Version Oct
Prestige 2602HWL-D3A
Prestige 2602HWL-D3A Support Notes
FAQ
Pstn L Ifeline FAQ
IP FAQ
Ontent F Ilter FAQ
Ireless FAQ
Application Notes
Ethernet connection
All PCs must have an Ethernet adapter card installed
TCP/IP Installation
∙ Setting up the Prestige router
TCP/IP Configuration
Follow these steps to configure Windows TCP/IP
Prestige 2602HWL-D3A Support Notes
∙ What is Dhcp Relay?
Setup the Prestige as a Dhcp Relay
∙ Setup the Prestige as a Dhcp Client
Configure an Internal Server Behind SUA
Edit IP Alias= No Press Enter to Confirm or ESC to Cancel
Service Port Number
Configure a Pptp server Behind SUA
∙ Example
1723 192.168.1.10
Prestige 2602HWL-D3A Support Notes
∙ What is Multi-NAT?
Using NAT / Multi-NAT
Many to One
One to One
Many to Many Overload
Many to Many No Overload
Applying NAT in the SMT Menus
Following table summarizes these types
NAT Type IP Mapping Direction
Field Options Description
Full Feature
None
SUA Only
Address Mapping Sets and NAT Server Sets
Configuring NAT
Table Applying NAT in Menu 4 and Menu
Prestige 2602HWL-D3A Support Notes
SUA
Field Description Option/Example
Description Option
Field
Following table describes the fields in this screen
Enter 2 to go to Menu 15.2.1-NAT Server Setup
See the following figure
Internet Access Only
Prestige 2602HWL-D3A Support Notes
Internet Access with an Internal Server
Types are used
Type One-to-One
Start=
Name= Example3
Support Non NAT Friendly Applications
Type Many-to-Many No Overload
Start=
NAT Type IP Mapping
∙ SUA
∙ Filter Structure
About Filter & Filter Examples How does ZyXEL filter work?
∙ Filter Types and SUA
Prestige 2602HWL-D3A Support Notes
Menu
Protocol and device rule cannot be active together
Filter for blocking the web service
Create a filter set in Menu
Rule 2 for b.DNS request, TCP06/Port number
Rule one for a. http packet, TCP06/Port number
Rule 3 for c. DNS packet UDP17/Port number
Filter for blocking a specific client
Configuration Create a filter set in Menu 21, e.g., set
Enter the client IP in this field
One rule for blocking all packets from this client
Addr= field, for one workstation it is
Set to Drop to drop all the packets from this client
Detailed format of the Ethernet Version
Before you Begin
Configurations
Action Matched= Drop Action Not Matched= Forward
Value= 0080c810234a
Filter for blocking the NetBIOS packets
Action Not Matched= Check Next Rule
Prestige 2602HWL-D3A Support Notes
Prestige 2602HWL-D3A Support Notes
Menu 21.1.6 TCP/IP Filter Rule Filter # 1,6
Prestige 2602HWL-D3A Support Notes
Prestige 2602HWL-D3A Support Notes
Menu 3.1 General Ethernet Setup Input Filter Sets
Using the Dynamic DNS Ddns
Key Settings for using Ddns function
Network Management Using Snmp
Password Enable Wildcard
Writes
∙ GetNext
∙ Get
∙ Set
∙ Trap
ZyXEL Snmp Implementation
∙ warmStart defined in RFC-1215
Configure the Prestige for Snmp
Using syslog
∙ Unix Setup
∙ Filter log
L02 Call Terminated C02 Call Terminated Example
∙ Packet triggered log
Format SdcmdSyslogSend SYSLOGPPPLOG, SYSLOGNOTICE, String
∙ PPP Log
∙ What is IP Alias ?
Using IP Alias
Dhcp Setup TCP/IP Setup
IP Alias
Using Call Scheduling
Select a Schedule Set number and give it a name
Edit the Schedule sets in menu
Menu 26.1 Schedule Set Setup is as follows
Start Date How Often Forced On Forced Down
Enable
∙ Time Service in Prestige
∙ IP Multicast Setup Enable Igmp in Prestiges LAN in menu
Using IP Multicast
Multicast
Enable Igmp in Prestiges remote node in menu
You can deploy the backup gateway on LAN of Prestige
Using Prestige traffic redirect
SMT Menu 2 WAN Backup Setup
Traffic Redirect on LAN port
WAN IP
∙ 1. What is UPnP
Using Universal Plug n Play UPnP
UPnP Operations
Enable UPnP function in ZyXEL device
∙ 2. Using UPnP in ZyXEL devices
Changes through UPnP
Prestige 2602HWL-D3A Support Notes
Finally, your video conversation is achieved
What is Infrastructure mode?
