Configuring Secure Shell (SSH)
Configuring the Switch for SSH Operation
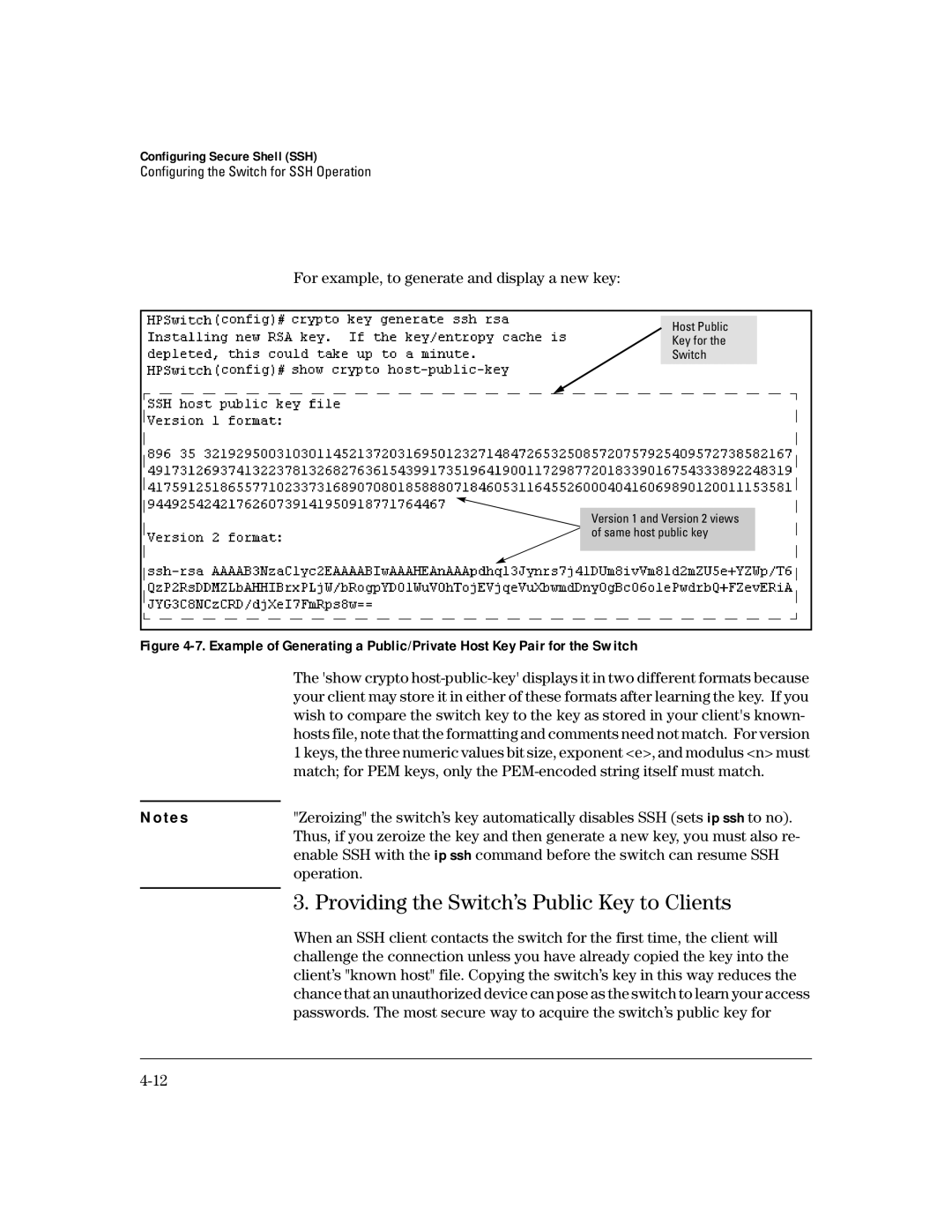
For example, to generate and display a new key:
Host Public
Key for the
Switch
Version 1 and Version 2 views of same host public key
Figure 4-7. Example of Generating a Public/Private Host Key Pair for the Switch
The 'show crypto
N o t e s | "Zeroizing" the switch’s key automatically disables SSH (sets ip ssh to no). |
| Thus, if you zeroize the key and then generate a new key, you must also re- |
| enable SSH with the ip ssh command before the switch can resume SSH |
| operation. |
| 3. Providing the Switch’s Public Key to Clients |
| |
| When an SSH client contacts the switch for the first time, the client will |
| challenge the connection unless you have already copied the key into the |
| client’s "known host" file. Copying the switch’s key in this way reduces the |
| chance that an unauthorized device can pose as the switch to learn your access |
| passwords. The most secure way to acquire the switch’s public key for |