Configuring and Monitoring Port Security
Port Security Command Options and Operation
For information on the individual control parameters, see the Port Security Parameter table on page
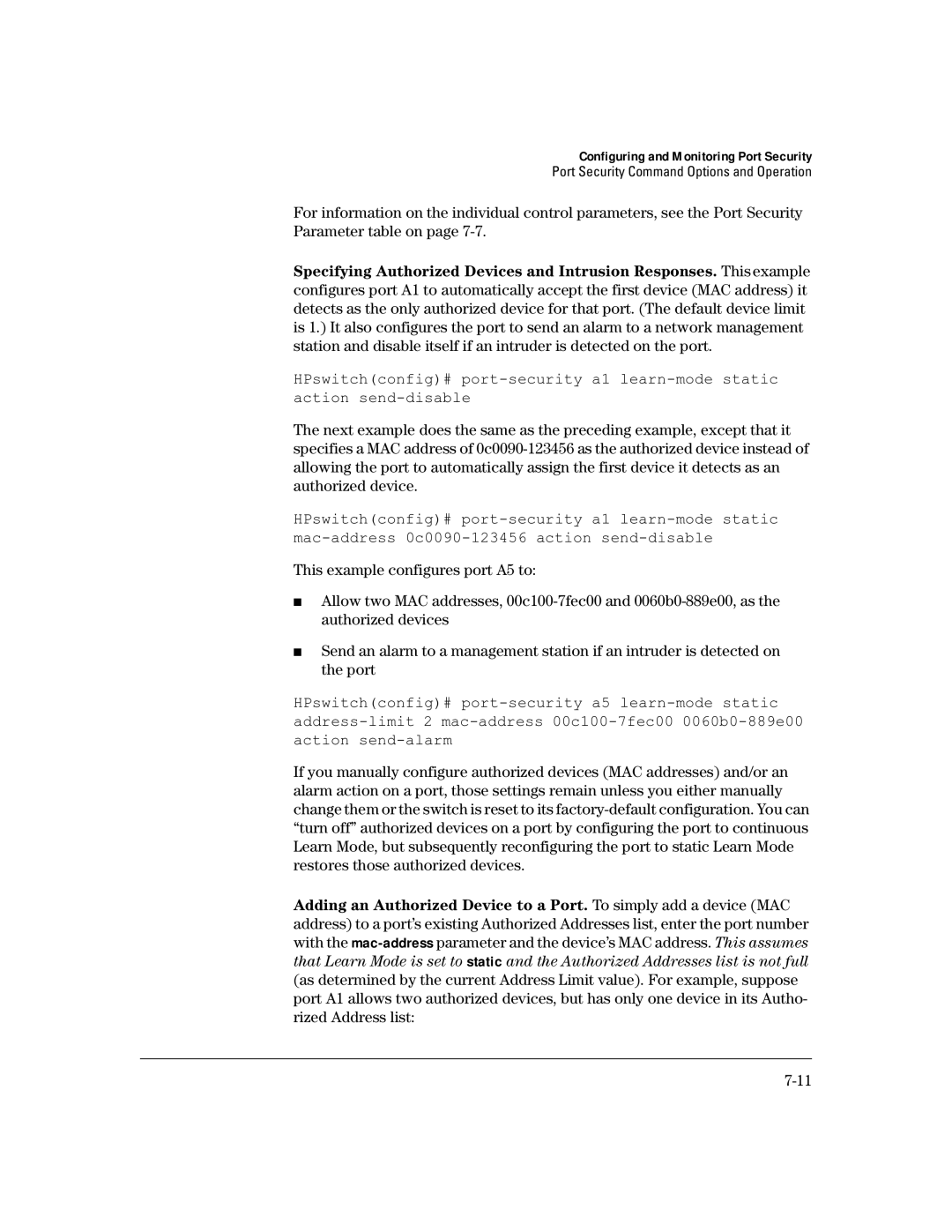
Specifying Authorized Devices and Intrusion Responses. This example configures port A1 to automatically accept the first device (MAC address) it detects as the only authorized device for that port. (The default device limit is 1.) It also configures the port to send an alarm to a network management station and disable itself if an intruder is detected on the port.
HPswitch(config)#
The next example does the same as the preceding example, except that it specifies a MAC address of
HPswitch(config)#
This example configures port A5 to:
■Allow two MAC addresses,
■Send an alarm to a management station if an intruder is detected on the port
HPswitch(config)#
If you manually configure authorized devices (MAC addresses) and/or an alarm action on a port, those settings remain unless you either manually change them or the switch is reset to its
Adding an Authorized Device to a Port. To simply add a device (MAC address) to a port’s existing Authorized Addresses list, enter the port number with the