Infrastructure mode
Configuration Prestige Wireless using SMT
Prestige 2602HWL-D3A Support Notes
∙ Configuration Wireless Station to Infrastructure mode
Double click on the AP you want to associated with
MAC Filter Overview
Wireless MAC address filtering
Filter Action
Key Settings Option Descriptions
Configured in this list will be blocked
Prestige 2602HWL-D3A Support Notes
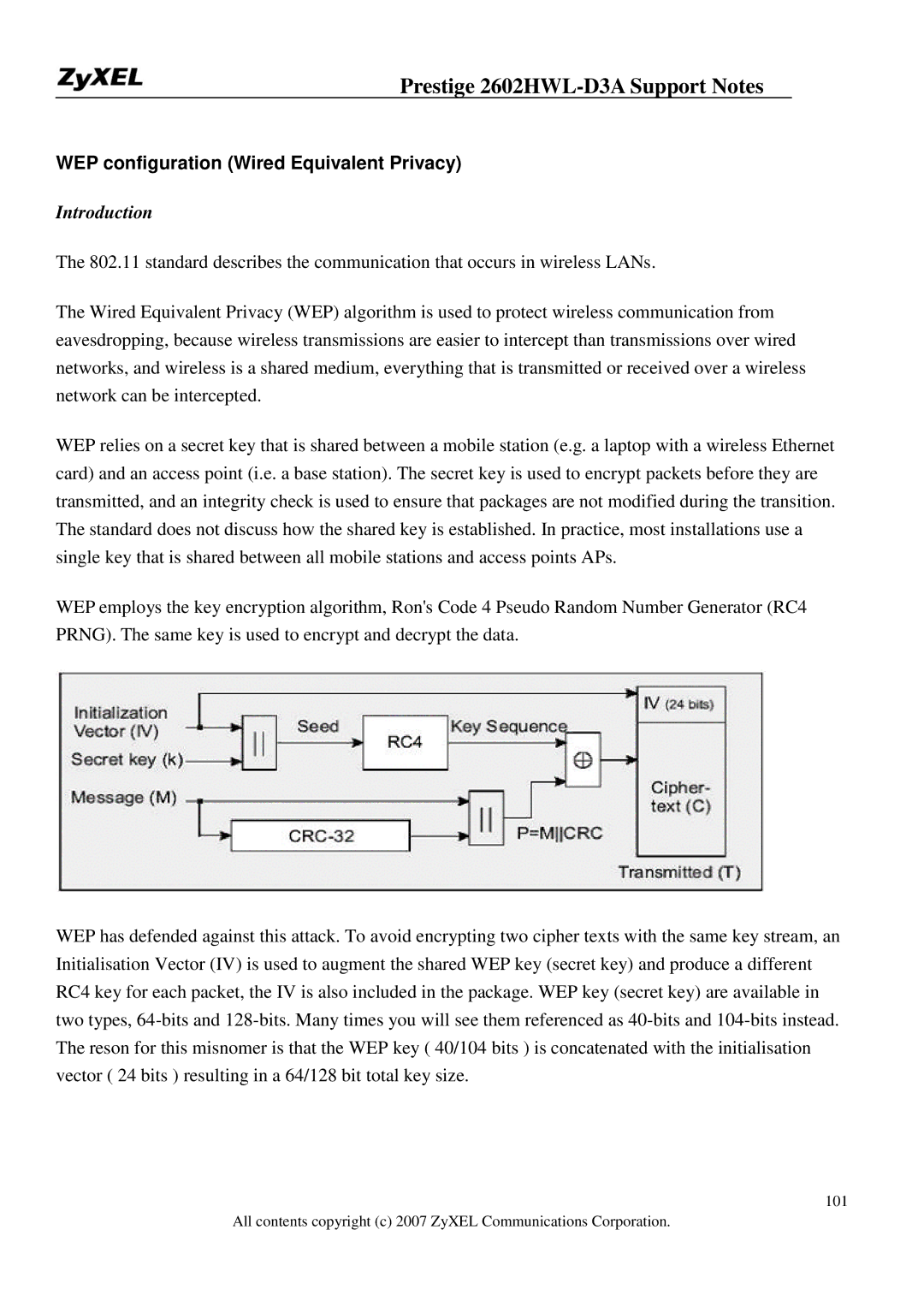
Introduction
WEP configuration Wired Equivalent Privacy
Setting up the Access Point
Key settings
Access point will decrypt the data by its Key
Setting up the Station
Prestige 2602HWL-D3A Support Notes
Prestige 2602HWL-D3A Support Notes
Ieee 802.1x Introduction
Configuring
Supplicant
Authenticator
Authentication Server
∙ Authentication Port State and Authentication Control
∙ Re-Authentication
Eapol Exchange between 802.1x Authenticator and Supplicant
Prestige 2602HWL-D3A Support Notes
Prestige 2602HWL-D3A Support Notes
Wireless Port Control= No Authentication Required
If you use WEB Configuration
∙ Using Internal Authentication Server
Password
Key settings
If you use WEB Configurator
User Name
∙ Using External Radius Authentication Server
Prestige 2602HWL-D3A Support Notes
Server Address Port Shared Secret
Key settings for authentication server
Preparation
Site Survey
Survey on Site
Prestige 2602HWL-D3A Support Notes
Usage of Pstn Lifeline
Pstn Lifeline Application Notes
Lifeline configuration
Firgure 1 Splitter type
How to connect Lifeline and DSL connection
Relay to Pstn
VoIP Application Notes
Setup SIP Account
Number
Account
Local
Port
Setup
Password
Reset
Address SIP Server
Phone port settings
Advanced voice settings configuration
Volume
Speaking
Listening
SIP Account
Each fields detail description of the page is listed below
Dtmf Mode
Timer
URL Type
Expiration
Waiting
Message
Indication
Time
Each fields detail description of the page is listed below
SIP Number
Speed Dial
Name
Type
Settings
Voice Common Settings
Region
Immediate
Voice QoS setup
Call Service Mode
Services from your voice service provider
Voice Vlan
Call Forwarding setup
Priority
No Answer Forward to Number
Unconditional Forward to Number
Busy Forward to Number
Forward to
