Security Target, Version 3.9March 18, 2008
| authorized users with the ability to verify the integrity of TSF Data and TSF executable code | |
| [FPT_AMT.1 and FPT_TST.1]. | |
OE.TIME | The environment must provide reliable timestamps for the | |
| Time stamps associated with an audit record must be reliable [FPT_STM.1]. | |
OE.PROTECT | The environment must protect the TOE from interference and tampering by untrusted | |
| subjects. | |
| The IT Environment must protect the TOE from intentional attacks and unintentional interference | |
| [FPT_SEP.1]. | |
OE.NONBYPASS | The environment must ensure that TSP enforcement functions are invoked and | |
| succeed before each function within the TSC is allowed to proceed. | |
The IT Environment must ensure that the TOE receives reliable time information for time stamps from the Environment [FPT_RVM.1], and only receives it from an authorized and reliable source [FPT_STM.1].
8.3 Security Assurance Requirements Rationale
EAL 4+ was chosen to provide a basic level of independently assured security and thorough investigation of the TOE and its development. As such, minimal additional tasks are placed upon the vendor assuming the vendor follows reasonable software engineering practices and can provide support to the evaluation for design and testing efforts. The chosen assurance level is appropriate with the threats defined for the environment. While the TOE may operate in a hostile environment, it is expected to be protected by other products and processes designed to address threats that correspond with the intended environment. At EAL 4+, the TOE will have incurred an independent vulnerability analysis to support its introduction into the hostile environment.
The augmentation of ALC_FLR.2 was chosen to give greater assurance of the developer’s
8.4 Rationale for Strength of Function
The TOE minimum strength of function is
8.5 Dependency Rationale
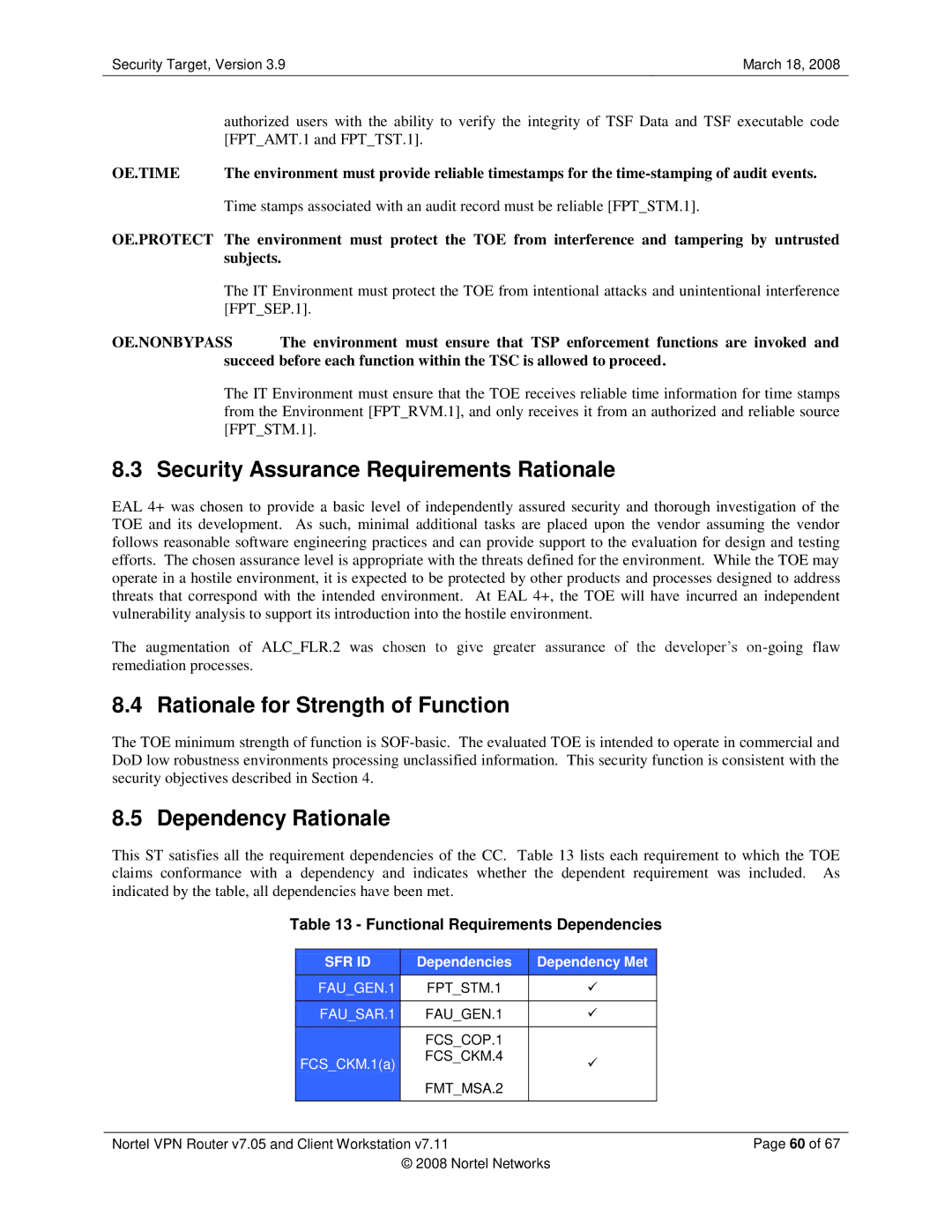
This ST satisfies all the requirement dependencies of the CC. Table 13 lists each requirement to which the TOE claims conformance with a dependency and indicates whether the dependent requirement was included. As indicated by the table, all dependencies have been met.
Table 13 - Functional Requirements Dependencies
| SFR ID |
| Dependencies |
| Dependency Met |
|
|
|
|
| |||
|
|
|
|
|
|
|
| FAU_GEN.1 |
| FPT_STM.1 |
| |
|
|
|
|
| |||
|
|
|
|
|
|
|
| FAU_SAR.1 |
| FAU_GEN.1 |
| |
|
|
|
|
| |||
|
|
|
|
|
|
|
|
|
| FCS_COP.1 |
|
|
|
| FCS_CKM.1(a) |
| FCS_CKM.4 |
| |
|
|
|
|
| |||
|
|
|
|
| ||
|
|
| FMT_MSA.2 |
|
|
|
|
|
|
|
|
| |
|
|
|
|
|
|
|
Nortel VPN Router v7.05 and Client Workstation v7.11 |
|
| Page 60 of 67 | |||
|
| © 2008 Nortel Networks | ||||