CRADLEPOINT IBR600 USER MANUAL Firmware ver. 3.3.0
7.7.3Page 3: IKE Phase 1
IKE security has two phases, Phase 1 and Phase 2. You have the ability to distinctly configure each phase, but the default settings will be sufficient for most users.
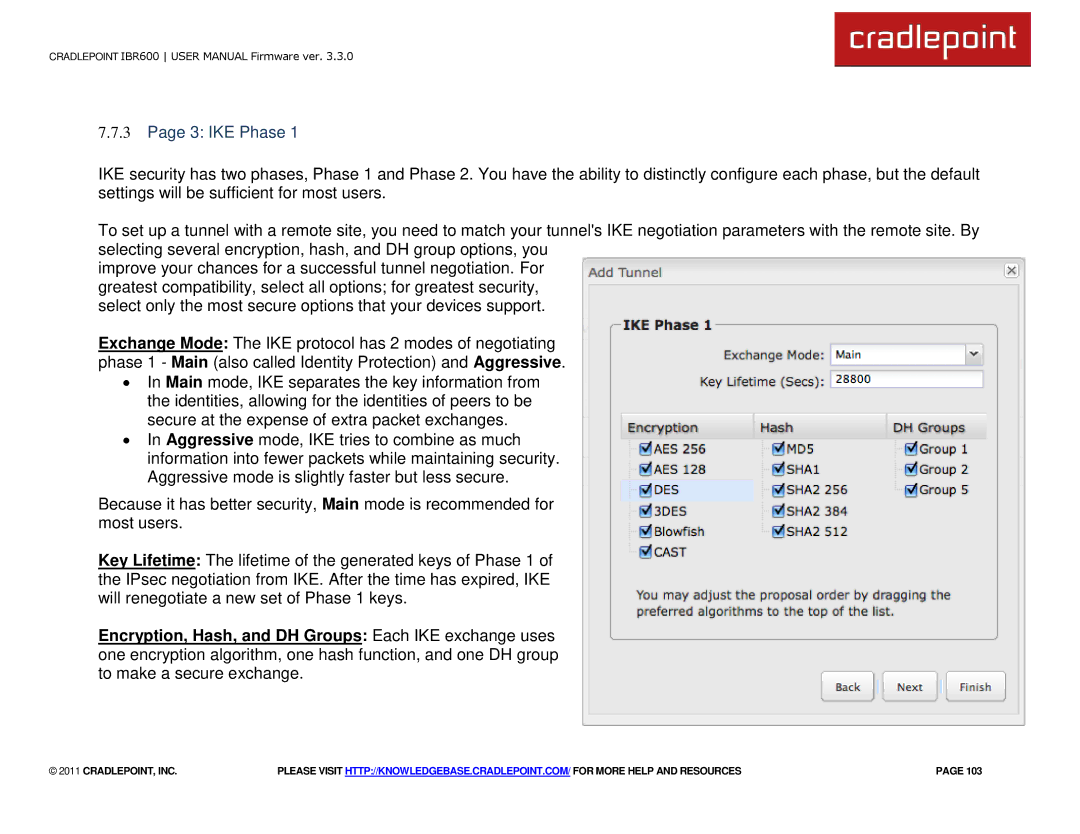
To set up a tunnel with a remote site, you need to match your tunnel's IKE negotiation parameters with the remote site. By selecting several encryption, hash, and DH group options, you
improve your chances for a successful tunnel negotiation. For greatest compatibility, select all options; for greatest security, select only the most secure options that your devices support.
Exchange Mode: The IKE protocol has 2 modes of negotiating phase 1 - Main (also called Identity Protection) and Aggressive.
∙In Main mode, IKE separates the key information from the identities, allowing for the identities of peers to be secure at the expense of extra packet exchanges.
∙In Aggressive mode, IKE tries to combine as much information into fewer packets while maintaining security. Aggressive mode is slightly faster but less secure.
Because it has better security, Main mode is recommended for most users.
Key Lifetime: The lifetime of the generated keys of Phase 1 of the IPsec negotiation from IKE. After the time has expired, IKE will renegotiate a new set of Phase 1 keys.
Encryption, Hash, and DH Groups: Each IKE exchange uses one encryption algorithm, one hash function, and one DH group to make a secure exchange.
© 2011 CRADLEPOINT, INC. | PLEASE VISIT HTTP://KNOWLEDGEBASE.CRADLEPOINT.COM/ FOR MORE HELP AND RESOURCES | PAGE 103 |