Table Number
Unconditional
Busy Forward
Call Hold setup
Number Setup section
Call Waiting setup
Condition
Scenario
Prestige 2602HWL-D3A Support Notes
Get a dial tone
Three Way Conference setup
Dial B phone number directly to make another call
Three-way conversation
Dial to B Off hook B conversation
Call Transfer setup
Prestige 2602HWL-D3A Support Notes
Application scenario 3 Attendant Transfer
Call Fallback
Prestige 2602HWL-D3A Support Notes
Call Park Call Flow
Call Return
Call Pickup Call Flow
Distinctive Ringing
Each filed is described in the following table
Do Not Disturb DND
Hot Line Auto Dial
Music on hold
Ras voice config fxs save
Setting Advanced
Trunking
Trunking Peer to Peer
Configuration details
Prestige 2602HWL-D3A Support Notes
Prestige 2602HWL-D3A Support Notes
VoIP Trunking General
Trunking SIP to FXO
Trunking FXO to SIP
On Device B No special configuration needed
Prestige 2602HWL-D3A Support Notes
Trunking FXO to FXO
Prestige 2602HWL-D3A Support Notes
Prestige 2602HWL-D3A Support Notes
How do I access the embedded web configurator?
What is ZyNOS?
Prestige 2602HWL-D3A Support Notes
Why cant I make Telnet to Prestige from WAN?
How do I upload or backup Romfile via web configurator?
What is the difference between NAT and SUA?
What should I do if I forget the system password?
What is SUA? When should I use SUA?
What is the Prestige Integrated Access Device?
Why cant I configure device filters or protocol filters?
How many network users can the SUA/NAT support?
What are Device filters and Protocol filters?
How do I know I am using PPPoE?
What is PPPoE?
Will the Prestige work with my Internet connection?
What do I need to use the Prestige?
How can I configure the Prestige?
Why does my provider use PPPoE?
Which Internet Applications can I use with the Prestige?
What network interface does the Prestige support?
What Dhcp capability does the Prestige support?
Default IP address is 192.168.1.1, Password
How does e-mail work through the Prestige?
How fast can the data go?
How does the Prestige support TFTP?
Can the Prestige support Tftp over WAN?
When do I need Multi-NAT?
What is Multi-NAT?
Server
What IP/Port mapping does Multi-NAT support?
