Security Target, Version 3.9 | March 18, 2008 |
|
|
1 Security Target Introduction
This section identifies the Security Target (ST), Target of Evaluation (TOE) identification, ST conventions, ST conformance claims, and the ST organization. The Targets of Evaluation are models 600, 1010, 1050, 1100, 1750, 2750, and 5000 of the Nortel VPN Router v7.05 and Client Workstation v7.11. These devices are functionally identical and will hereafter be referred to, collectively, as “the TOE” throughout this document. The TOE is a Virtual Private Network (VPN) Router that ensures
1.1 Purpose
This ST contains the following sections to provide mapping of the Security Environment to the Security Requirements that the TOE meets in order to remove, diminish, or mitigate the defined threats:
Security Target Introduction (Section 1) – Provides a brief summary of the content of the ST and describes the organization of other sections of this document.
TOE Description (Section 2) – Provides an overview of the TOE security functions and describes the physical and logical boundaries for the TOE.
TOE Security Environment (Section 3) – Describes the threats and assumptions that pertain to the TOE and its environment.
Security Objectives (Section 4) – Identifies the security objectives that are satisfied by the TOE and its environment.
IT Security Requirements (Section 5) – Presents the Security Functional Requirements (SFRs) and Security Assurance Requirements (SARs) met by the TOE and by the TOE’s environment.
TOE Summary Specification (Section 6) – Describes the security functions provided by the TOE to satisfy the security requirements and objectives.
Protection Profile Claims (Section 7) – Provides the identification of any ST Protection Profile claims as well as a justification to support such claims.
Rationale (Section 8) – Presents the rationale for the security objectives, requirements, and the TOE summary specifications as to their consistency, completeness, and suitability.
Acronyms (Section 9) – Defines the acronyms used within this ST.
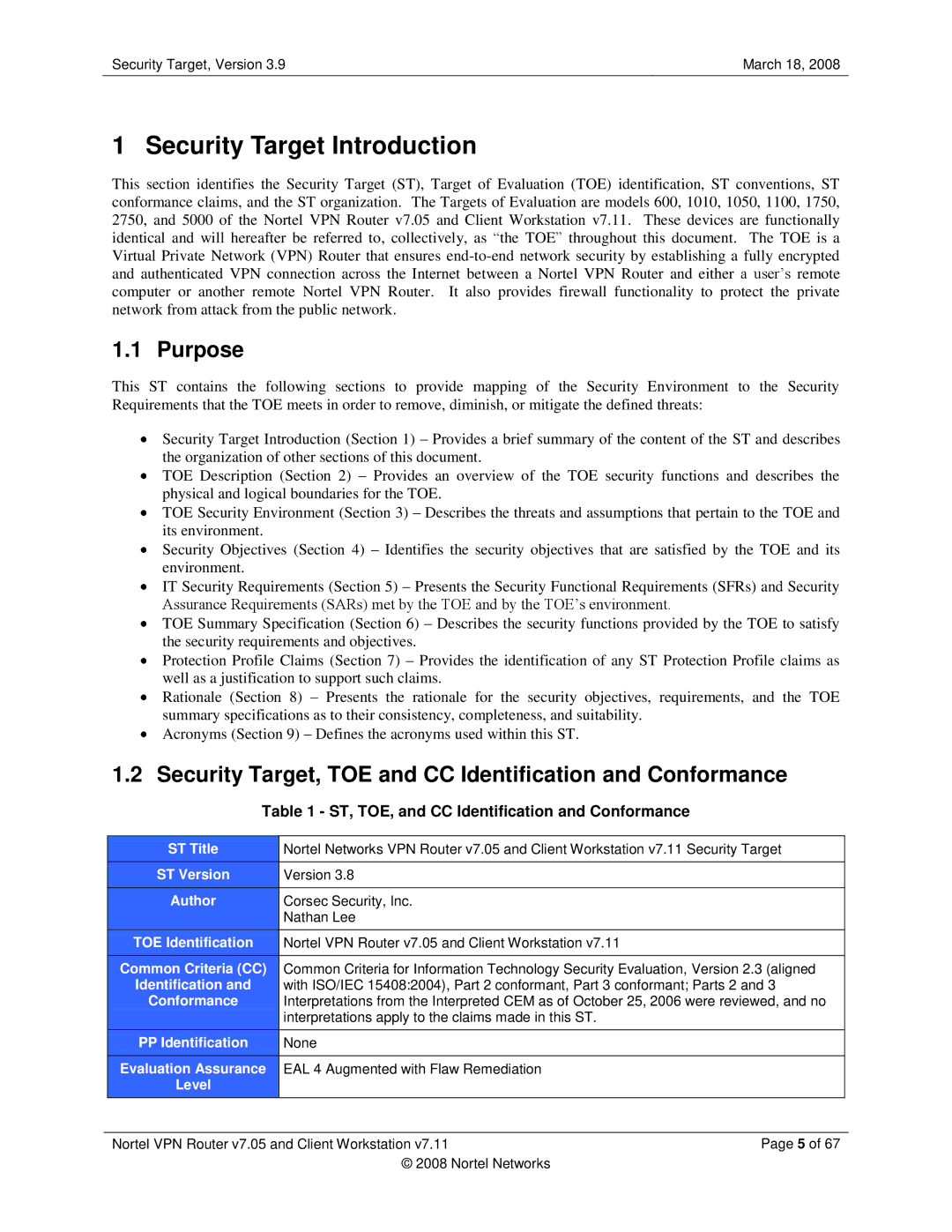
1.2 Security Target, TOE and CC Identification and Conformance
| Table 1 - ST, TOE, and CC Identification and Conformance |
|
| |
|
|
|
| |
| ST Title | Nortel Networks VPN Router v7.05 and Client Workstation v7.11 Security Target |
| |
| ST Version | Version 3.8 |
|
|
|
|
|
|
|
| Author | Corsec Security, Inc. |
|
|
|
| Nathan Lee |
|
|
|
|
|
|
|
|
|
|
|
|
| TOE Identification | Nortel VPN Router v7.05 and Client Workstation v7.11 |
|
|
| Common Criteria (CC) | Common Criteria for Information Technology Security Evaluation, Version 2.3 (aligned |
| |
| Identification and | with ISO/IEC 15408:2004), Part 2 conformant, Part 3 conformant; Parts 2 and 3 |
| |
| Conformance | Interpretations from the Interpreted CEM as of October 25, 2006 were reviewed, and no |
| |
|
| interpretations apply to the claims made in this ST. |
|
|
| PP Identification | None |
|
|
|
|
|
|
|
| Evaluation Assurance | EAL 4 Augmented with Flaw Remediation |
|
|
| Level |
|
|
|
|
|
|
|
|
|
|
|
|
|
| Nortel VPN Router v7.05 and Client Workstation v7.11 | Page 5 of 67 | ||
|
| © 2008 Nortel Networks |
|
|