6
Configuring Port-Based Access Control (802.1x)
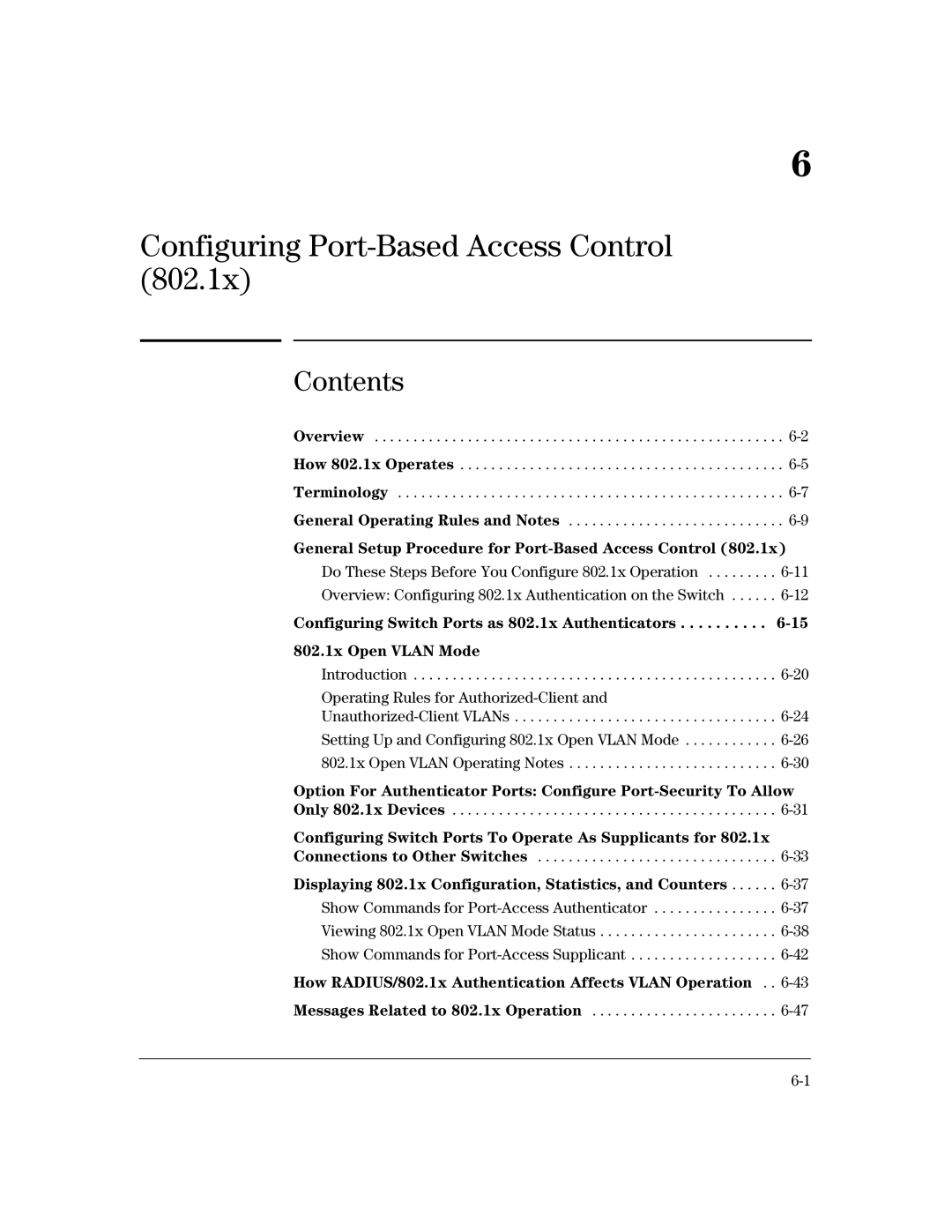
Contents
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
How 802.1x Operates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
Terminology . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
General Operating Rules and Notes . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-9
General Setup Procedure for Port-Based Access Control (802.1x)
Do These Steps Before You Configure 802.1x Operation . . . . . . . . .
Overview: Configuring 802.1x Authentication on the Switch . . . . . .
Configuring Switch Ports as 802.1x Authenticators . . . . . . . . . .
802.1x Open VLAN Mode
Introduction . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
Operating Rules for
Option For Authenticator Ports: Configure
Configuring Switch Ports To Operate As Supplicants for 802.1x Connections to Other Switches . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
Displaying 802.1x Configuration, Statistics, and Counters . . . . . .
How RADIUS/802.1x Authentication Affects VLAN Operation . .