Text Part Number OL-23874-01
Americas Headquarters
Page
N T E N T S
Manager
Disabling and Enabling Web Page Access
Network and Access Port Pinouts C-3
Installing the Bracket E-8
OL-23874-01
Audience
Overview
Organization
Chapter Description
Cisco Unified IP Phone 6900 Series
Related Documentation
Cisco Product Security Overview
Convention Description
Document Conventions
Italic font
Italic screen font
An Overview of the Cisco Unified IP Phone
1shows the main components of the Cisco Unified IP Phone
Understanding the Cisco Unified IP Phone 6901
OL-23874-01
2shows the main components of the Cisco Unified IP Phone
OL-23874-01
What Networking Protocols are Used?
Dynamic Host Configuration Protocol chapter
Networking Protocol Purpose Usage Notes
Communications Manager System Guide
Unified IP Phones section on page 1-17for
Supporting 802.1X Authentication on Cisco
See the LLDP-MED and Cisco Discovery Protocol
701/technologieswhitepaper0900aecd804cd46d
Cisco Unified Communications Manager
Communications Manager Security Guide
System Guide
Related Topics
Configuring Telephony Features
Feature Overview
Related Topic
Providing Users with Feature Information
OL-23874-01
Topic Reference
Refer to the Troubleshooting Guide for Cisco Unified
Communications Manager
Security, refer to the Cisco Unified Communications Manager
Feature Description
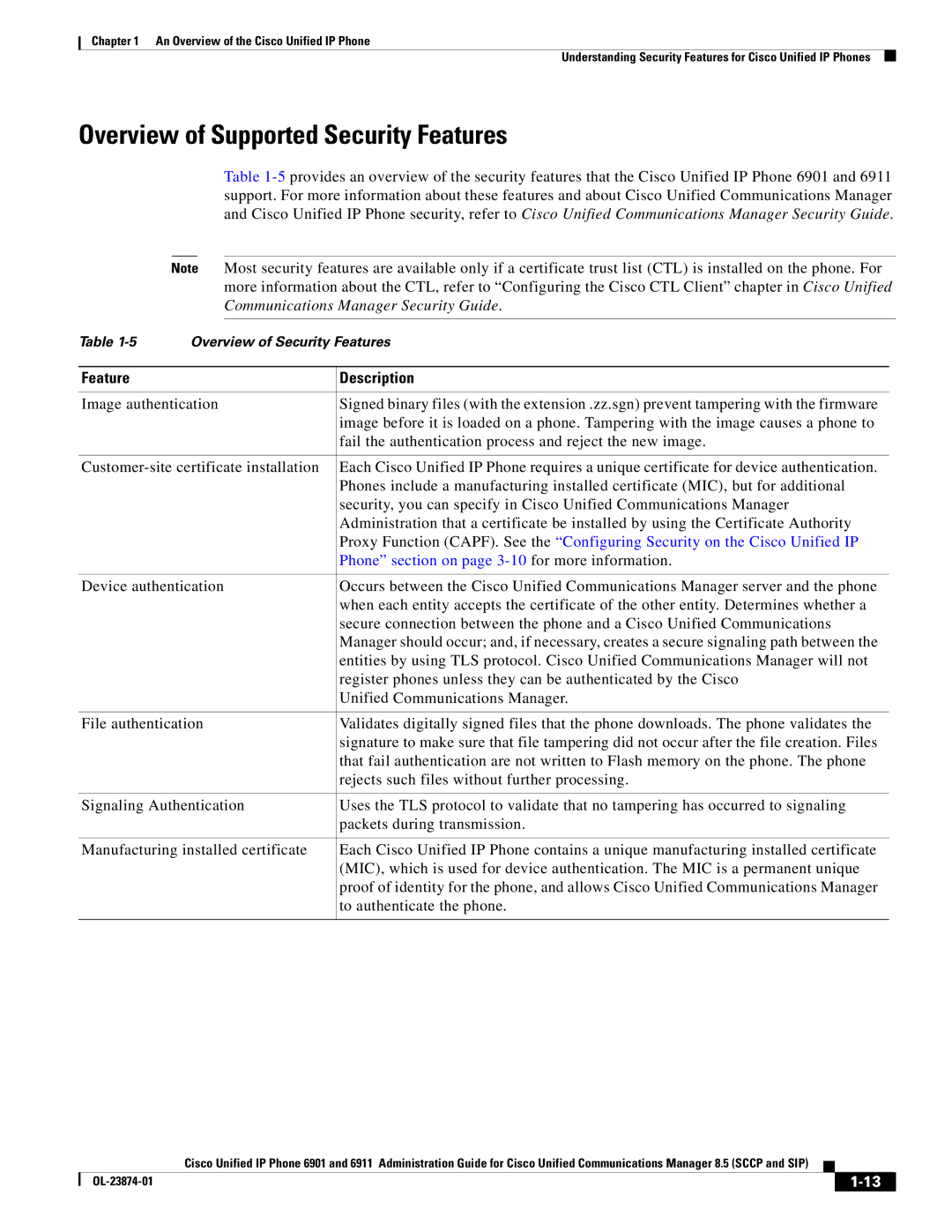
Overview of Supported Security Features
Phone section on page 3-10for more information
Voice Quality Metrics
IP Phones section on page 1-17for more information
Understanding Security Profiles
Establishing and Identifying Protected Calls
Overview
Supporting 802.1X Authentication on Cisco Unified IP Phones
Required Network Components
Best Practices-Requirements and Recommendations
OL-23874-01
Purpose For More Information
Communications Manager Administration
Communications Manager Administration Guide
Chapter in the Cisco Unified Communications Manager
Installing Cisco Unified IP Phones
Terminology Differences
User Guide Administration and System Guides
Refer to Cisco Unified IP Phone 6901
A P T E R
Cisco Communications Manager Administration Guide
Providing Power to the Cisco Unified IP Phone
Power Outage
Power Guidelines
Power Type Guidelines
Obtaining Additional Information About Power
Understanding Phone Configuration Files
Purpose Related Topics
Understanding the Phone Startup Process
Obtaining an IP Address
Method Address?
Adding Phones with Auto-Registration
Adding Phones with Auto-Registration and Taps
Procedure
Adding Phones Using the BAT Phone Template
Converting a New Phone from Sccp to SIP
Using Cisco Unified IP Phones with Different Protocols
Deploying a Phone in an Sccp and SIP Environment
Determining the MAC Address for a Cisco Unified IP Phone
