Security Target, Version 3.9 | March 18, 2008 |
|
|
Attackers who are not TOE users: These attackers have no knowledge of how the TOE operates and are assumed to possess a low skill level, a low level of motivation, limited resources to alter TOE configuration settings/parameters, and no physical access to the TOE.
TOE users: These attackers have extensive knowledge of how the TOE operates and are assumed to possess a high skill level, moderate resources to alter TOE configuration settings/parameters, and physical access to the TOE, but no motivation to do so.
The threats are mitigated through the objectives identified in Section 4 - Security Objectives.
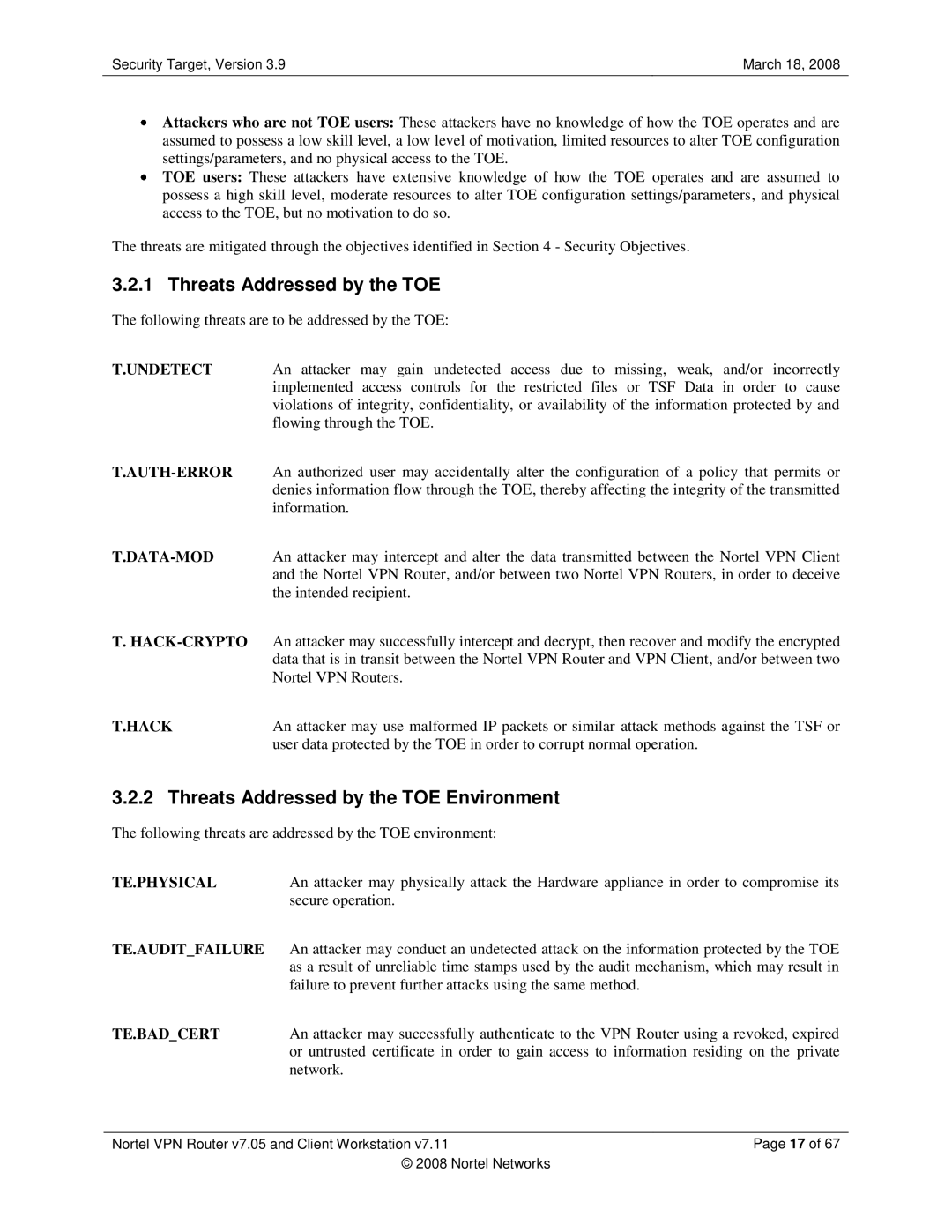
3.2.1 Threats Addressed by the TOE
The following threats are to be addressed by the TOE:
T.UNDETECT An attacker may gain undetected access due to missing, weak, and/or incorrectly implemented access controls for the restricted files or TSF Data in order to cause violations of integrity, confidentiality, or availability of the information protected by and flowing through the TOE.
T.
T.HACK | An attacker may use malformed IP packets or similar attack methods against the TSF or |
| user data protected by the TOE in order to corrupt normal operation. |
3.2.2 Threats Addressed by the TOE Environment
The following threats are addressed by the TOE environment:
TE.PHYSICAL | An attacker may physically attack the Hardware appliance in order to compromise its | |
| secure operation. |
|
TE.AUDIT_FAILURE | An attacker may conduct an undetected attack on the information protected by the TOE | |
| as a result of unreliable time stamps used by the audit mechanism, which may result in | |
| failure to prevent further attacks using the same method. |
|
TE.BAD_CERT | An attacker may successfully authenticate to the VPN Router using a revoked, expired | |
| or untrusted certificate in order to gain access to information residing on the private | |
| network. |
|
|
| |
Nortel VPN Router v7.05 and Client Workstation v7.11 | Page 17 of 67 | |
| © 2008 Nortel Networks |
|