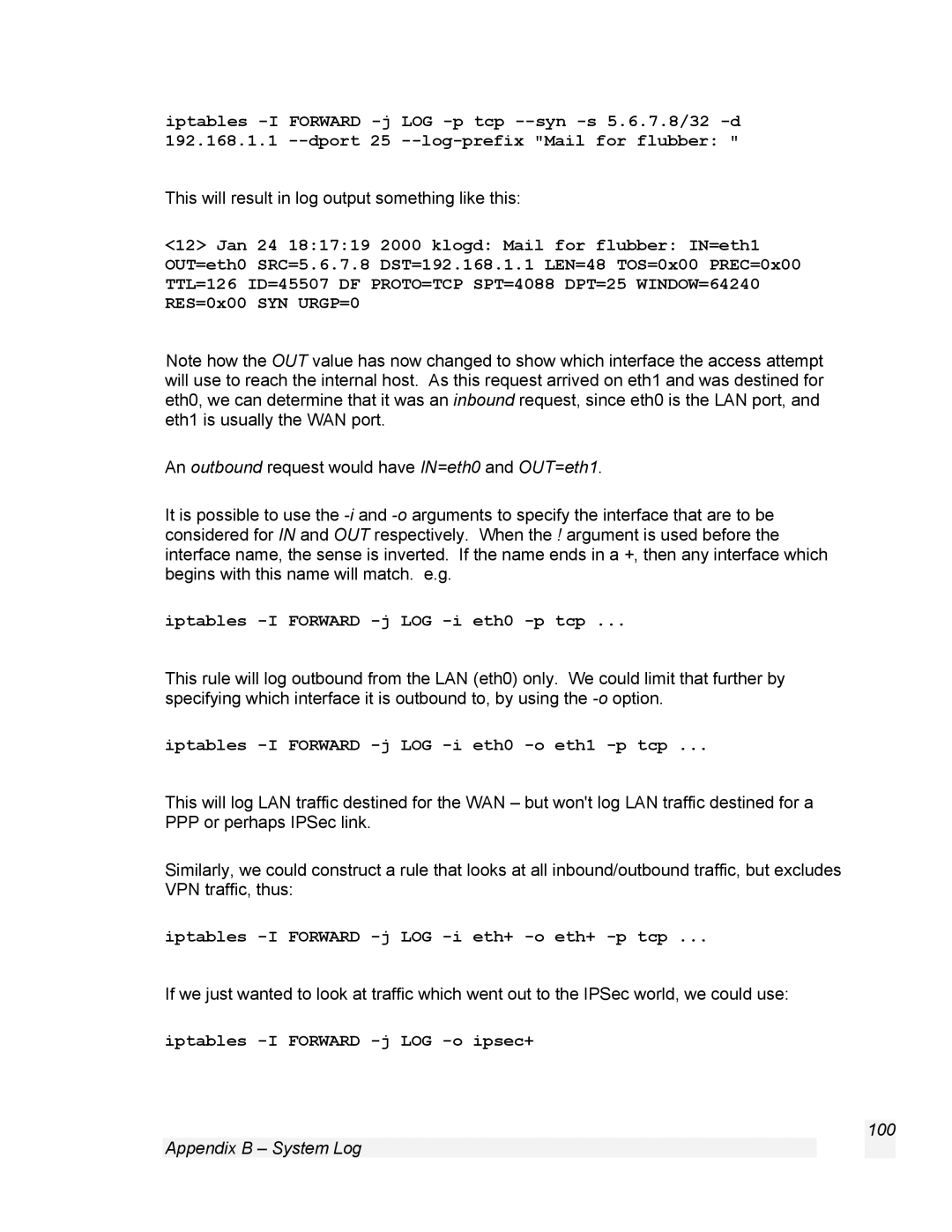
iptables
This will result in log output something like this:
<12> Jan 24 18:17:19 2000 klogd: Mail for flubber: IN=eth1 OUT=eth0 SRC=5.6.7.8 DST=192.168.1.1 LEN=48 TOS=0x00 PREC=0x00 TTL=126 ID=45507 DF PROTO=TCP SPT=4088 DPT=25 WINDOW=64240 RES=0x00 SYN URGP=0
Note how the OUT value has now changed to show which interface the access attempt will use to reach the internal host. As this request arrived on eth1 and was destined for eth0, we can determine that it was an inbound request, since eth0 is the LAN port, and eth1 is usually the WAN port.
An outbound request would have IN=eth0 and OUT=eth1.
It is possible to use the
iptables -I FORWARD -j LOG -i eth0 -p tcp ...
This rule will log outbound from the LAN (eth0) only. We could limit that further by specifying which interface it is outbound to, by using the
iptables -I FORWARD -j LOG -i eth0 -o eth1 -p tcp ...
This will log LAN traffic destined for the WAN – but won't log LAN traffic destined for a PPP or perhaps IPSec link.
Similarly, we could construct a rule that looks at all inbound/outbound traffic, but excludes VPN traffic, thus:
iptables -I FORWARD -j LOG -i eth+ -o eth+ -p tcp ...
If we just wanted to look at traffic which went out to the IPSec world, we could use: