Nortel Networks Corsec Security, Inc
Version Modification Date Modified By Description of Changes
Revision History
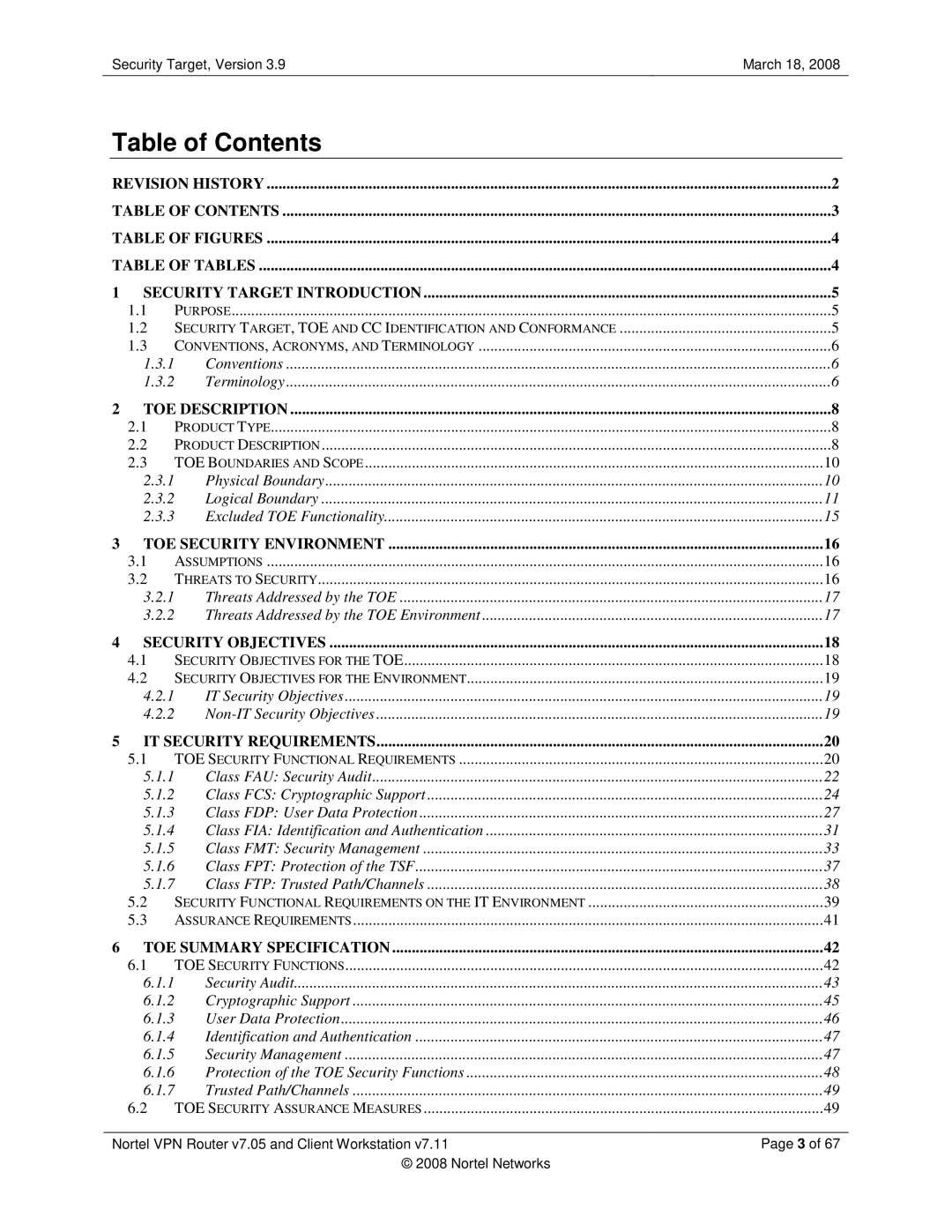
Table of Contents
Rationale
Table of Figures
Table of Tables
Protection Profile Claims
ST, TOE, and CC Identification and Conformance
Security Target Introduction
Purpose
Security Target, TOE and CC Identification and Conformance
Terminology
Conventions, Acronyms, and Terminology
Conventions
Terminology
Primary Admin password
TOE Description
Product Type
Product Description
Branch Office Deployment Configuration of the TOE
Physical Boundary
TOE Boundaries and Scope
TOE Environment
Logical Boundary
Enterprise
World
Security Audit
Cryptographic Support
User Data Protection
Trusted Path/Channels
Identification and Authentication
Security Management
Protection of the TOE Security Functions
Excluded TOE Functionality
TOE Security Environment
Assumptions
Threats to Security
Threats Addressed by the TOE Environment
Threats Addressed by the TOE
Security Objectives for the TOE
Security Objectives
OE.TIME
Security Objectives for the Environment
IT Security Objectives
Non-IT Security Objectives
ST Operation
IT Security Requirements
TOE Security Functional Requirements
TOE Security Functional Requirements
Description ST Operation
Auditable Events
Class FAU Security Audit
FAUGEN.1 Audit Data Generation
FAUSAR.1 Audit review
Dependencies FAUGEN.1 Audit data generation
FCSCKM.4 Cryptographic key destruction
Class FCS Cryptographic Support
FCSCKM.1a Cryptographic key generation Diffie-Hellman
FCSCKM.1b Cryptographic key generation RSA
FCSCOP.1b Cryptographic operation authentication
FCSCOP.1d Cryptographic operation random number generation
FCSCOP.1e Cryptographic operation hashing
Security Target, Version March 18
FDPIFC.2a Complete information flow control VPN
FDPACC.2 Complete access control
FDPACF.1 Security attribute based access control
Class FDP User Data Protection
FDPIFF.1a Simple security attributes VPN
FDPIFC.2b Complete information flow control Firewall
FDPIFF.1b Simple security attributes Firewall
FDPUIT.1.1
FDPUCT.1 Basic data exchange confidentiality
FDPUIT.1 Data exchange integrity
FDPUCT.1.1
FIAUID.2 User identification before any action
Class FIA Identification and Authentication
FIAUAU.1 Timing of authentication
FIAUAU.5 Multiple authentication mechanisms
Dependencies No dependencies
FMTMSA.1a Management of security attributes
