Configuring Secure Shell (SSH)
Public Key Formats
Public Key Formats
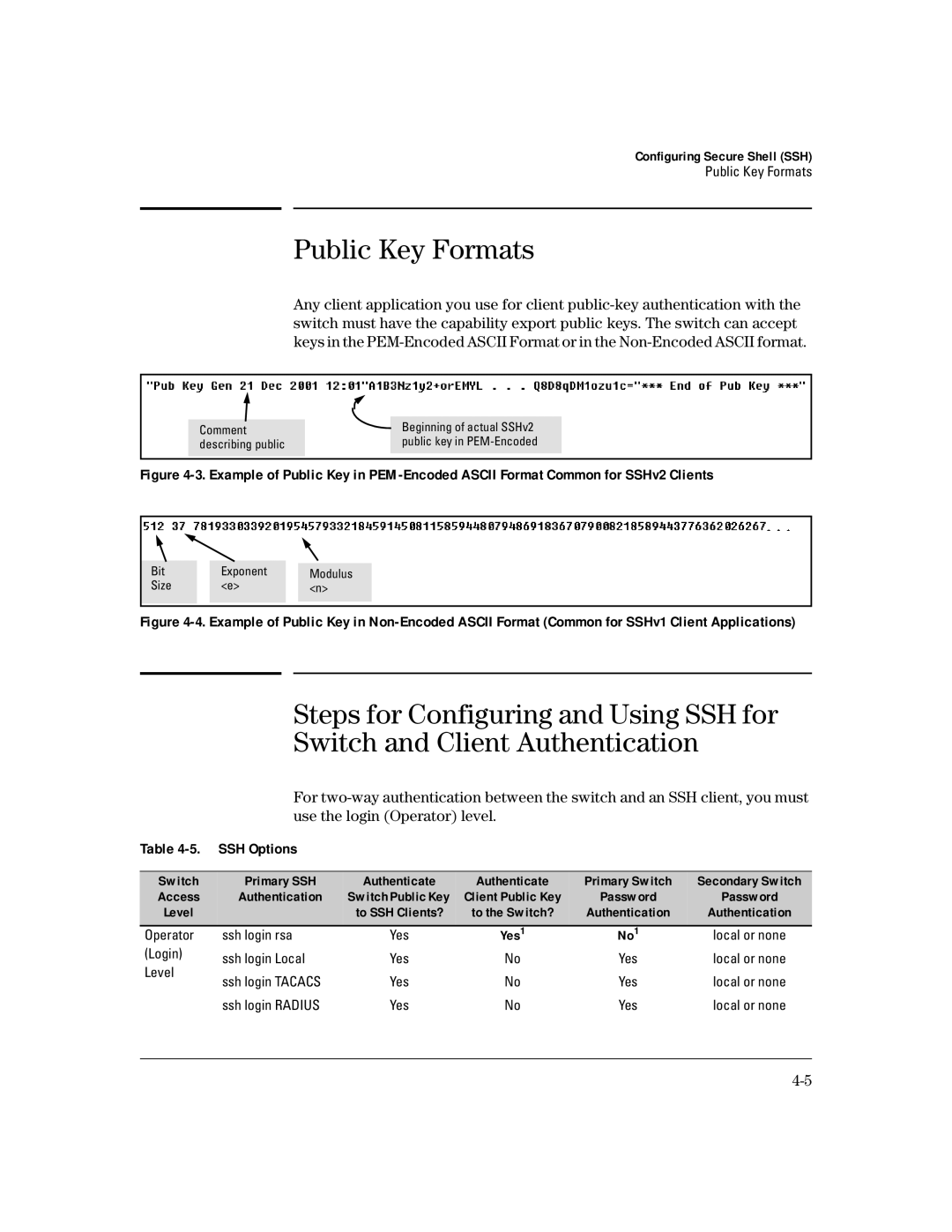
Any client application you use for client
|
|
|
|
|
|
|
| Beginning of actual SSHv2 |
|
| Comment |
|
| |
| describing public |
| public key in |
|
|
|
|
|
|
Figure 4-3. Example of Public Key in PEM-Encoded ASCII Format Common for SSHv2 Clients
|
|
|
|
|
|
Bit |
| Exponent |
|
|
|
|
| Modulus |
| ||
Size |
| <e> |
| <n> |
|
|
|
|
|
|
|
|
|
|
|
|
|
Figure 4-4. Example of Public Key in Non-Encoded ASCII Format (Common for SSHv1 Client Applications)
Steps for Configuring and Using SSH for
Switch and Client Authentication
For
Table | SSH Options |
|
|
|
| |
|
|
|
|
|
| |
Switch | Primary SSH | Authenticate | Authenticate | Primary Switch | Secondary Switch | |
Access | Authentication | Switch Public Key | Client Public Key | Password | Password | |
Level |
| to SSH Clients? | to the Switch? | Authentication | Authentication | |
Operator | ssh login rsa | Yes | Yes1 | No1 | local or none | |
(Login) | ssh login Local | Yes | No | Yes | local or none | |
Level | ||||||
ssh login TACACS | Yes | No | Yes | local or none | ||
| ||||||
| ssh login RADIUS | Yes | No | Yes | local or none |