Lenovo ThinkVantage Tools
The Lenovo ThinkVantage® Tools program guides you to a host of information sources and provides easy access to various tools to help you work more easily and securely.
Note: The Lenovo ThinkVantage Tools program is only available on computers with the Windows 7 operating system from Lenovo.
To access the Lenovo ThinkVantage Tools program, click Start ➙ All Programs ➙ Lenovo ThinkVantage Tools.
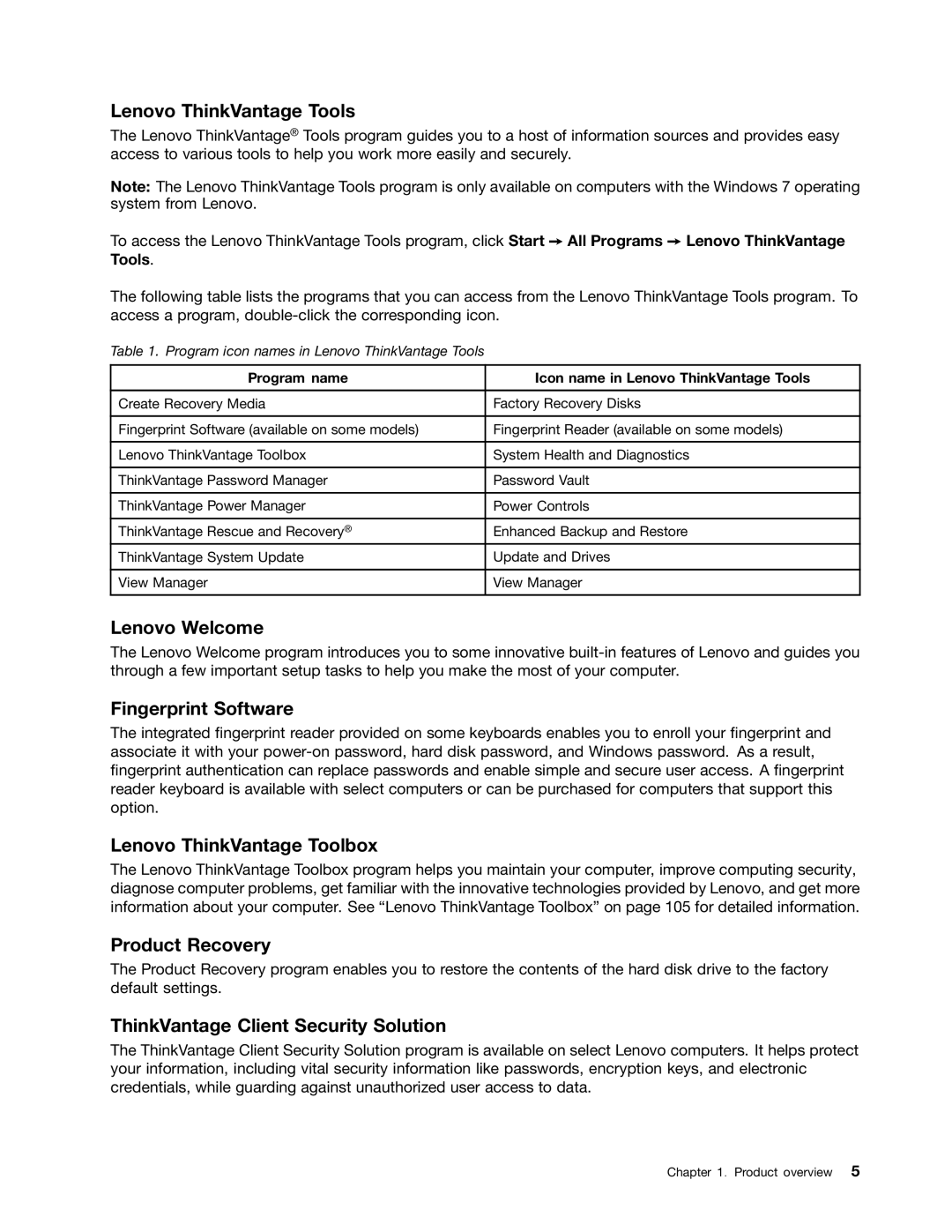
The following table lists the programs that you can access from the Lenovo ThinkVantage Tools program. To access a program,
Table 1. Program icon names in Lenovo ThinkVantage Tools
Program name | Icon name in Lenovo ThinkVantage Tools |
|
|
Create Recovery Media | Factory Recovery Disks |
|
|
Fingerprint Software (available on some models) | Fingerprint Reader (available on some models) |
|
|
Lenovo ThinkVantage Toolbox | System Health and Diagnostics |
|
|
ThinkVantage Password Manager | Password Vault |
|
|
ThinkVantage Power Manager | Power Controls |
|
|
ThinkVantage Rescue and Recovery® | Enhanced Backup and Restore |
ThinkVantage System Update | Update and Drives |
|
|
View Manager | View Manager |
|
|
Lenovo Welcome
The Lenovo Welcome program introduces you to some innovative
Fingerprint Software
The integrated fingerprint reader provided on some keyboards enables you to enroll your fingerprint and associate it with your
Lenovo ThinkVantage Toolbox
The Lenovo ThinkVantage Toolbox program helps you maintain your computer, improve computing security, diagnose computer problems, get familiar with the innovative technologies provided by Lenovo, and get more information about your computer. See “Lenovo ThinkVantage Toolbox” on page 105 for detailed information.
Product Recovery
The Product Recovery program enables you to restore the contents of the hard disk drive to the factory default settings.
ThinkVantage Client Security Solution
The ThinkVantage Client Security Solution program is available on select Lenovo computers. It helps protect your information, including vital security information like passwords, encryption keys, and electronic credentials, while guarding against unauthorized user access to data.
Chapter 1. Product overview 5