SRB Configuration Examples
Access lists are scanned in order. In the following example, the first list denies all entries beginning with the letters ABC, including one named ABCD. This voids the second command, because the entry permitting a name with ABCD comes after the entry denying it.
netbios
Filtering Bridged Token Ring Packets to IBM Machines Example
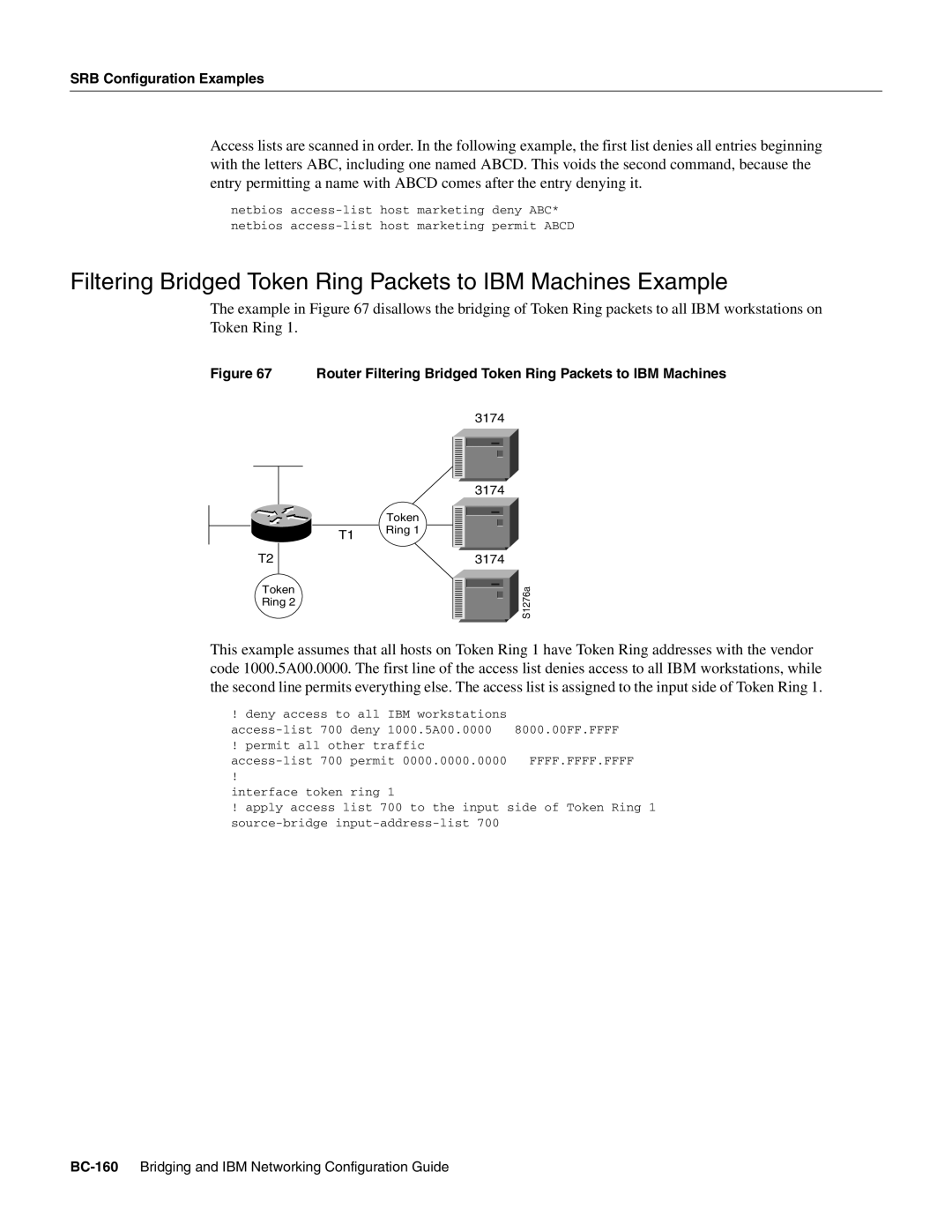
The example in Figure 67 disallows the bridging of Token Ring packets to all IBM workstations on Token Ring 1.
Figure 67 Router Filtering Bridged Token Ring Packets to IBM Machines
T2
Token Ring 2
3174
| 3174 |
| ||||
|
| |||||
| Token |
|
|
|
|
|
|
|
|
|
|
| |
T1 | Ring 1 |
|
|
|
|
|
|
|
|
|
|
| |
|
|
| 3174 |
| ||
|
|
|
|
|
| S1276a |
|
|
|
|
|
| |
|
|
|
|
|
| |
|
|
|
|
|
| |
|
|
|
|
|
| |
|
|
|
|
|
| |
|
|
|
|
|
|
|
This example assumes that all hosts on Token Ring 1 have Token Ring addresses with the vendor code 1000.5A00.0000. The first line of the access list denies access to all IBM workstations, while the second line permits everything else. The access list is assigned to the input side of Token Ring 1.
! deny access to all | IBM workstations |
| |
deny | 1000.5A00.0000 | 8000.00FF.FFFF | |
! permit all other traffic |
| ||
permit 0000.0000.0000 | FFFF.FFFF.FFFF | ||
! |
|
|
|
interface token | ring | 1 |
|
!apply access list 700 to the input side of Token Ring 1