from outside your network.
5.Select Log for each event in the list you want to log or, if you want to log all events, select Log All.
6.Click Apply.
Below is a description of each event that can be monitored.
•Same Source and Destination Address
An outside device can send a SYN (synchronize) packet to a host with the same source and destination address (including port) causing the system to hang. When the receiving host tries to respond to the source address in the packet, it ends up just sending it back to itself. This packet could
•Broadcast Source Address
An outside device can send a ping to your Gateway broadcast address using a forged source address. When your system responds to these pings, it is brought down by echo replies.
•LAN Source Address on LAN
An outside device can send a forged source address in an incoming IP packet to block trace back.
•Invalid IP Packet Fragment
An outside device can send fragmented data packets that can bring down your system. IP packets can be fairly large in size. If a link between two hosts transporting a packet can only handle smaller packets, the large packet may be split (or fragmented) into smaller ones. When the packet fragments get to the destination host, they must be reassembled into the original large packet like pieces of a puzzle. A specially crafted invalid fragment can cause the host to crash
•TCP NULL
An outside device can send an IP packet with the protocol field set to TCP but with an all null TCP header and data section. If your Gateway responds to this attack, it will bring down your system.
62