Chapter 2
Configuration
Key Management
Select Auto (IKE) or Manual from the
Auto (IKE)
Select Auto (IKE) and enter a series of numbers or letters in the
Manual
Select Manual, then select the Encryption Algorithm from the
Manual Key Management
Status
The status of the connection is shown.
Click Connect to connect your VPN tunnel. Click View Logs to view system, UPnP, VPN, firewall, access, or all logs. Click Advanced Settings and the Advanced IPSec VPN Tunnel Setup screen will appear.
System Log
When you have finished making changes to the Security > VPN screen, click Save Settings to save the changes, or click Cancel Changes to undo your changes.
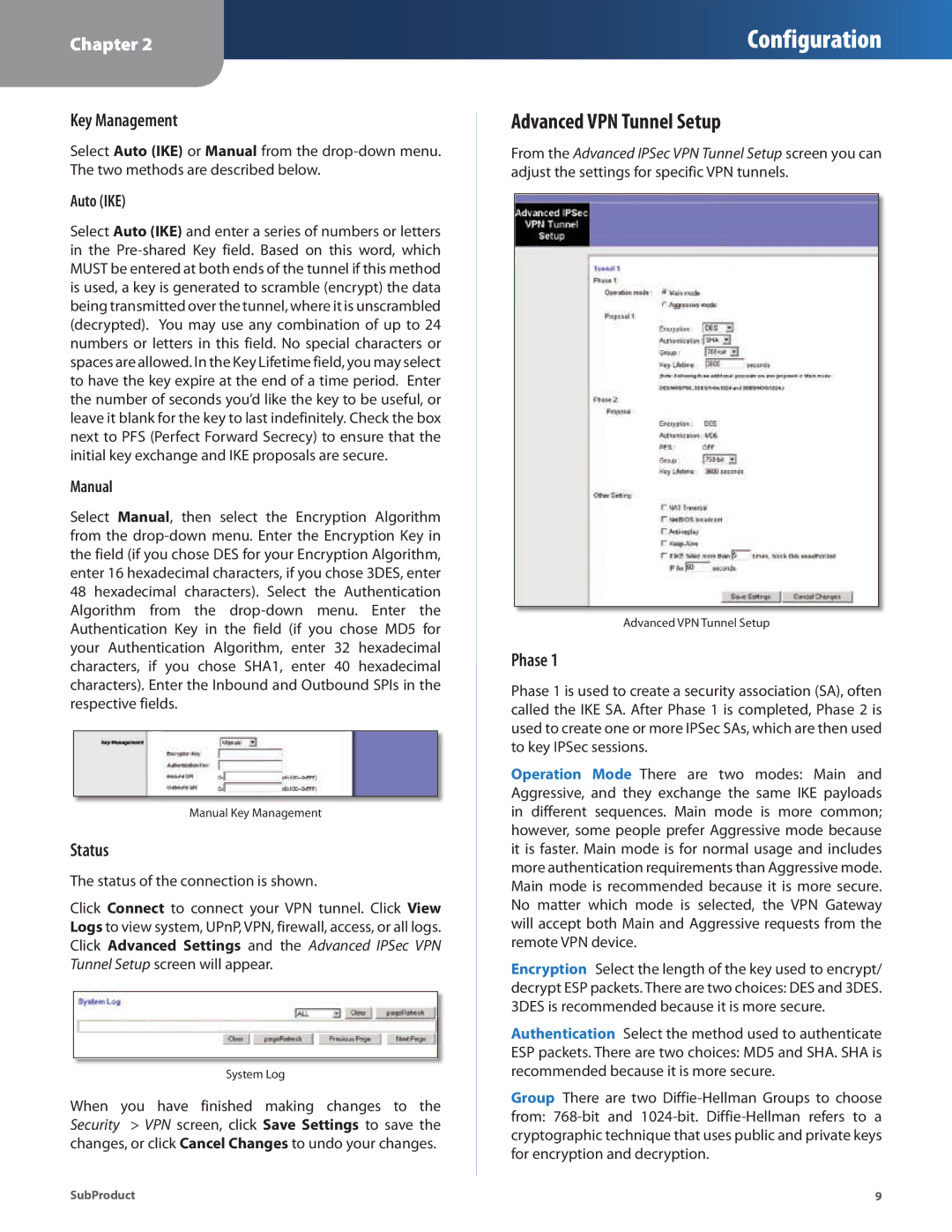
Advanced VPN Tunnel Setup
From the Advanced IPSec VPN Tunnel Setup screen you can adjust the settings for specific VPN tunnels.
Advanced VPN Tunnel Setup
Phase 1
Phase 1 is used to create a security association (SA), often called the IKE SA. After Phase 1 is completed, Phase 2 is used to create one or more IPSec SAs, which are then used to key IPSec sessions.
Operation Mode There are two modes: Main and Aggressive, and they exchange the same IKE payloads in different sequences. Main mode is more common; however, some people prefer Aggressive mode because it is faster. Main mode is for normal usage and includes more authentication requirements than Aggressive mode. Main mode is recommended because it is more secure. No matter which mode is selected, the VPN Gateway will accept both Main and Aggressive requests from the remote VPN device.
Encryption Select the length of the key used to encrypt/ decrypt ESP packets. There are two choices: DES and 3DES. 3DES is recommended because it is more secure.
Authentication Select the method used to authenticate ESP packets. There are two choices: MD5 and SHA. SHA is recommended because it is more secure.
Group There are two
SubProduct | 9 |