Administering
Troubleshooting
If the output shows ldap is not being searched, check /etc/nsswitch.conf to make sure ldap is specified. If username is not found, make sure that user is in the directory and, if using a proxy user, make sure the proxy user is properly configured.
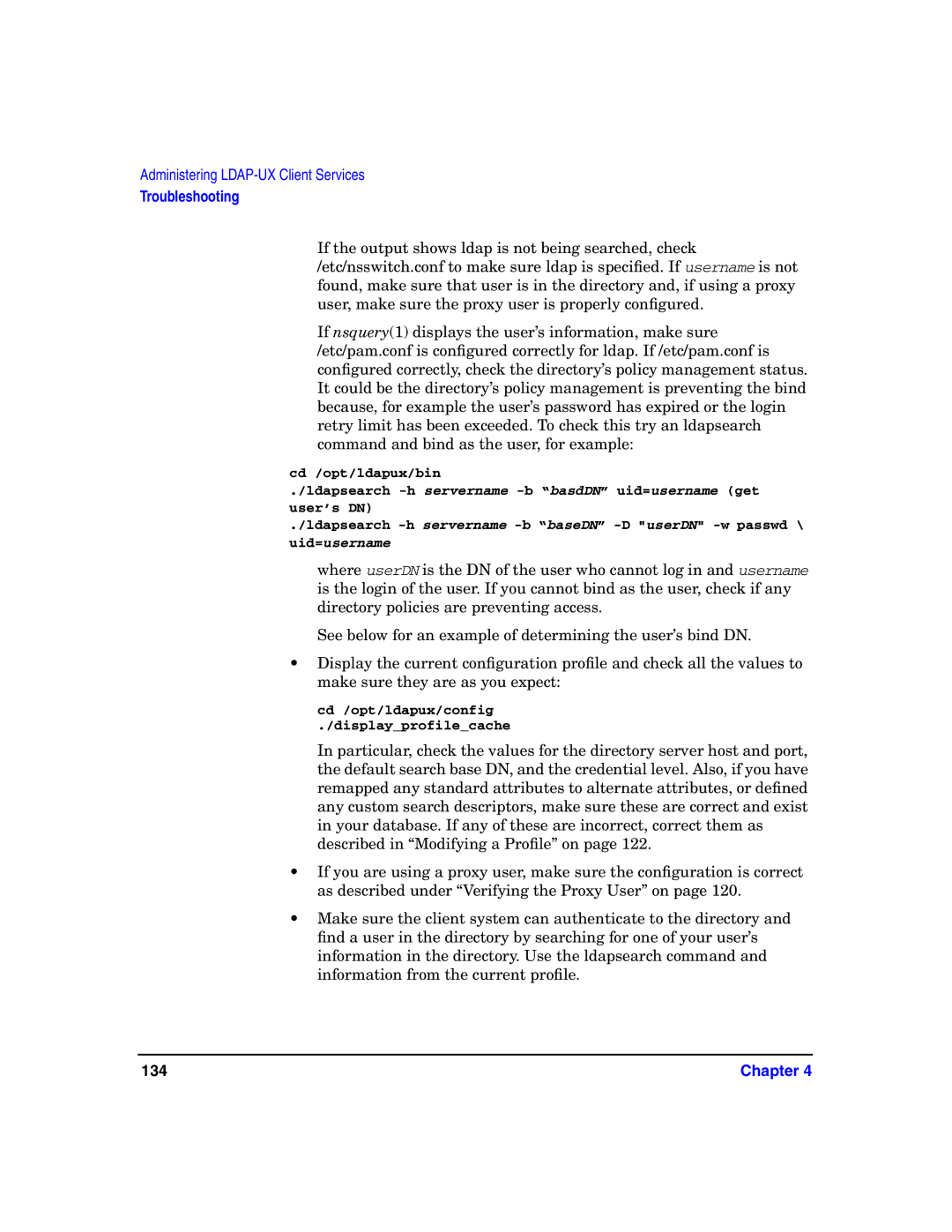
If nsquery(1) displays the user’s information, make sure /etc/pam.conf is configured correctly for ldap. If /etc/pam.conf is configured correctly, check the directory’s policy management status. It could be the directory’s policy management is preventing the bind because, for example the user’s password has expired or the login retry limit has been exceeded. To check this try an ldapsearch command and bind as the user, for example:
cd /opt/ldapux/bin
./ldapsearch
./ldapsearch
where userDN is the DN of the user who cannot log in and username is the login of the user. If you cannot bind as the user, check if any directory policies are preventing access.
See below for an example of determining the user’s bind DN.
•Display the current configuration profile and check all the values to make sure they are as you expect:
cd /opt/ldapux/config
./display_profile_cache
In particular, check the values for the directory server host and port, the default search base DN, and the credential level. Also, if you have remapped any standard attributes to alternate attributes, or defined any custom search descriptors, make sure these are correct and exist in your database. If any of these are incorrect, correct them as described in “Modifying a Profile” on page 122.
•If you are using a proxy user, make sure the configuration is correct as described under “Verifying the Proxy User” on page 120.
•Make sure the client system can authenticate to the directory and find a user in the directory by searching for one of your user’s information in the directory. Use the ldapsearch command and information from the current profile.
134 | Chapter 4 |