|
|
|
|
|
|
| Features in |
|
|
| 47 | ||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
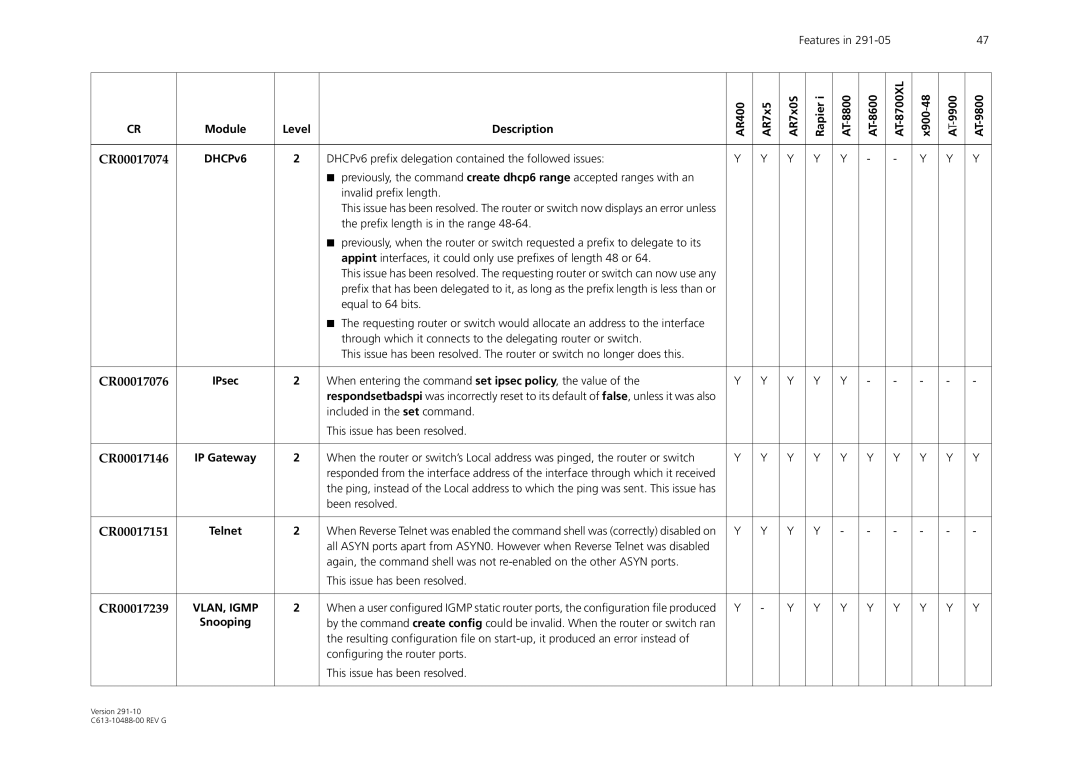
CR | Module | Level | Description | AR400 | AR7x5 | AR7x0S |
| Rapier i | AT8800- |
| x90048- | ||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
CR00017074 | DHCPv6 | 2 | DHCPv6 prefix delegation contained the followed issues: | Y | Y | Y |
| Y | Y | - |
| - | Y | Y | Y |
|
|
| ■ previously, the command create dhcp6 range accepted ranges with an |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| invalid prefix length. |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| This issue has been resolved. The router or switch now displays an error unless |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| the prefix length is in the range |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| ■ previously, when the router or switch requested a prefix to delegate to its |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| appint interfaces, it could only use prefixes of length 48 or 64. |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| This issue has been resolved. The requesting router or switch can now use any |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| prefix that has been delegated to it, as long as the prefix length is less than or |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| equal to 64 bits. |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| ■ The requesting router or switch would allocate an address to the interface |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| through which it connects to the delegating router or switch. |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| This issue has been resolved. The router or switch no longer does this. |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
CR00017076 | IPsec | 2 | When entering the command set ipsec policy, the value of the | Y | Y | Y |
| Y | Y | - |
| - | - | - | - |
|
|
| respondsetbadspi was incorrectly reset to its default of false, unless it was also |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| included in the set command. |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| This issue has been resolved. |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
CR00017146 | IP Gateway | 2 | When the router or switch’s Local address was pinged, the router or switch | Y | Y | Y |
| Y | Y | Y |
| Y | Y | Y | Y |
|
|
| responded from the interface address of the interface through which it received |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| the ping, instead of the Local address to which the ping was sent. This issue has |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| been resolved. |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
CR00017151 | Telnet | 2 | When Reverse Telnet was enabled the command shell was (correctly) disabled on | Y | Y | Y |
| Y | - | - |
| - | - | - | - |
|
|
| all ASYN ports apart from ASYN0. However when Reverse Telnet was disabled |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| again, the command shell was not |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| This issue has been resolved. |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
CR00017239 | VLAN, IGMP | 2 | When a user configured IGMP static router ports, the configuration file produced | Y | - | Y |
| Y | Y | Y |
| Y | Y | Y | Y |
| Snooping |
| by the command create config could be invalid. When the router or switch ran |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| the resulting configuration file on |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| configuring the router ports. |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| This issue has been resolved. |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Version