Network Requirements
Before You Begin
Network and Access Ports
Cisco Unified Communications Manager Configuration
Speakerphone Cisco Unified IP Phone 6911 Only
Handset
See the Network and Access Ports section on
Installing the Cisco Unified IP Phone
Cisco Unified IP Phone 6901 Cable Connections
Cisco Unified IP Phone 6911 Cable Connections
3illustrates the footstand on the Cisco Unified IP Phone
Footstand
Lower Viewing Angle
Higher Viewing Angle
Mounting the Phone to the Wall
Configuring Startup Network Settings
Verifying the Phone Startup Process
Before You Begin
Configuring Security on the Cisco Unified IP Phone
Phone Settings Options
Configuring Settings on the Cisco Unified IP Phone
Option Description
Accessing the IVR and Configuring Your Phone Setting
Accessing the Phone Configuration Settings
Action IVR Code Navigating Notes
OL-23874-01
Configuring Features, Templates, Services, and Users
Features and Services Guide, Barge
Feature Description Configuration Reference
System Guide, Cisco Unified IP Phones
Unified Communications Manager
Unified Communications Manager Features
Features and Services Guide Barge
Services Guide
Administration Guide, Directory
Manager Features and Services Guide
Forward Maximum Hop Count service parameter
Features and Services Guide,Barge
Communications Manager Features
Point Configuration chapter in the Cisco
Codes and Forced Authorization Codes
Conference Bridges chapter
Administration Guide, Message Waiting
Number/Pattern Configuration chapter
Configuration chapter
System Guide, Voice Mail Connectivity
Administration Guide, Cisco Unified IP
Services Guide, Monitoring
Phone Configuration chapter
Administration Guide, Date/Time Group
Administration Guide, Time Period
Administration Guide, Cisco Voice-Mail
Adding Users to Cisco Unified Communications Manager
Managing the User Options Web Pages
Giving Users Access to the User Options Web Pages
Unified Communications Manager System Guide
Click Save Selected/Changes
Specifying Options that Appear on the User Options Web Pages
OL-23874-01
Monitoring the Cisco Unified IP Phone Remotely
Http//IPaddress
Accessing the Web Page for a Phone
Device Information
Disabling and Enabling Web Page Access
UDI
Network Setup
Description
Vlan
Network Statistics
Table below
Device Logs
Message Description Possible Explanation and Action
Status Messages
Adding Phones to the Cisco Unified Communi
Cations Manager Database section on
Message Description Possible Explanation and Action
Message Description Possible Explanation and Action
Streaming Statistics
Streaming Statistics Area Items
Configuring Settings on the Cisco Unified IP Phone chapter
OL-23874-01
Resolving Startup Problems
Troubleshooting and Maintenance
Troubleshooting and Maintenance Resolving Startup Problems