What is DDNS?
What is the difference between SUA and Multi-NAT?
What is BOOTP/DHCP?
When do I need Ddns service?
Do I need Lifeline?
What does Lifeline mean?
Can I connect more than one phone on the phone port?
Can I receive incoming Pstn call through P2602HWL- 6xC?
Why use VoIP?
What is Voice over IP?
What is the relationship between codec and VoIP?
Can I make an outgoing Pstn call through P2602HWL 6xC?
What is voice quality?
What is the difference between H.323 and SIP?
What is codec?
What advantage does Voice over IP can provide?
What codec does Prestige support?
What is the relation of codec and VoIP?
Which codec should I choose?
What do I need in order to use SIP?
Can register but can not establish a call?
Unable to register with the SIP server?
What are the basic types of firewalls?
What is a network firewall?
What makes Prestige firewall secure?
What kind of firewall is the Prestige?
What is Ping of Death attack?
What is Denials of Service DoSattack?
What is Teardrop attack?
What is SYN Flood attack?
What is Brute-force attack?
What is Land attack?
What is IP Spoofing attack?
What are the default ACL firewall rules in Prestige?
How can I protect against IP spoofing attacks?
Why do I need VPN?
What is VPN?
Can I override block or allow certain URLs by wording?
Security
What is L2TP?
What is PPTP?
What is IPSec?
Cost
What secure protocols does IPSec support?
What is SA?
What is IKE?
What is Phase 1 ID for?
What is Pre-Shared Key?
What are the differences between IKE and manual key VPN?
What are Local ID and Peer ID?
How do I configure Prestige VPN?
When should I use FQDN?
Is my Prestige ready for IPSec VPN?
How many VPN connections does Prestige support?
What types of encryption does Prestige VPN support?
What types of authentication does Prestige VPN support?
What VPN protocols are supported by Prestige?
Does Prestige support dynamic secure gateway IP?
Where can I configure Phase 1 ID in Prestige?
Does Prestige VPN support NetBIOS broadcast?
Will ZyXEL support Secure Remote Management?
Is the host behind NAT allowed to use IPSec?
We presume your environment may look like this
Can Prestige support IPSec passthrough?
How can I keep a tunnel alive?
What are the advantages of Wireless LANs ?
What is a Wireless LAN ?
Where can you find wireless 802.11 networks ?
What are the disadvantages of Wireless LANs ?
What is an Access Point ?
What is Ieee 802.11 ?
What is 802.11a ?
What is 802.11b ?
What is 802.11g ?
How fast is 802.11b ?
Does the 802.11 interfere with Bluetooth devices ?
What is Wi-Fi ?
Can radio signals pass through walls ?
What types of devices use the 2.4GHz Band ?
What is Infrastructure mode ?
What is Ad Hoc mode ?
How many Access Points are required in a given area ?
What is Direct-Sequence Spread Spectrum Technology Dsss ?
Why the 2.4 Ghz Frequency range ?
What is Frequency-hopping Spread Spectrum Technology Fhss ?
What is Server Set ID Ssid ?
What is an Essid ?
What is the difference between 40-bit and 64-bit WEP ?
What is WEP ?
What is a WEP key ?
Can the Ssid be encrypted ?
What are Insertion Attacks?
What is Wireless Sniffer?
What is 802.1x ?
What is WPA ?
What is AAA ?
What is Radius ?
What is WPA-PSK?
Trouble Shooting
Example
Online Trace
TCP/IP
0001
RAW Data
Urgent Ptr TCP Data Length=6 Captured=6 0000 20 20 20 20 20
Prestige 2602HWL-D3A Support Notes
Be 2F FE EF D0
7637 Checksum = 0x7A12 31250 Urgent Ptr
Offline Trace
TCP
0000 80 C8 A0-C5 0010 00 ED 0020 1B-18 FA F0 04-05 Prestige
224
Header Length Flags = 0x18 .AP Window Size 8760 Checksum
Debug PPPoE Connection
Example- a trace with system crashes
Prestige 2602HWL-D3A Support Notes
Prestige 2602HWL-D3A Support Notes
Trace LAN packet Trace WAN packet
LAN/WAN Packet Trace
Example
RAW Data
Size 60 Time 12090.210 sec Frame Type TCP
= 0xE8ED
0030 22 38 E8 ED 00 00 20 20-20 20 20
FB be 2F FE EF D0
CLI Command List