Security Target, Version 3.9 | March 18, 2008 |
|
|
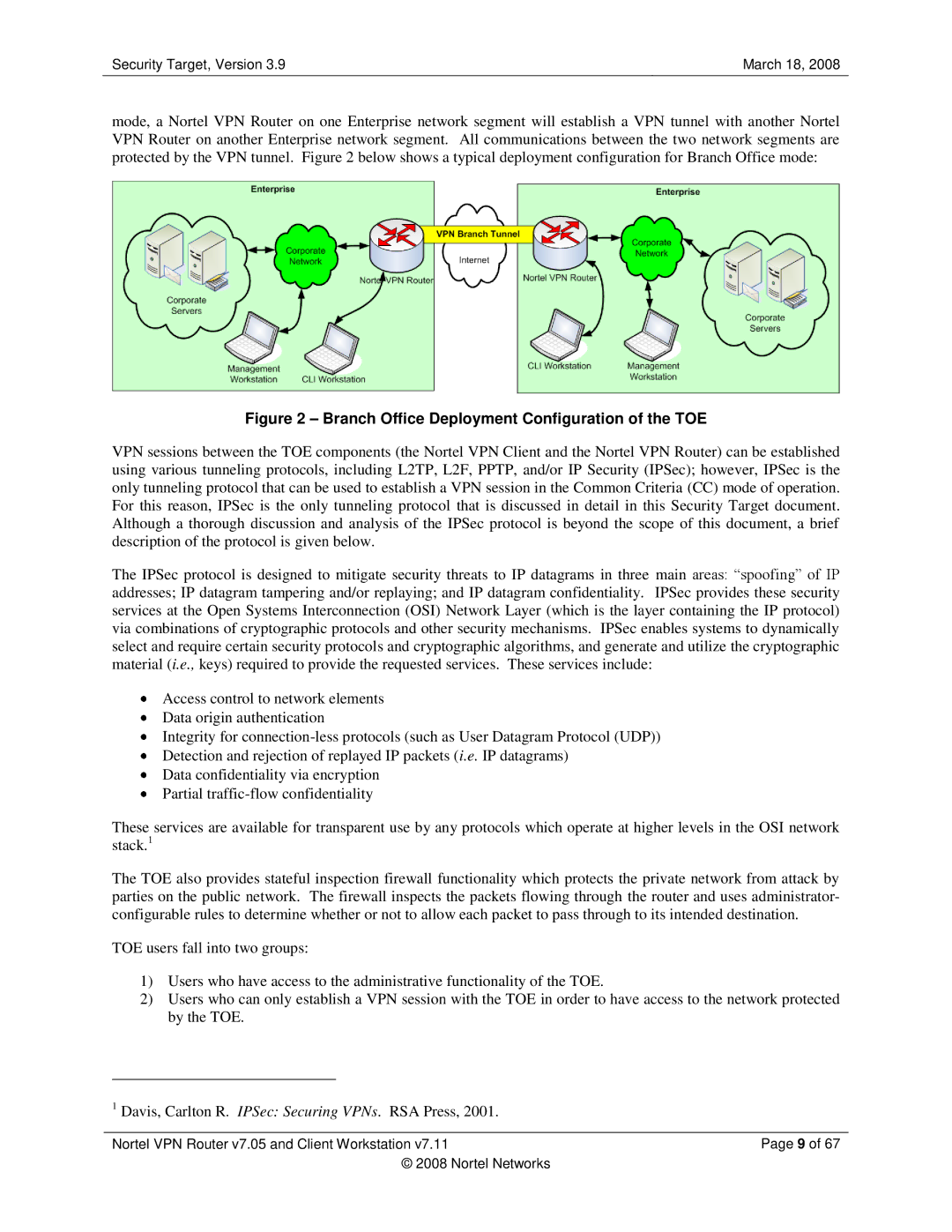
mode, a Nortel VPN Router on one Enterprise network segment will establish a VPN tunnel with another Nortel VPN Router on another Enterprise network segment. All communications between the two network segments are protected by the VPN tunnel. Figure 2 below shows a typical deployment configuration for Branch Office mode:
Figure 2 – Branch Office Deployment Configuration of the TOE
VPN sessions between the TOE components (the Nortel VPN Client and the Nortel VPN Router) can be established using various tunneling protocols, including L2TP, L2F, PPTP, and/or IP Security (IPSec); however, IPSec is the only tunneling protocol that can be used to establish a VPN session in the Common Criteria (CC) mode of operation. For this reason, IPSec is the only tunneling protocol that is discussed in detail in this Security Target document. Although a thorough discussion and analysis of the IPSec protocol is beyond the scope of this document, a brief description of the protocol is given below.
The IPSec protocol is designed to mitigate security threats to IP datagrams in three main areas: “spoofing” of IP addresses; IP datagram tampering and/or replaying; and IP datagram confidentiality. IPSec provides these security services at the Open Systems Interconnection (OSI) Network Layer (which is the layer containing the IP protocol) via combinations of cryptographic protocols and other security mechanisms. IPSec enables systems to dynamically select and require certain security protocols and cryptographic algorithms, and generate and utilize the cryptographic material (i.e., keys) required to provide the requested services. These services include:
Access control to network elements
Data origin authentication
Integrity for
Detection and rejection of replayed IP packets (i.e. IP datagrams)
Data confidentiality via encryption
Partial
These services are available for transparent use by any protocols which operate at higher levels in the OSI network stack.1
The TOE also provides stateful inspection firewall functionality which protects the private network from attack by parties on the public network. The firewall inspects the packets flowing through the router and uses administrator- configurable rules to determine whether or not to allow each packet to pass through to its intended destination.
TOE users fall into two groups:
1)Users who have access to the administrative functionality of the TOE.
2)Users who can only establish a VPN session with the TOE in order to have access to the network protected by the TOE.
1 Davis, Carlton R. IPSec: Securing VPNs. RSA Press, 2001.
Nortel VPN Router v7.05 and Client Workstation v7.11 | Page 9 of 67 |
© 2008 Nortel Networks |
|