Class FMT Security Management
FMTMOF.1a Management of security functions behaviour
FMTMOF.1b Management of security functions behaviour
FMTMSA.2.1
FMTMSA.1c Management of security attributes
FMTMSA.2 Secure security attributes
FMTMSA.3a Static attribute initialisation
FMTSMR.1 Security roles
FMTSMF.1 Specification of Management Functions
FMTMSA.3b Static attribute initialisation
FMTMSA.3c Static attribute initialisation
FMTSMR.1.2
FPTRPL.1 Replay detection
FPTAMT.1 Abstract machine testing
FPTTST.1 TSF testing
Class FPT Protection of the TSF
FTPTRP.1.2
Class FTP Trusted Path/Channels
FTPTRP.1 Trusted path
FTPTRP.1.1
FPTSTM.1 Reliable time stamps
Security Functional Requirements on the IT Environment
FPTRVM.1 Non-bypassability of the TSP
FPTSEP.1 TSF domain separation
Security Target, Version 3.9March 18
Assurance Requirements
Assurance Components
Assurance Requirements
Description Function
TOE Summary Specification
TOE Security Functions
TOE Security
Security Log
Configuration Log
Security Audit
Accounting Logs
Event Log
System Log
Validation Modules Fips 140-2 Certificate #
Cryptographic Support
Fips Validated Modules
FIPS-Validated Cryptographic Algorithms
User Data Protection
Security Management
Identification and Authentication
Power-Up Self-Tests
Protection of the TOE Security Functions
Conditional Self-Tests
Assurance Assurance Measure Component
TOE Security Assurance Measures
Trusted Path/Channels
TOE Security Functional Requirements Satisfied FTPTRP.1
Augmentation to EAL 4+ assurance level
Protection Profile Reference
Protection Profile Claims
TOE Objectives Environmental Objectives Non-IT
Rationale
Security Objectives Rationale
Relationship of Security Threats to Objectives
Hack
Certificate
OE.CERTIFICATE
Security Functional Requirements Rationale
Objectives Requirements
Relationship of Security Requirements to Objectives
Env
Functions and data
FMTMSA.3a,b,c
Able to access such functionality
Integrity
Reject packets based on their attributes
Functional Requirements Dependencies
Security Assurance Requirements Rationale
Rationale for Strength of Function
Dependency Rationale
FCSCOP.1
TOE Summary Specification Rationale
Configuration Management
Secure Delivery and Operation
Development
Guidance Documentation
Life Cycle Support Documents
Tests
Vulnerability and TOE Strength of Function Analyses
Strength of Function
DoD
Acronyms
Acronyms
Acronym Definition
SHA