Identifying Error Messages
Cisco CallManager and Tftp Services Are Not Running
Symptom Cisco Unified IP Phone Unable to Obtain IP Address
Verifying Dhcp Settings
Cisco Unified IP Phone Resets Unexpectedly
Verifying the Physical Connection
Identifying Intermittent Network Outages
Verifying the Voice Vlan Configuration
Checking Static IP Address Settings
Verifying that the Phones Have Not Been Intentionally Reset
Eliminating DNS or Other Connectivity Errors
Checking Power Connection
General Troubleshooting Tips
Summary Explanation
Halfduxcollisionexceedthreshold
Phone Configuration Settings section on page 4-2for details
Performing a Basic Reset
Resetting or Restoring the Cisco Unified IP Phone
Performing a Factory Reset
Performing a Basic Reset, Performing a Factory Reset,
Monitoring the Voice Quality of Calls
Using Voice Quality Metrics
Metric Change Condition
Troubleshooting Tips
Cleaning the Cisco Unified IP Phone
Where to Go for More Troubleshooting Information
OL-23874-01
Providing Information to Users Via a Website
How Users Access a Voice Messaging System
How Users Configure Phone Features
Supporting International Users
OL-23874-01
Specification Value or Range
Physical and Operating Environment Specifications
Cable Specifications
Network Port Connector
Network and Access Port Pinouts
Access Port Connector
Pin Number Function
OL-23874-01
Example User Information for These Procedures
Basic Phone Administration Steps
Adding a User From an External Ldap Directory
Proceed to Configuring the Phone section on page D-3
Proceed to the section Configuring the Phone, page D-3
Configuring the Phone
OL-23874-01
OL-23874-01
Click Device Associations
Performing Final End User Configuration Steps
Click Save
OL-23874-01
Installing a Wall Mount for the Cisco Unified IP Phone
Before You Begin
Figure E-2 Preparing the Handset Hookswitch
Network Port on the Phone RJ45 Connector
Installing the Phone on Wall Mount Plate
Figure E-4 RJ45 Connector in the Wall Mount Jack
Figure E-5 Mounting Holes
Firmly slide the IP phone down into place Figure E-6
Phone bracket
Installing the Bracket
Figure E-8 Mounting the Wall Bracket
Figure E-9 Attaching the Phone Bracket
Figure E-10 Preparing the Handset Hookswitch
Figure E-11 Attaching the Cables
Figure E-12 Attaching the Phone to the Wall Bracket
OL-23874-01
ADA Non-Lockable Wall Mount Kit for 6900 Series
Cisco Unified IP Phone Non-Lockable Wall Mount
Package includes these items
Components
Install Non-Lockable Wall Mount Kit for Phone
Figure F-4 Mount the Wall Bracket
Figure F-5 Attach Phone Bracket
Proceed to Before You Begin, page E-2
Remove Phone from Non-Lockable Wall Mount
Figure F-7
Figure F-8
Protocol
Features
Protocol Features
Sccp SIP
OL-23874-01
Numerics
IN-2
IN-3
IN-4
IN-5
IN-6
IN-7
IN-8